Phishing Statistics [2026]: Latest Attack Data & Trends

3.4 billion phishing emails hit inboxes every day — and 82.6% of them are now AI-generated. Whether you need phishing attacks statistics for a board presentation, security awareness training, or your own research, you've found the most comprehensive source available.
I've aggregated 76+ phishing and social engineering statistics from over 40 authoritative sources — Verizon DBIR, IBM, FBI IC3, CrowdStrike, APWG, KnowBe4, Sophos, and more — and cross-referenced them to produce original analysis you won't find in any single report. You'll find email phishing statistics, AI-powered attack data, click rates by industry, BEC losses, vishing and smishing trends, country targeting, and defense effectiveness across 14 sections below.
Key Phishing Statistics at a Glance
- 3.4 billion phishing emails sent daily; 82.6% are AI-generated (Keepnet/VIPRE)
- 21 seconds — median time to click a phishing link (Verizon DBIR 2025)
- $25 billion in annual global phishing losses (SentinelOne 2026)
- $2.77 billion in FBI-reported BEC losses from 21,442 complaints (FBI IC3 2024)
- 442% surge in vishing attacks in H2 2024 (CrowdStrike 2025)
- 54% click rate for AI spear phishing — matching human experts at 95% lower cost (HBR 2024)
- 36% of all data breaches involve phishing (Verizon DBIR 2025)
- <5% phishing susceptibility after comprehensive training (KnowBe4 2025)
Last updated: May 2026
📊 Key Phishing Numbers (2026)
3.4 billion phishing emails are sent every day, making phishing the single largest volume attack vector. APWG tracked 3.8 million phishing attacks across 2025, with Q2 2025 alone recording 1,130,393 attacks. 80,000+ phishing websites are detected annually, each lