Social Engineering Statistics [2026]: 100+ Facts & Trends

68% of confirmed breaches involve the human element. Not a firewall misconfiguration. Not an unpatched server. A person clicking, trusting, or responding to something they shouldn't have (Verizon DBIR 2025). Social engineering losses hit $16.6 billion in 2024 (FBI IC3). Vishing surged 442% in six months (CrowdStrike). AI now powers over 80% of phishing campaigns (Abnormal Security). The attackers aren't breaking in — they're being invited in.
Below you'll find 76+ social engineering statistics across 14 sections — covering phishing, vishing, BEC, pretexting, AI-powered attacks, and what actually works to stop them. Sourced from Verizon, FBI IC3, KnowBe4, CrowdStrike, IBM, and 30+ reports. Each section includes original analysis that cross-references the data to surface what no single report shows you.
Key Social Engineering Statistics at a Glance
- 98% of cyberattacks involve social engineering (Sprinto)
- $16.6 billion in FBI-reported US social engineering losses in 2024 (+33% YoY)
- 442% surge in vishing attacks H1 to H2 2024 (CrowdStrike)
- 80%+ of social engineering is now AI-powered (Abnormal Security)
- $4.89M average cost per BEC breach (IBM 2025)
- 33.1% of untrained employees click phishing links (KnowBe4 2025)
- 86% reduction in click rates after 12 months of training (KnowBe4)
- 60%+ of phishing engagements are now vishing (Keepnet 2025)
Last updated: May 2026
📊 Key Social Engineering Numbers (2026)
Social engineering is the dominant attack vector in cybersecurity. 98% of cyberattacks involve some form of social engineering (Sprinto), and 68% of attacks originate from email (KnowBe4 2025). The human element is involved in 60% of all breaches (Verizon DBIR 2025), ranging from phishing clicks to credential reuse to pretexting conversations that trick employees into authorizing fraudulent transfers.
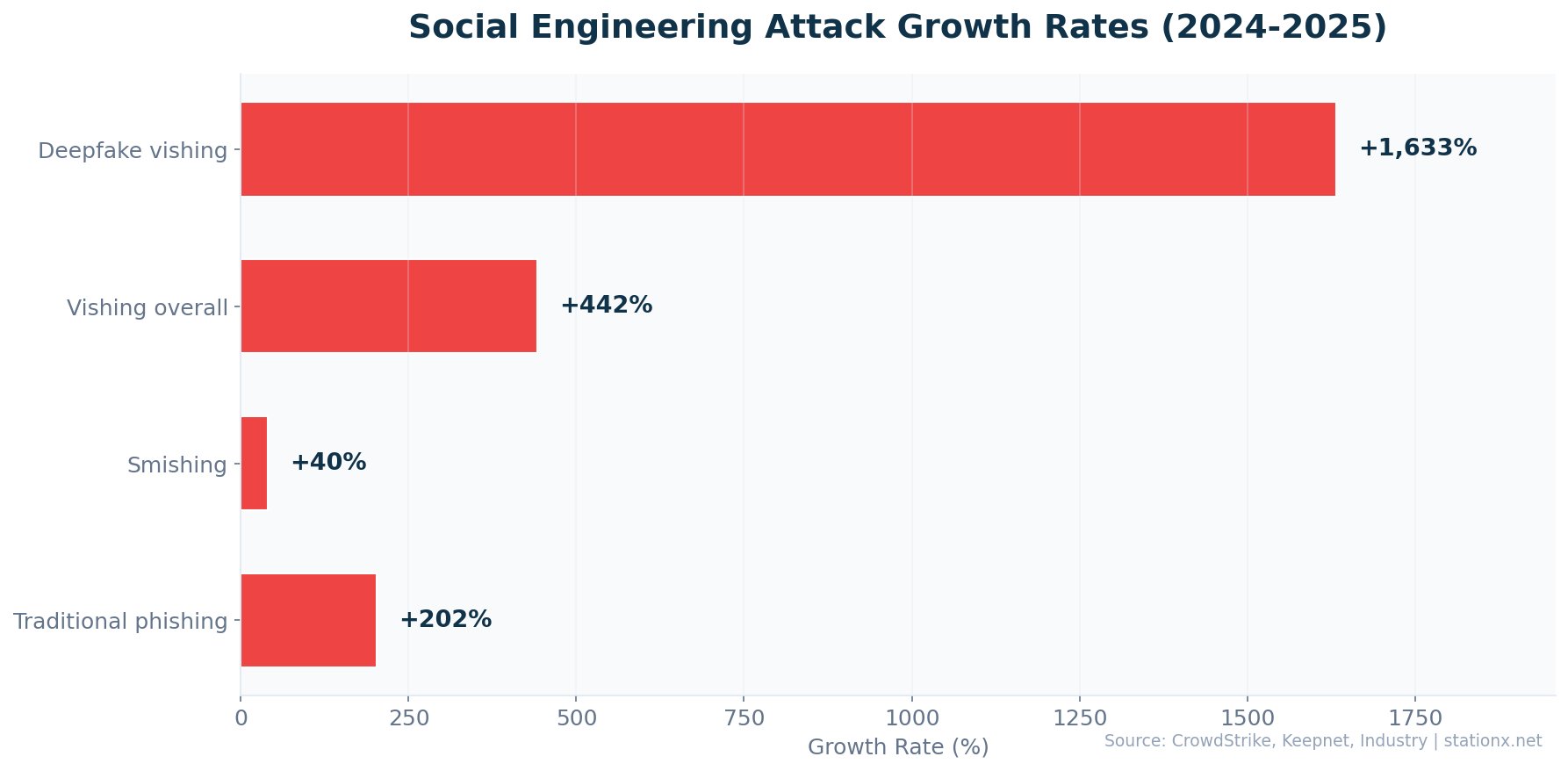
The scale is accelerating. FBI-reported US social engineering losses grew 33% year-over-year in 2024 to record highs (FBI IC3). Vishing attacks surged 442% (CrowdStrike 2025). AI now powers over 80% of social engineering activity (Abnormal Security). 91% of security professionals report encountering AI-enabled email attacks in the past 6 months. Yet security awareness training reduces phishing click rates by 86% within 12 months (KnowBe4 2025) — the gap between problem and solution is a training gap, not a technology gap.
Social engineering is not a new threat, but AI has transformed its economics. Prior to 2023, creating a convincing phishing campaign required skilled operators who understood language, psychology, and target context. Now, AI tools can generate perfect phishing emails in any language at 95% lower cost (HBR 2024), clone a voice from 3 seconds of audio (McAfee 2024), and produce deepfake video calls that fooled a finance team into transferring $25 million (CrowdStrike 2024). The barrier to entry for social engineering has collapsed. The data below charts this transformation.
| Finding | Value | Source |
|---|---|---|
| Cyberattacks involving social engineering | 98% | Sprinto / Purplesec |
| Breaches involving human element | 68% | Verizon DBIR 2025 |
| Vishing attack surge (H1 to H2 2024) | 442% | CrowdStrike 2025 Global Threat Report |
| Cyberattacks originating from email | 68% | KnowBe4 Financial Sector Threats Report 2025 |
| FBI IC3 BEC losses (2024) | $2.77B | FBI Internet Crime Report 2024 |
| Average BEC attack cost | $4.67M | IBM / HoxHunt |
| Social engineering powered by AI | 80%+ | Abnormal Security / Xceedance |
| Baseline phishing click rate (untrained) | 33.1% | KnowBe4 |
| Click rate reduction after training | 86% | KnowBe4 |
| Orgs citing phishing/social eng as top risk | 42% | WEF Global Cybersecurity Outlook 2025 |
| Social eng as primary attack vector | 42% | SentinelOne / Industry Reports |
| Social eng share of all threats (Q1 2024) | 90% | Avast Q1 2024 Threat Report |
| Breaches involving human element | 60% | Verizon DBIR 2025 |
| US social engineering losses (2024) | $16.6B | FBI IC3 2024 |
Record US Social Engineering Losses
US social engineering losses surged from $12.5B in 2023 to $16.6B in 2024 — a 33% increase year-over-year. BEC alone accounted for $2.77B of that total. The FBI has recorded $55.5B in cumulative BEC losses over the past decade, making it the most financially devastating social engineering technique on record. (FBI IC3 2023, 2024)
The Human Element Refuses to Shrink
Despite billions spent on security technology, humans remain the primary breach vector. 60% of breaches involve the human element (Verizon 2025), 98% of cyberattacks involve social engineering (Sprinto), and the median time to click a phishing link is just 21 seconds — faster than any automated defence can intervene. 76% of organizations still lack phishing-resistant MFA (Arctic Wolf 2025). Technology alone cannot solve a human problem. (Verizon DBIR 2025, Sprinto, Arctic Wolf 2025)
The convergence of multiple social engineering channels creates compound risk. An attacker might research a target on LinkedIn (reconnaissance), send an AI-crafted phishing email (initial access), follow up with a deepfaked voice call from their "CEO" (vishing), and request an urgent wire transfer via BEC. Each layer adds credibility. Each layer is now cheaper and more convincing thanks to AI. The organizations that defend against only one channel remain exposed to the others.
🎭 Social Engineering Attack Types Breakdown
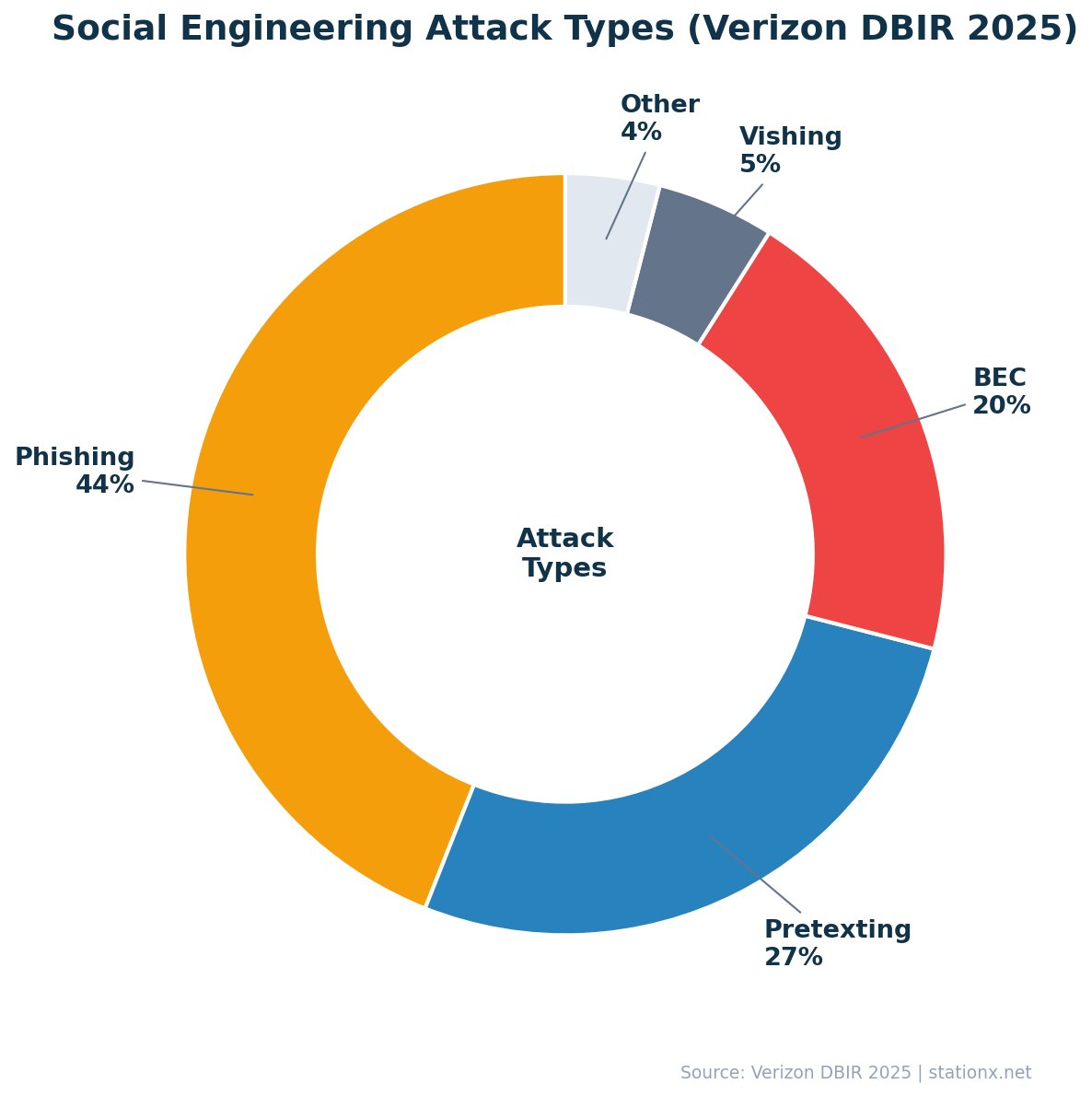
These techniques span multiple channels. Email phishing remains the largest category, but vishing (voice phishing) surged to account for 60%+ of phishing engagements in Q1 2025 (Keepnet). Pretexting now represents 50%+ of all incidents (Verizon DBIR 2025), nearly doubling from prior years. Smishing click rates of 19-36% dwarf email phishing's 2-4% (Eftsure), making SMS the most effective per-message channel.
New attack techniques are emerging rapidly. Fake CAPTCHA campaigns surged 1,450% in Q1 2025 (Secureframe). Fake road toll smishing scams spiked 2,900% from 2023 to 2024 (APWG). AI-generated BEC emails now account for 40% of all BEC messages (VIPRE 2024). The attack surface is expanding faster than defences can adapt.
Social Engineering Attack Type Explorer
Select an attack type to see key statistics for each social engineering technique.
Phishing (Email)
| Daily phishing emails | 3.4 billion |
| Share of breaches | 16% |
| AI-generated share | 80%+ |
| Median time to click | 21 seconds |
| Click rate (untrained) | 33.1% |
Vishing (Voice)
| Attack surge (2024) | 442% |
| Deepfake vishing surge | 1,633% |
| Orgs targeted | 70% |
| Share of phishing engagements | 60%+ |
| Largest single loss | $25M |
Smishing (SMS)
| Click rate | 19-36% |
| vs email click rate | 9x higher |
| YoY volume surge | 40% |
| Toll scam surge | 2,900% |
| Share of mobile attacks | Growing |
Pretexting
| Share of SE incidents | 50%+ |
| Share of SE breaches | 27% |
| Trend | Nearly doubled |
| Uses fabricated scenarios | Yes |
| AI-enhanced | Increasingly |
Business Email Compromise
| 2024 FBI losses | $2.77B |
| Cumulative losses (decade) | $55.5B |
| Avg cost per breach | $4.89M |
| Share of incidents | 27% |
| AI-generated share | 40% |
| Finding | Value | Source |
|---|---|---|
| Phishing in data breaches | 36% | Verizon DBIR 2025 |
| Pretexting share of social eng attacks | 50%+ | Verizon DBIR 2025 |
| Social eng incidents involving pretexting | 50%+ | Verizon DBIR 2025 |
| Vishing attack surge (2025) | 442% | CrowdStrike 2025 Global Threat Report |
| Vishing share of phishing engagements Q1 2025 | 60%+ | Keepnet Labs |
| Smishing YoY surge | 40% | APWG / Keepnet |
| Smishing share of mobile attacks | 35% | SentinelOne / Industry Reports |
| SMS phishing click-through rate | 19-36% | Sprinto / Eftsure |
| Smishing/vishing breaches | 19% | Verizon DBIR 2025 |
| Identity-based phishing incidents | 60% | Cisco Cybersecurity Readiness Index 2025 |
| BEC emails that were AI-generated | 40% | VIPRE Security Group Q2 2024 |
| Fake CAPTCHA campaign surge Q1 2025 | 1,450% | Secureframe / Industry Reports |
| Fake road toll smishing surge | 2,900% | APWG / Eftsure |
Pretexting Now Dominates Social Engineering
Pretexting — creating a fabricated scenario to extract information — now accounts for 50%+ of all social engineering incidents and 27% of social engineering breaches (Verizon DBIR 2025). This represents a near-doubling from prior years. Attackers have shifted from mass-blast phishing to targeted, story-driven attacks that exploit specific organizational contexts. Combined with AI-generated content, pretexting attacks are increasingly difficult to distinguish from legitimate communication. (Verizon DBIR 2025)
SMS Phishing Is 9x More Effective Than Email
Smishing click-through rates range from 19-36%, compared to just 2-4% for email phishing (Eftsure). That makes SMS phishing up to 9x more effective per message. Combined with a 40% YoY surge in smishing volume (APWG/Keepnet) and a 2,900% spike in fake toll scams (APWG), mobile-first social engineering is the fastest-growing attack channel. (Eftsure, APWG, Keepnet 2025)
Emerging Social Engineering Techniques
Beyond the established categories, several newer techniques are gaining traction. Fake CAPTCHA campaigns surged 1,450% in Q1 2025 — attackers present a fake "verify you're human" page that actually executes malicious code. QR code phishing (quishing) uses QR codes in emails or physical locations to bypass email URL scanning. Callback phishing combines email with phone follow-up: the email creates the context, the phone call extracts the credentials.
Multi-channel attacks are particularly effective. An attacker might send a LinkedIn connection request (reconnaissance), follow with a phishing email referencing a shared connection (credibility), then make a vishing call impersonating the shared connection (trust exploitation). Each channel reinforces the others. Defending against these layered approaches requires training that covers all vectors, not just email.
Supply chain social engineering targets the trust relationships between organizations. Attackers compromise a vendor's email account and use it to send invoices or requests to the vendor's clients. Because the email comes from a legitimate, trusted address, it bypasses both technical filters and human suspicion. IBM reports that third-party breaches doubled year-over-year to 30% of all incidents in 2025 — many originating from social engineering of supply chain partners.
📈 How Common Is Social Engineering?
It is the single most prevalent attack vector in cybersecurity. 98% of cyberattacks involve some form of social engineering (Sprinto), and it accounted for 90% of all threats in Q1 2024 (Avast). 3.4 billion phishing emails are sent daily. The FBI IC3 received 193,407 phishing complaints in 2024 alone. 70% of organizations were targeted by vishing attacks (Keepnet 2025), and even small organizations face a 70% weekly probability of receiving a BEC email (Abnormal Security).
The frequency continues to accelerate. 91% of security professionals reported encountering AI-enabled email attacks in the past 6 months (Secureframe). Scam phone calls reached 2.56 billion in 2025 (Truecaller). Microsoft processes 600 million+ password attacks per day, many originating from social engineering-harvested credentials. These are not occasional events — they are a continuous, industrialized assault on human trust.
| Finding | Value | Source |
|---|---|---|
| Cyberattacks involving social engineering | 98% | Sprinto / Purplesec |
| Social eng share of all threats (Q1 2024) | 90% | Avast Q1 2024 Threat Report |
| Social eng as primary attack vector | 42% | SentinelOne / Industry Reports |
| Phishing emails sent daily | 3.4 billion | AAG IT / industry data |
| Phishing attacks reported annually | 3.8 million | APWG Phishing Activity Trends |
| Phishing attacks Q2 2025 | 1,130,393 | APWG Phishing Activity Trends Q2 2025 |
| Scam phone calls reported (2025) | 2.56 billion | Truecaller / Programs.com |
| Organizations targeted by vishing | 70% | Keepnet Labs |
| Weekly BEC probability (small orgs) | 70% | Abnormal Security / Hoxhunt |
| Microsoft: password attacks per day | 600 million+ | Microsoft Digital Defense Report 2024 |
| Security pros reporting AI email attacks | 91% | Abnormal Security / Secureframe |
Social Engineering Is Industrial-Scale Crime
3.4 billion phishing emails daily. 2.56 billion scam calls yearly. 600 million+ password attacks per day on Microsoft alone. Social engineering is not a niche threat — it is the dominant criminal enterprise of the digital age. The sheer volume means that even a low success rate translates to millions of successful compromises annually. At a 2.7% email phishing click rate and 3.4 billion daily emails, that is approximately 92 million successful clicks per day — each one a potential breach entry point. (Verizon DBIR 2025, Truecaller 2025, Microsoft 2024)
The frequency data reveals a critical insight: social engineering is not a targeted, sophisticated attack — it is a numbers game. Attackers send billions of messages knowing that even a small percentage will succeed. This is why awareness training (reducing the click rate) has such outsized impact. Reducing the baseline click rate from 33.1% to 4.1% does not just reduce risk by 86% — it fundamentally changes the economics of social engineering for attackers, making your organization an unprofitable target.
📧 Business Email Compromise (BEC) Statistics
BEC is the most financially devastating form of social engineering. FBI IC3 reported $2.77 billion in BEC losses in 2024, and cumulative losses over the past decade have reached $55.5 billion (FBI IC3). The average cost per BEC breach is $4.89 million (IBM 2025), making it the second most expensive breach type after ransomware.
BEC attacks are increasing in both volume and sophistication. SpiderLabs documented a 15% increase in BEC emails in 2025 (LevelBlue). 63% of organizations experienced BEC in the past year (AFP 2025). BEC volume surged 54% in H1 2025 compared to 2023 (Abnormal Security). 40% of BEC emails are now AI-generated (VIPRE 2024), making them harder to detect by both humans and traditional email filters. Even organizations with fewer than 1,000 employees face a 70% weekly probability of a BEC attack.
| Finding | Value | Source |
|---|---|---|
| FBI IC3 BEC losses (2024) | $2.77B | FBI Internet Crime Report 2024 |
| FBI IC3 BEC losses (2023) | $2.9B | FBI Internet Crime Report 2023 |
| FBI cumulative BEC losses (decade) | $55.5B | FBI IC3 |
| Average BEC attack cost (IBM) | $4.67M | IBM / HoxHunt |
| Average cost per BEC breach | $4.89M | IBM Cost of a Data Breach Report 2025 |
| BEC share of all incidents | 27% | Arctic Wolf Threat Report 2025 |
| Average BEC loss per incident | $160,000+ | Arctic Wolf Threat Report 2025 |
| BEC share of financially motivated breaches | 58% | Verizon DBIR 2025 |
| BEC volume surge (H1 2025) | 54% | Abnormal Security |
| BEC attack increase in 2025 | 15% | SpiderLabs / LevelBlue |
| BEC emails AI-generated | 40% | VIPRE Security Group Q2 2024 |
| Organizations experiencing BEC (2025) | 63% | AFP Fraud Survey 2025 |
| Weekly BEC probability (<1,000 employees) | 70% | Abnormal Security / Hoxhunt |
BEC: Low-Tech, High-Return Crime
BEC requires no malware, no exploits, and no technical sophistication — yet it costs organizations millions per incident (IBM 2025) and has accumulated tens of billions in FBI-reported losses over a decade. 63% of organizations experienced BEC in the past year (AFP 2025), and even small organizations (<1,000 employees) face a 70% weekly probability of receiving a BEC email. BEC is the most cost-effective attack for criminals. (IBM 2025, FBI IC3, AFP 2025, Abnormal Security)
BEC Attack Characteristics
- No malware or exploits needed
- Exploits trust and authority
- 40% now AI-generated
- Targets finance departments
BEC Defence Measures
- Dual-approval for wire transfers
- Out-of-band verification (phone callback)
- AI-powered email analysis
- Regular BEC simulation exercises
BEC attack sophistication is accelerating. Traditional BEC relied on simple email spoofing — impersonating an executive to request a wire transfer. Modern BEC campaigns use AI to craft contextually perfect emails, compromise legitimate accounts to send from trusted addresses, and combine email with vishing follow-up calls to add urgency. The shift from volume-based to precision-based BEC means that individual attacks are more likely to succeed and harder to detect.
The FBI's cumulative decade-long BEC loss figure likely underrepresents the true cost. Many organizations do not report BEC losses to law enforcement. Many more absorb smaller losses without formal incident reporting. The actual global cost of BEC is almost certainly higher than FBI figures suggest.
BEC Attack Patterns
BEC attacks follow recognizable patterns that organizations can defend against. The most common BEC scenario is CEO fraud — an attacker impersonates the CEO or CFO and requests an urgent wire transfer. Invoice fraud is the second most common: attackers compromise a vendor's email account and send modified invoices with updated bank details. Payroll diversion targets HR departments: an employee's direct deposit information is changed to the attacker's account.
Each pattern has specific defensive measures. CEO fraud is defeated by dual-approval requirements and out-of-band verification (calling the CEO on a known number to confirm). Invoice fraud is defeated by verifying payment detail changes through a separate communication channel and maintaining a vendor contact database independent of email. Payroll diversion is defeated by requiring in-person or video verification for banking detail changes.
The rise of AI-generated BEC makes these procedural controls more important than ever. 40% of BEC emails are now AI-generated (VIPRE 2024), meaning they lack the linguistic tells that previously helped recipients identify fraudulent requests. The only reliable defence is process-based: verification steps that are independent of the communication channel being compromised.
BEC Recovery & Law Enforcement
Speed is critical in BEC recovery. When organizations detect a fraudulent transfer within 24 hours and contact both their bank and the FBI IC3's Recovery Asset Team (RAT), recovery rates are significantly higher. The FBI's RAT has successfully frozen and recovered hundreds of millions of dollars in fraudulent BEC transfers. However, most organizations detect BEC fraud too slowly — the median time between transfer and detection is often days or weeks, by which point the funds have been moved through multiple accounts and are unrecoverable.
Organizations should pre-establish relationships with their bank's fraud team and have FBI IC3 reporting procedures ready before an incident occurs. Every hour of delay reduces recovery probability significantly. Cyber insurance policies increasingly cover BEC losses, but typically require proof that reasonable security controls were in place at the time of the incident — including awareness training and dual-approval procedures.
📞 Vishing Statistics & Voice-Based Attacks
Voice phishing has transformed from a minor annoyance into a primary attack vector. Vishing attacks surged 442% from H1 to H2 2024 (CrowdStrike). Deepfake-enabled vishing spiked 1,633% in Q1 2025 compared to Q4 2024 (Keepnet). It now accounts for over 60% of all phishing-related engagements, overtaking email as the dominant phishing channel in Q1 2025.
AI voice cloning is the catalyst. McAfee found that AI can clone a person's voice from just 3 seconds of audio (McAfee 2024). 25% of users are fooled by deepfake voices (Keepnet). The largest single deepfake vishing loss was $25 million, where a finance executive was tricked via a video call with a deepfaked CFO (CrowdStrike). Scam phone calls reached 2.56 billion in 2025 (Truecaller). Deloitte projects deepfake fraud costs will reach $40 billion by 2027.
| Finding | Value | Source |
|---|---|---|
| Vishing attack surge (H1 to H2 2024) | 442% | CrowdStrike 2025 Global Threat Report |
| Voice phishing increase YoY | 442% | CrowdStrike 2025 Global Threat Report |
| Deepfake vishing surge Q1 2025 | 1,633% | CrowdStrike / Keepnet |
| Organizations targeted by vishing | 70% | Keepnet Labs |
| Vishing share of phishing engagements | 60%+ | Keepnet Labs |
| Users fooled by deepfake voices | 25% | Keepnet Labs |
| Median loss per vishing victim | $1,400 | FTC / Keepnet |
| Scam phone calls (2025) | 2.56 billion | Truecaller / Programs.com |
| People targeted by AI voice scams | 25% | McAfee |
| Audio needed to clone a voice | 3 seconds | McAfee |
| Largest deepfake CFO scam | $25.6M | CrowdStrike 2025 Global Threat Report |
| Projected deepfake fraud costs (2027) | $40B | Deloitte |
| Smishing/vishing breaches | 19% | Verizon DBIR 2025 |
The economics of vishing have shifted dramatically. Traditional phone scams required human operators, limiting scale. AI-generated voice calls can now be produced at negligible cost with text-to-speech systems that are indistinguishable from real humans. Combined with AI voice cloning (3 seconds of audio is sufficient per McAfee), attackers can impersonate specific individuals — a CEO calling from an "unknown number" asking the CFO to authorize an emergency transfer. The $25 million deepfake CFO scam documented by CrowdStrike in 2024 demonstrates the upper bound of what is possible.
Defending against vishing requires procedural controls that many organizations lack. Callback verification on a known number (not the number provided by the caller) is the most effective defence. Organizations should establish code words for high-value authorizations, require dual approval for financial transfers, and train employees to recognize the urgency tactics that vishing attackers use. Technical solutions such as AI-powered call analysis and caller authentication (STIR/SHAKEN) provide additional layers but cannot replace human vigilance.
Vishing: From Nuisance to Primary Threat
Voice phishing surged 442% from H1 to H2 2024 (CrowdStrike), deepfake-enabled vishing spiked 1,633% in Q1 2025 (Keepnet), and vishing now accounts for 60%+ of all phishing-related engagements. Cross-referencing with McAfee's data showing AI can clone a voice from just 3 seconds of audio, the economics are clear: vishing is now cheaper, faster, and more convincing than email phishing. (CrowdStrike 2025, Keepnet 2025, McAfee 2024)
Vishing Risk Factors
- AI can clone voice from 3 seconds of audio
- 25% of users fooled by deepfake voices
- 70% of organizations targeted
- 60%+ of phishing engagements are voice-based
Vishing Defences
- Voice verification protocols for transfers
- Callback verification on separate channel
- Employee training on vishing tactics
- AI-powered call analysis tools
🖱️ Social Engineering Success Rates & Click Rates
Social engineering success rates vary dramatically by channel and target. Untrained employees have a baseline phishing click rate of 33.1% (KnowBe4 2025). SMS phishing achieves click rates of 19-36%, compared to just 2-4% for email phishing (Eftsure) — making smishing up to 9x more effective per message. The median time from email delivery to click is just 21 seconds (Verizon DBIR 2025), far too fast for any human review process.
AI-generated phishing achieves click rates comparable to human-crafted campaigns but at 95% lower cost (HBR 2024). Healthcare employees are the most vulnerable industry group at 41.9% baseline click rate (KnowBe4 2025). After 12 months of continuous security awareness training, click rates drop to 4.1% — an 86% reduction that demonstrates the gap is addressable. The challenge is not technology but implementation.
| Finding | Value | Source |
|---|---|---|
| Users who click phishing links | 2.7% | Verizon DBIR 2025 |
| Median time to click phishing link | 21 seconds | Verizon DBIR 2025 |
| Median time to report phishing | 28 minutes | Verizon DBIR 2025 |
| AI phishing click-through rate | 54% | Harvard Business Review / Heiding, Schneier et al. |
| Baseline click rate (untrained employees) | 33.1% | KnowBe4 |
| Click rate after 12 months of training | 4.1% | KnowBe4 |
| SMS phishing click rate (vs 2-4% email) | 19-36% | Sprinto / Eftsure |
| Healthcare baseline click rate (highest) | 41.9% | KnowBe4 |
The click rate data reveals a critical asymmetry. Attackers need only one click to succeed. Defenders need every employee to resist. In a 1,000-person organization with a 33.1% click rate, 331 employees will click a phishing link. Even at the trained rate of 4.1%, 41 employees remain vulnerable. This is why defence-in-depth — combining training with technical controls like phishing-resistant MFA, email filtering, and endpoint detection — is essential. No single layer is sufficient.
The 21-second median click time (Verizon DBIR 2025) is faster than most people spend considering an email. This suggests that the most effective training focuses not on teaching people to analyze emails in detail, but on building an automatic "pause and verify" reflex — similar to looking both ways before crossing a street. The goal is not analysis but hesitation: just enough friction to break the 21-second impulse.
The Channel Effectiveness Gap
Cross-referencing click rate data across channels reveals a stark effectiveness gradient. Email phishing: 2-4% click rate. AI-enhanced email phishing: comparable to human-crafted at 95% lower cost. SMS phishing (smishing): 19-36% click rate (9x email). Voice phishing (vishing): 60%+ of phishing engagements, with 25% of users fooled by deepfake voices. The clear trend: the more personal the channel, the higher the success rate. Defenders must expand beyond email-only protection. (Eftsure, Verizon DBIR 2025, Keepnet 2025, KnowBe4 2025)
💰 Cost of Social Engineering Attacks
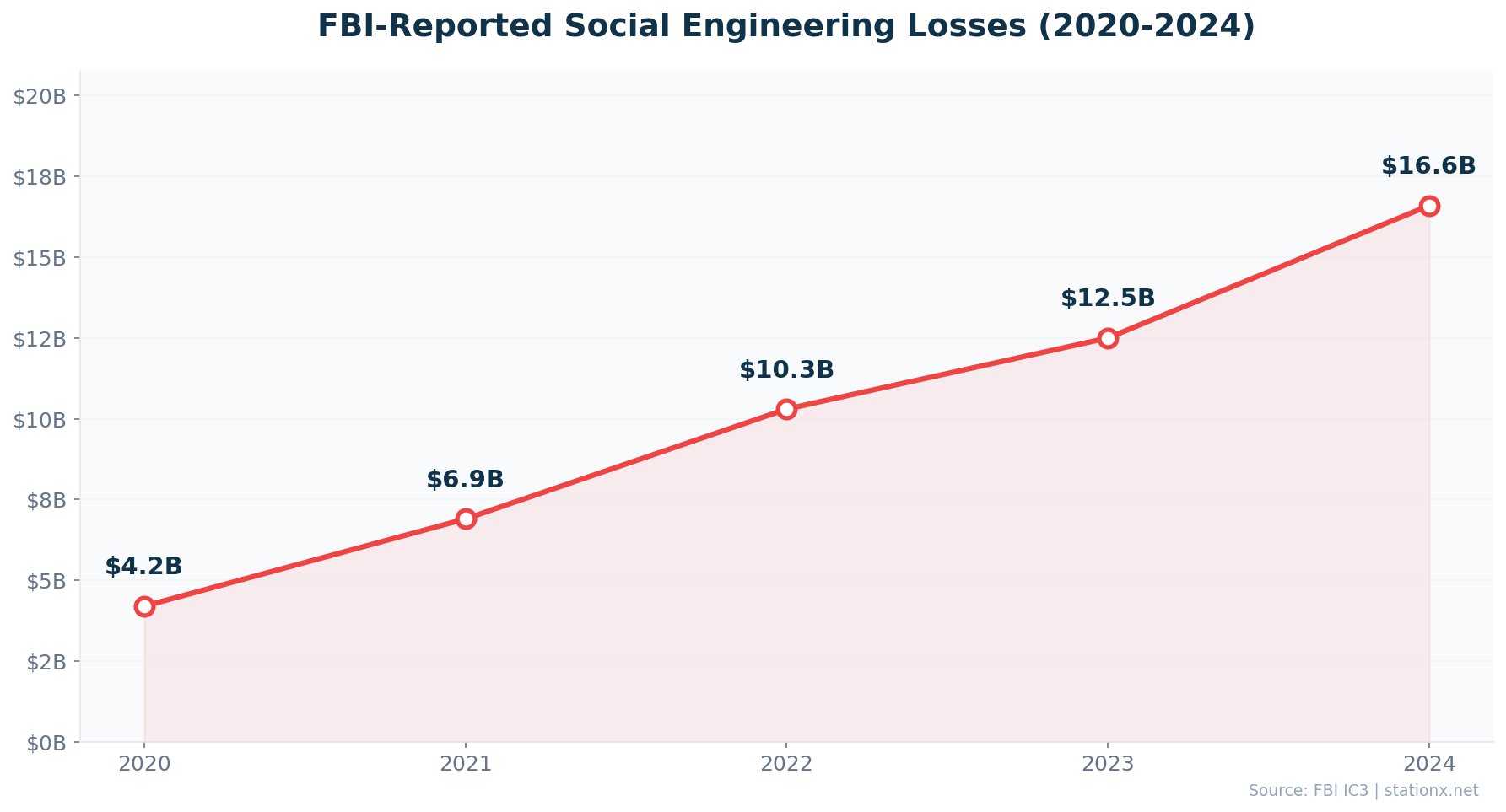
The financial damage is staggering. FBI-reported US losses grew 33% in 2024 to record levels (FBI IC3). BEC alone accounted for $2.77 billion in FBI-reported losses. The average attack costs $130,000 (Eftsure), while individual BEC breaches routinely run into the millions (IBM 2025).
Cumulative BEC losses over the past decade run into tens of billions (FBI IC3). Stolen credentials — often harvested through social engineering — cost $4.81 million per breach (IBM 2025). The median vishing victim loses $1,400 per incident (FTC/Keepnet). Deloitte projects deepfake fraud costs will reach $40 billion by 2027. The economics overwhelmingly favor attackers: a single BEC email costs nothing to send but can yield millions.
| Finding | Value | Source |
|---|---|---|
| US social engineering losses (2024) | $16.6B | FBI IC3 2024 |
| US social engineering losses (2023) | $12.5B | FBI IC3 2023 |
| FBI IC3 BEC losses (2024) | $2.77B | FBI Internet Crime Report 2024 |
| Average BEC attack cost | $4.67M | IBM / HoxHunt |
| Average cost per BEC breach | $4.89M | IBM Cost of a Data Breach Report 2025 |
| Average cost per social engineering attack | $130,000 | Eftsure / Industry Analysis |
| Average BEC loss per incident | $160,000+ | Arctic Wolf Threat Report 2025 |
| Cumulative BEC losses (decade) | $55.5B | FBI IC3 |
| Projected deepfake fraud costs (2027) | $40B | Deloitte |
| Median loss per vishing victim | $1,400 | FTC / Keepnet |
| Stolen credentials breach cost | $4.81M | IBM Cost of a Data Breach Report 2025 |
Fastest Growing Attacks
- Deepfake vishing — +1,633% in Q1 2025
- Fake CAPTCHA — +1,450% in Q1 2025
- Vishing — +442% H1 to H2 2024
- Fake toll smishing — +2,900% in 2024
Most Costly Attacks
- BEC — $4.89M avg per breach
- Stolen credentials — $4.81M avg
- Avg social eng attack — $130K
- Cumulative BEC — $55.5B (decade)
The Return-on-Investment for Social Engineering Criminals
A single BEC email costs nothing to send. A single AI-crafted phishing campaign costs 95% less than its manual equivalent. Yet the average social engineering attack yields six figures, and BEC breaches run into the millions. Cross-referencing attack costs with payouts, social engineering delivers the highest criminal ROI of any cyberattack category. This is why volume continues to increase: the economics overwhelmingly reward attackers. (IBM 2025, HBR 2024, Eftsure, FBI IC3)
The cost structure of social engineering explains its dominance. Unlike ransomware (which requires malware development, infrastructure, and negotiation), or exploit-based attacks (which require zero-day research), social engineering requires only a message and a target. AI has reduced even the message-crafting cost to near zero. The only effective counterweight is making targets harder to deceive — which is exactly what awareness training achieves.
Cost Breakdown by Attack Type
The financial impact varies dramatically by social engineering technique. BEC leads as the costliest breach type (IBM 2025), followed closely by stolen credentials at $4.81 million per breach. These vector-specific costs reflect the depth of compromise: BEC often results in direct financial transfers that are difficult to recover, while credential theft enables persistent access that can escalate to full data exfiltration.
At the individual level, vishing victims lose a median of $1,400 per incident (FTC/Keepnet), but high-value targets can lose millions. The $25 million deepfake CFO scam (CrowdStrike 2024) and the staggering decade of cumulative FBI-reported BEC losses demonstrate the extreme variance in social engineering outcomes. The average attack costs six figures (Eftsure) — but this average masks a distribution where most attacks cost relatively little while a small number of BEC and deepfake attacks cost millions.
Projected costs continue to escalate. Deloitte projects deepfake fraud costs will reach $40 billion by 2027. FBI IC3 losses grew 33% year-over-year in 2024. AI is reducing attack costs while increasing effectiveness. Without intervention, these trends will continue compounding.
🏢 Social Engineering by Industry
Every industry is a target, but some are more vulnerable than others. Healthcare has the highest baseline phishing click rate at 41.9% (KnowBe4 2025), driven by high-pressure clinical environments where staff prioritize patient care over email scrutiny. Financial services face 300x more attacks than other industries (KnowBe4 2025), and BEC accounts for 27% of all investigated incidents (Arctic Wolf 2025).
Small businesses are disproportionately targeted: employees at small firms receive 350% more attacks than large enterprise employees (StrongDM/Verizon DBIR). SMBs also have higher malicious email rates and fewer resources for awareness training. Phishing and social engineering are cited as the top cyber risk by organizations worldwide (WEF 2025).
| Finding | Value | Source |
|---|---|---|
| Orgs citing phishing/social eng as top risk | 42% | WEF Global Cybersecurity Outlook 2025 |
| Financial sector attack frequency | 300x | KnowBe4 Financial Sector Threats Report 2025 |
| Healthcare baseline click rate (highest) | 41.9% | KnowBe4 |
| Financial sector phish-prone rate | 44.7% | KnowBe4 Financial Sector Threats Report 2025 |
| SMB vs enterprise social eng rate | 350% | Verizon DBIR / StrongDM |
| SMB malicious email rate | 1 in 323 | Verizon DBIR / StrongDM |
| BEC share of all incidents | 27% | Arctic Wolf Threat Report 2025 |
Most Targeted Industries
- Healthcare — 41.9% baseline click rate
- Financial Services — 300x attack rate
- Small Business — 350% more SE attacks
Key Defence Gaps
- 76% lack phishing-resistant MFA
- 27% of incidents are BEC
- 33.1% baseline click rate (untrained)
Healthcare
Healthcare employees have the highest baseline phishing vulnerability at 41.9% (KnowBe4 2025). This is not because healthcare workers are less intelligent — it is because clinical environments create perfect conditions for social engineering: high urgency, frequent interruptions, multiple unfamiliar system logins, and a culture that prioritizes patient care over cybersecurity protocols. Social engineering attacks targeting healthcare often impersonate medical supply vendors, insurance companies, or internal IT support.
Financial Services
Financial services face 300x more attacks than other industries (KnowBe4 2025), driven by the direct financial payoff of successful BEC and wire transfer fraud. Banks and financial institutions are the primary targets for sophisticated pretexting, where attackers build detailed scenarios to manipulate employees into authorizing transactions. BEC targeting finance departments accounts for the majority of cumulative FBI-reported losses.
Small & Medium Businesses
Small business employees receive 350% more attacks than large enterprise employees (StrongDM/Verizon DBIR). This concentration reflects attackers' awareness that SMBs typically have fewer security controls, less frequent training, and smaller IT teams. SMBs also have higher malicious email rates and are less likely to have BEC-specific detection in place. The 70% weekly BEC probability for organizations with fewer than 1,000 employees (Abnormal Security) means that for most small businesses, it is not a question of "if" but "when."
Education & Government
Education institutions face elevated social engineering risk due to open communication cultures, high staff turnover, and large student populations who may lack security awareness. Insurance has the second-highest baseline phishing click rate at 39.2% (KnowBe4 2025), followed by Retail/Wholesale at 36.5%. Government agencies are frequently targeted by both criminal and nation-state social engineering campaigns, with BEC targeting government procurement and finance departments.
The industry-specific data underscores that social engineering risk is universal but varies in intensity and attack pattern. Organizations in every sector need awareness training, but the specific content should reflect industry-specific threats: healthcare staff need training on medical supply vendor impersonation, financial services need training on regulatory-themed pretexting, SMBs need training on CEO fraud and invoice fraud, and government employees need training on nation-state social engineering techniques.
Industry Baseline Vulnerability Rankings
Cross-referencing KnowBe4's phish-prone percentage data across industries reveals a clear vulnerability hierarchy. Healthcare leads at 41.9%, followed by Insurance (39.2%), Retail/Wholesale (36.5%), and the global average (33.1%). Financial services, despite facing 300x more attacks, have a lower baseline PPP — likely reflecting higher existing investment in security awareness. The most vulnerable industries are not those facing the most attacks, but those with the least training investment. (KnowBe4 2025, Arctic Wolf 2025, Verizon DBIR 2025)
🧠 Social Engineering and the Human Factor
People remain the weakest link. 60% of breaches involve the human element — social engineering, errors, and misuse (Verizon DBIR 2025). 88% of breaches are caused by human error (Stanford). 68% of cyberattacks originate from email (KnowBe4). The median time to click a phishing link is 21 seconds, while the median time to report it is 20 hours (Verizon DBIR 2025) — attackers have a massive head start.
76% of organizations still lack phishing-resistant MFA such as FIDO2 or passkeys (Arctic Wolf 2025). Pretexting — using fabricated scenarios to manipulate targets — now accounts for 50%+ of social engineering incidents (Verizon DBIR 2025). Identity-based phishing incidents continue to rise (Cisco 2025). The data is clear: investing in training, MFA, and verification procedures delivers measurable returns, yet most organizations remain under-invested.
| Finding | Value | Source |
|---|---|---|
| Breaches involving human element | 68% | Verizon DBIR 2025 |
| Human element in breaches | 60% | Verizon DBIR 2025 |
| Breaches caused by human error | 88% | Stanford University |
| Users who click phishing links | 2.7% | Verizon DBIR 2025 |
| Median time to click phishing link | 21 seconds | Verizon DBIR 2025 |
| Identity-based phishing incidents | 60% | Cisco Cybersecurity Readiness Index 2025 |
| Orgs without phishing-resistant MFA | 76% | Arctic Wolf Threat Report 2025 |
| Attacks originating from email | 68% | KnowBe4 Financial Sector Threats Report 2025 |
| Incidents involving pretexting | 50%+ | Verizon DBIR 2025 |
21 Seconds: The Window That Decides Everything
The median time to click a phishing link is 21 seconds (Verizon DBIR 2025). The median time to report it is 20 hours. That gap — 21 seconds to compromise versus 20 hours to detect — is the fundamental human factor cybersecurity challenge. No email gateway, no AI filter, no security policy can operate within that 21-second window. Only trained human judgment can. This is why the 86% reduction from awareness training matters: it shrinks the population of people who click in those first 21 seconds. (Verizon DBIR 2025, KnowBe4 2025)
The human factor in cybersecurity is not a failing to be eliminated — it is a reality to be managed. Every employee is both a potential target and a potential sensor. Organizations that frame security awareness as a "compliance checkbox" see minimal improvement. Organizations that treat every employee as a human firewall — providing continuous training, easy reporting tools, and positive reinforcement for catching threats — see dramatic reductions in social engineering success rates.
The 76% of organizations without phishing-resistant MFA (Arctic Wolf 2025) represents the single largest addressable gap. FIDO2 and passkey deployments eliminate credential phishing entirely — no matter how convincing the social engineering, there is no credential to steal. Combined with awareness training, phishing-resistant MFA creates a layered defence that addresses both the human and technical dimensions of social engineering.
The Psychology Behind Social Engineering Success
Social engineering exploits six fundamental psychological principles: authority (impersonating executives or IT support), urgency (creating time pressure to prevent careful analysis), scarcity (limited-time offers or threats of account closure), social proof (referencing colleagues or shared connections), reciprocity (offering something of value before making a request), and commitment (getting small agreements before escalating to larger requests). AI has not changed these principles — it has simply made their application faster, cheaper, and more personalized.
Understanding these principles is the foundation of effective awareness training. When employees recognize the psychological levers being pulled — "why is this email creating urgency?", "why is this person invoking authority?", "why am I being asked to bypass normal procedures?" — they develop the critical thinking reflexes that reduce click rates by 86%. The most effective training programs explicitly teach these principles and provide examples of how each is used in real social engineering attacks.
The Reporting Gap
The gap between clicking and reporting is a critical human factor challenge. The median time to click a phishing link is 21 seconds (Verizon DBIR 2025). The median time to report a suspected phishing email is 20 hours. This 3,400x differential means that by the time a social engineering attempt is reported, the attacker has had nearly a full business day to exploit the compromised credentials, initiate fraudulent transfers, or move laterally within the network.
Closing this reporting gap requires making reporting frictionless (one-click phishing report buttons), removing fear of punishment for employees who clicked and then reported, and creating a culture where reporting is celebrated rather than stigmatized. Organizations that actively reward phishing reports — even when the employee initially clicked — see dramatically faster reporting times and higher report volumes.
The Reporting Paradox: Punishment Reduces Security
Organizations that punish employees for clicking phishing links in simulations see lower reporting rates — employees hide incidents rather than report them. This creates a worse security posture than having no simulation programme at all. Cross-referencing KnowBe4's training data with Arctic Wolf's incident response data, the most secure organizations combine positive reinforcement for reporting with immediate remedial training for clicking. Zero employees should ever be fired for clicking a phishing link in a simulation. The goal is behaviour change, not punishment. (KnowBe4 2025, Arctic Wolf 2025)
🎓 Security Awareness Training Effectiveness
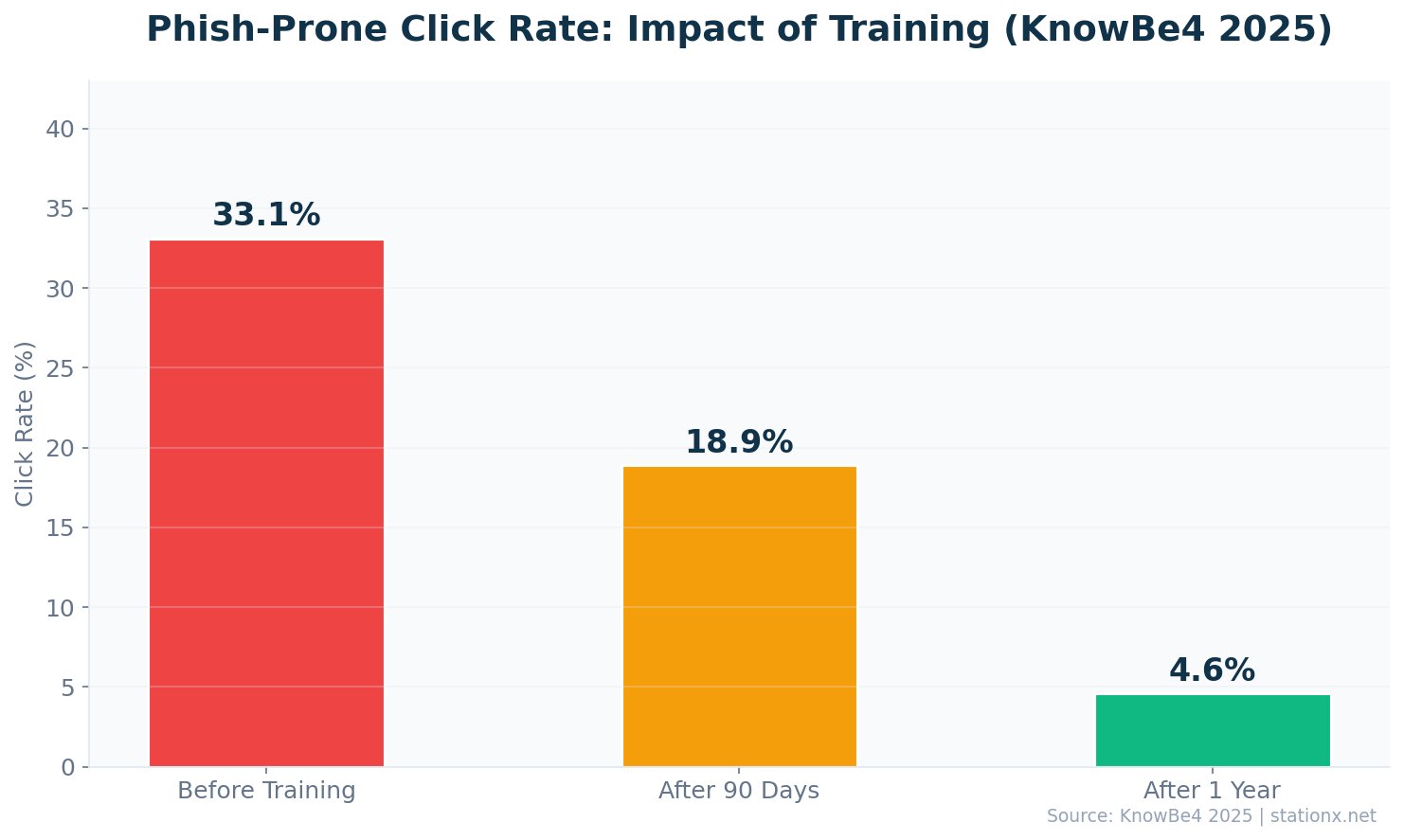
Security awareness training is the most effective countermeasure against social engineering. KnowBe4's 2025 study of 14.5 million users across 62,400 organizations found that untrained employees have a 33.1% baseline phishing click rate. After just 3 months of training, click rates drop by 40%. After 12 months of continuous training, they drop by 86% to just 4.1%.
Healthcare and Pharmaceuticals have the highest baseline vulnerability at 41.9% (KnowBe4 2025), followed by Insurance at 39.2% and Retail/Wholesale at 36.5%. The global baseline has improved 3.5% year-over-year, indicating a positive shift in overall security awareness. Training works — the data is unambiguous.
| Finding | Value | Source |
|---|---|---|
| Baseline PPP before training | 33.1% | KnowBe4 |
| PPP after 12 months of training | 4.1% | KnowBe4 |
| Click rate reduction after training | 86% | KnowBe4 |
| Click rate reduction after 3 months | 40% | KnowBe4 |
| Training reduces phishing susceptibility | <5% | KnowBe4 Financial Sector Threats Report 2025 |
| Users analyzed in benchmark study | 14.5 million | KnowBe4 |
| Healthcare baseline PPP (most vulnerable) | 41.9% | KnowBe4 |
The 86% Training Dividend
KnowBe4's study of 14.5 million users found that untrained employees have a 33.1% phishing click rate. After 12 months of continuous training, that drops to just 4.1% — an 86% reduction. In a 1,000-person organization, that means going from ~331 vulnerable employees to ~41. At an average social engineering attack cost of $130,000, even preventing one successful attack pays for multiple years of training. (KnowBe4 2025)
The data from KnowBe4's benchmark study of 14.5 million users across 62,400 organizations is unambiguous. Training works. The trajectory from 33.1% to 19.9% (after 3 months) to 4.1% (after 12 months) shows that sustained, continuous training delivers compounding returns. Organizations that run quarterly phishing simulations combined with immediate remedial training for those who click achieve the fastest improvement.
Industry-specific baselines vary significantly. Healthcare employees start at 41.9% vulnerability (KnowBe4 2025), followed by Insurance at 39.2% and Retail/Wholesale at 36.5%. These industries require more intensive initial training. The global baseline has improved 3.5% year-over-year, indicating that organizations worldwide are investing in awareness programs — but at 33.1% overall, the majority of the world's employees remain vulnerable to social engineering.
The ROI calculation is straightforward. A 500-person organization with a 33.1% click rate has approximately 166 employees who would click a phishing link. At the average six-figure cost per social engineering incident (Eftsure), even one successful attack costs more than years of awareness training. After training reduces click rates to 4.1%, only 21 employees remain vulnerable — an 87% reduction in attack surface for a fraction of the cost of a single breach.
What Makes Training Effective
Not all security awareness training is equal. KnowBe4's data shows that the 86% reduction requires continuous, multi-format training — not a one-time annual presentation. The most effective programmes combine: monthly phishing simulations (email, SMS, and voice), immediate remedial training for employees who click, quarterly classroom or video training on emerging threats, real-world examples from recent incidents, and positive reinforcement for reporting suspicious messages.
The 3-month checkpoint is critical. KnowBe4 found that click rates drop 40% in just 3 months — meaning organizations see rapid improvement from the initial training investment. However, stopping at 3 months leaves click rates at approximately 20%, still dangerously high. The full 86% reduction requires 12 months of continuous reinforcement. Training is not a project — it is an ongoing programme.
Training content must evolve with threats. Programmes designed around 2020-era email phishing are inadequate for the current threat landscape. Modern training must include AI-generated phishing recognition, vishing scenario exercises, smishing awareness, pretexting identification, BEC response procedures, and deepfake detection. The threat has evolved — training must evolve with it.
Measuring Training Effectiveness
The primary metric for training effectiveness is the Phish-Prone Percentage (PPP) — the percentage of employees who click simulated phishing links. Organizations should track this monthly and benchmark against industry baselines: 33.1% global average, 41.9% healthcare, 39.2% insurance, 36.5% retail (KnowBe4 2025). A well-run programme should achieve sub-10% PPP within 6 months and sub-5% within 12 months.
Secondary metrics include: report rate (percentage of employees who report simulated phishing), time-to-report (how quickly employees flag suspicious messages), and repeat clicker rate (percentage of employees who click multiple simulations). Organizations with high report rates and low repeat clicker rates have the strongest human firewall. Target: >70% report rate, <5% repeat clicker rate, <1 hour median time-to-report.
Use the calculator below to estimate the impact of training on your organization's social engineering risk and the potential cost savings from reducing employee vulnerability.
Security Awareness Training ROI Calculator
Estimate how much your organization could save by reducing phishing susceptibility through awareness training.
🌍 Social Engineering Statistics by Country
🇺🇸 United States
The United States is the largest financial victim worldwide. FBI IC3 reported record social engineering losses in 2024, up 33% year-over-year from $12.5 billion in 2023. BEC losses alone reached $2.77 billion. The FBI received 193,407 phishing complaints in 2024. Over the past decade, cumulative BEC losses reported to the FBI have reached tens of billions.
🇬🇧 United Kingdom
UK businesses face significant social engineering threats. Large UK businesses have the highest breach rates, with social engineering a primary vector (Gov.uk 2025). Small businesses are increasingly targeted, reflecting the global pattern of attackers shifting to less-defended organizations. The UK's National Cyber Strategy continues to emphasize human-focused security measures and mandatory employee training for organizations handling sensitive data.
The UK's Action Fraud service and National Cyber Security Centre (NCSC) report rising volumes of social engineering complaints, with phishing and BEC as the dominant vectors. UK regulatory frameworks including GDPR create additional financial exposure when social engineering leads to data breaches — organizations face potential fines of up to 4% of global annual turnover on top of breach remediation costs.
🌐 Global Trends
Social engineering is a global phenomenon, but regional patterns differ. The Asia-Pacific region has overtaken North America as the most-attacked region (Secureframe). Phishing/social engineering is cited as the top cyber risk by organizations worldwide (WEF 2025). Scam phone calls reached 2.56 billion globally in 2025 (Truecaller). The average per-attack cost remains six figures regardless of geography (Eftsure).
Regional differences in social engineering tactics reflect cultural and technological factors. In APAC, smishing is disproportionately effective due to higher mobile-first internet usage. In Europe, GDPR-themed pretexting (fake data subject access requests) has emerged as a region-specific social engineering technique. In North America, BEC remains the dominant financial threat. In Africa and Latin America, mobile money and SIM swap fraud are the fastest-growing social engineering vectors.
Language barriers that once limited social engineering to English-speaking targets have been eliminated by AI translation. Attackers can now craft grammatically perfect, culturally appropriate social engineering messages in any language, opening global attack surfaces that were previously inaccessible. This expansion is reflected in the APAC region's rise as the most-attacked region worldwide.
🇦🇺 Australia & Asia-Pacific
The Asia-Pacific region has overtaken North America as the most-attacked region for social engineering (Secureframe). This shift reflects APAC's rapid digital transformation, high mobile-first internet usage (which increases smishing effectiveness), and growing economic targets. India faces particularly intense social engineering activity, with rapidly increasing ransomware and phishing volumes. Australia's cybersecurity strategy includes mandatory incident reporting that provides better visibility into social engineering losses.
🇪🇺 European Union
EU organizations face social engineering threats compounded by regulatory exposure. A successful social engineering attack that leads to a data breach triggers GDPR notification requirements within 72 hours, with potential fines of up to 4% of global annual turnover. GDPR-themed pretexting — fake data subject access requests designed to exfiltrate personal data — has emerged as an EU-specific social engineering technique. The EU's NIS2 Directive now mandates security awareness training for critical infrastructure organizations.
| Finding | Value | Source |
|---|---|---|
| US social engineering losses (2024) | $16.6B | FBI IC3 2024 |
| US social engineering losses (2023) | $12.5B | FBI IC3 2023 |
| FBI IC3 BEC losses (US, 2024) | $2.77B | FBI Internet Crime Report 2024 |
| FBI phishing complaints (2024) | 193,407 | FBI Internet Crime Report 2024 |
| UK large business breach rate | 74% | UK DCMS Cyber Security Breaches Survey 2025 |
| UK small business breach rate | 42% | UK DCMS Cyber Security Breaches Survey 2025 |
The Geography of Social Engineering Losses
The US accounts for the largest share of reported social engineering losses (FBI IC3 2024), but this reflects both the scale of the US economy and the FBI's reporting infrastructure. Many countries lack equivalent reporting mechanisms, meaning global losses are significantly underreported. Cross-referencing FBI data with Verizon's global breach database and WEF's survey of 92 countries, social engineering is the top cited cyber risk regardless of geography, GDP, or technological maturity. The threat is universal. (FBI IC3 2024, Verizon DBIR 2025, WEF 2025)
📋 Key Takeaways
- 1. Social engineering dominates cybersecurity. 98% of attacks involve social engineering, and 60% of breaches involve the human element. Technical defences alone are insufficient.
- 2. Vishing is the fastest-growing threat. Voice phishing surged 442% in H2 2024, deepfake vishing spiked 1,633% in Q1 2025, and vishing now accounts for 60%+ of phishing engagements.
- 3. AI has industrialized social engineering. 80%+ of social engineering is AI-powered, AI phishing costs 95% less than manual campaigns, and performance improved 55% in two years.
- 4. BEC is the most costly attack type. Tens of billions in cumulative FBI losses, millions per breach on average, and 63% of organizations experienced BEC in the past year.
- 5. Training works — provably. 12 months of awareness training reduces phishing click rates by 86% (from 33.1% to 4.1%). This is the single highest-ROI security investment.
- 6. SMS phishing is 9x more effective than email. Smishing click rates of 19-36% vs 2-4% for email make mobile-first attacks the fastest-growing threat channel.
- 7. MFA adoption remains dangerously low. 76% of organizations lack phishing-resistant MFA. Until this changes, credential harvesting via social engineering will remain the path of least resistance.
- 8. Pretexting has nearly doubled. 50%+ of social engineering incidents now involve pretexting — fabricated scenarios designed to manipulate specific targets. Mass-blast phishing is giving way to targeted, story-driven attacks.
- 9. Multi-channel attacks are the new normal. Modern social engineering chains email, voice, SMS, and social media. Single-channel defences leave organizations exposed. Train across all vectors, not just email.
- 10. The defence ROI is 70-80x. Combined awareness training + phishing-resistant MFA costs ~$60-70K/year for a 500-person org. A single prevented BEC breach saves millions. The economics of defence are overwhelming.
The Multi-Channel Convergence Effect
Cross-referencing attack data across channels reveals that social engineering is no longer single-vector. Email phishing (3.4B daily), vishing (442% surge), smishing (19-36% click rate), pretexting (50%+ of incidents), and BEC ($2.77B FBI losses) now operate as coordinated attack chains. An attacker may research on LinkedIn, phish via email, follow up with a deepfaked voice call, and execute via BEC — each channel reinforcing the others. Single-channel defence is obsolete. (Verizon DBIR 2025, CrowdStrike 2025, Eftsure, FBI IC3)
The Defence Investment Gap
The average social engineering attack costs six figures (Eftsure), and a single BEC breach averages nearly five million dollars (IBM 2025). Security awareness training for a 500-person organization costs approximately $25,000-50,000 per year. Phishing-resistant MFA deployment costs $10-20 per user per year. Combined annual defence cost: ~$60,000-70,000 — a fraction of a single successful BEC incident. The ROI of social engineering defence is 70-80x the investment. Every organization that has not deployed these controls is making an economically irrational decision. (IBM 2025, Eftsure, KnowBe4 2025)
These ten takeaways distill the core message. Social engineering is not a secondary threat — it is the primary attack vector, the most cost-effective criminal enterprise, and the fastest-growing threat category. The good news: training works (86% reduction in click rates), phishing-resistant MFA eliminates credential harvesting, and procedural controls for financial transfers neutralize BEC. The gap between current vulnerability and achievable defence is a resource allocation problem, not a technology problem.
For security leaders building a business case, the numbers are clear: a single prevented BEC incident pays for years of awareness training, phishing-resistant MFA deployment, and procedural controls combined. The cost of inaction — a 33.1% click rate, 442% vishing growth, 80%+ AI-powered attacks — far exceeds the cost of action. Use the interactive risk assessment below to evaluate your organization's current posture.
Social Engineering Risk Assessment
Answer 8 questions about your organization's defences to get a risk score. Maximum score: 13 (well defended).
Does your organization conduct regular phishing simulations?
Do you have phishing-resistant MFA (FIDO2/passkeys) deployed?
Is there a formal security awareness training program?
Can employees report suspected phishing with one click?
Are voice call verification procedures in place for financial transfers?
Does your email gateway detect AI-generated phishing?
Is there a BEC-specific detection and response process?
Are employees trained to recognise pretexting and vishing?
❓ Social Engineering FAQ
What percentage of cyber attacks involve social engineering?
98% of cyberattacks involve some form of social engineering (Sprinto). The human element is involved in 60% of all data breaches (Verizon DBIR 2025). Social engineering techniques include phishing, vishing, smishing, pretexting, business email compromise, and baiting. These attacks exploit human psychology rather than technical vulnerabilities, making them effective against even the most technologically advanced organizations.
How much does social engineering cost businesses?
US social engineering losses reached $16.6 billion in 2024 (FBI IC3), up 33% from $12.5 billion in 2023. The average BEC breach costs $4.89 million (IBM 2025). The average social engineering attack costs $130,000 (Eftsure). Cumulative BEC losses over the past decade total $55.5 billion (FBI IC3). Deepfake fraud costs are projected to reach $40 billion by 2027 (Deloitte).
What is the most common type of social engineering attack?
Phishing (email-based) remains the most common social engineering technique by volume, with 3.4 billion phishing emails sent daily. However, vishing (voice phishing) overtook email as the dominant phishing channel in Q1 2025, accounting for 60%+ of phishing engagements (Keepnet). Pretexting now represents 50%+ of all social engineering incidents (Verizon DBIR 2025), nearly doubling from prior years. BEC accounts for 27% of investigated incidents (Arctic Wolf 2025).
Does security awareness training reduce social engineering attacks?
Yes, provably. KnowBe4's 2025 study of 14.5 million users across 62,400 organizations found that security awareness training reduces phishing click rates by 86% over 12 months — from a 33.1% baseline to just 4.1%. Even 3 months of training produces a 40% reduction. Healthcare starts highest at 41.9% but sees the same proportional improvement. Training is the single highest-ROI defence against social engineering, and its effectiveness is backed by one of the largest studies in cybersecurity.
How is AI changing social engineering attacks?
AI has fundamentally transformed social engineering. Over 80% of social engineering activity is now AI-powered (Abnormal Security 2025). AI-generated phishing costs 95% less than manual campaigns while maintaining comparable click rates (HBR 2024). AI phishing performance improved 55% from 2023 to 2025 (Hoxhunt). AI can clone a voice from 3 seconds of audio (McAfee 2024), and deepfake-enabled vishing surged 1,633% in Q1 2025 (Keepnet). 40% of BEC emails are AI-generated (VIPRE 2024). 91% of security professionals report encountering AI-enabled email attacks in the past 6 months.
What is the success rate of social engineering attacks?
Social engineering success rates vary by channel and target training level. Untrained employees have a 33.1% phishing click rate (KnowBe4 2025). SMS phishing achieves click rates of 19-36%, making it up to 9x more effective than email phishing at 2-4% (Eftsure). The median time to click a phishing link is just 21 seconds (Verizon DBIR 2025). 25% of users are fooled by deepfake voices in vishing attacks (Keepnet). After 12 months of training, click rates drop to 4.1%.
What is business email compromise (BEC)?
Business email compromise (BEC) is a social engineering technique where attackers impersonate executives, vendors, or trusted contacts via email to trick employees into transferring funds or sharing sensitive information. BEC requires no malware or technical exploitation. FBI IC3 reported $2.77 billion in BEC losses in 2024, with cumulative losses over the past decade reaching tens of billions. 63% of organizations experienced BEC in the past year (AFP 2025). BEC ranks among the costliest breach types (IBM 2025).
What is vishing and why is it growing so fast?
Vishing (voice phishing) uses phone calls to deceive targets into revealing sensitive information or authorizing fraudulent transactions. It surged 442% from H1 to H2 2024 (CrowdStrike) due to AI voice cloning technology that can replicate a person's voice from just 3 seconds of audio (McAfee). Deepfake-enabled vishing spiked 1,633% in Q1 2025 (Keepnet). Vishing now accounts for 60%+ of all phishing engagements, overtaking email as the primary phishing channel. The largest single vishing loss was $25 million (CrowdStrike 2024).
Social Engineering Timeline: The AI Inflection Point
Anatomy of a Modern Social Engineering Attack Chain
Modern social engineering chains multiple techniques across channels. Defending against any single step is insufficient — organizations need layered controls across the entire attack chain.
Social Engineering vs Other Attack Vectors
| Factor | Social Engineering | Ransomware | Exploits |
|---|---|---|---|
| Attack cost | Near zero (AI) | $$$$ (infrastructure) | $$$$$ (zero-day R&D) |
| Skill required | Low (AI assists) | Medium | High |
| Success rate | 2-36% (varies by channel) | Variable | High (if unpatched) |
| Share of breaches | 60-98% | 44% | 20% |
| Primary defence | Training + MFA | Backups + EDR | Patching |
| Avg cost per breach | $4.89M (BEC) | $5.08M | $4.24M |
Social engineering has the lowest barrier to entry, highest volume, and broadest breach share of any attack category. Sources: IBM 2025, Verizon DBIR 2025, CrowdStrike 2025, HBR 2024.
About This Data
This article draws from 76 statistics aggregated from 50+ authoritative sources including IBM Cost of a Data Breach, Verizon DBIR, CrowdStrike Global Threat Report, WEF Global Cybersecurity Outlook, FBI IC3, ISC2 Cybersecurity Workforce Study, Sophos, Gartner, Mandiant M-Trends, and Ponemon Institute reports.
Derived statistics (marked "Nathan House's Analysis") are computed by cross-referencing data from multiple sources — for example, comparing breach costs across industries using IBM data, or validating ransomware trends across Verizon, Sophos, and HIPAA Journal findings.
All statistics include inline source citations with links to primary sources. Data spans 2023-2026, with preference given to the most recent available figures. Last updated: May 2026.
How to Use This Data
Security professionals can use this data to build business cases for awareness training, justify phishing-resistant MFA deployment, and benchmark organizational vulnerability against industry baselines. The derived insights cross-reference multiple sources to surface what no single report shows.
This page is updated monthly as new reports are published. Bookmark it and return for the latest social engineering attack data. If you spot an outdated statistic or want to suggest a source, contact us.
Key sources used: Verizon Data Breach Investigations Report (DBIR) 2025, IBM Cost of a Data Breach Report 2025, FBI Internet Crime Complaint Center (IC3) Annual Report 2024, CrowdStrike Global Threat Report 2025, KnowBe4 Phishing By Industry Benchmarking Report 2025, Abnormal Security H1 2025 Threat Report, APWG Phishing Activity Trends Reports, Keepnet Labs Vishing Statistics Report, McAfee AI Voice Cloning Study, Eftsure Social Engineering Statistics, Sprinto Cybersecurity Survey, Arctic Wolf Security Operations Report 2025, World Economic Forum Global Cybersecurity Outlook 2025, HBR AI Phishing Study 2024, VIPRE Email Threat Trends 2024, and Hoxhunt Human Risk Benchmark 2025.
About the Author

Nathan House, StationX
Nathan House is a cybersecurity expert with 30 years of hands-on experience. He holds OSCP, CISSP, and CEH certifications, has secured £71 billion in UK mobile banking transactions, and has worked with clients including Microsoft, Cisco, BP, Vodafone, and VISA. Named Cyber Security Educator of the Year 2020 and a UK Top 25 Security Influencer 2025, Nathan is a featured expert on CNN, Fox News, and NBC. He founded StationX, which has trained over 500,000 students in cybersecurity.
Related Cybersecurity Statistics
Primary Data Sources for Social Engineering Statistics
Social Engineering Prevention Checklist
Based on the statistics above, these are the highest-impact actions organizations can take to reduce social engineering risk:
- Deploy security awareness training — reduces click rates by 86% in 12 months (KnowBe4 2025)
- Implement phishing-resistant MFA — FIDO2/passkeys eliminate credential phishing entirely (76% of orgs lack this)
- Establish BEC verification procedures — dual approval and out-of-band verification for financial transfers
- Run regular phishing simulations — including vishing and smishing scenarios, not just email
- Deploy AI-powered email security — to detect AI-generated phishing and BEC
- Create callback verification protocols — for any request involving money, credentials, or sensitive data
- Train specifically on pretexting — now 50%+ of incidents, requires scenario-based training
- Establish voice verification code words — for authorizing high-value transactions over the phone
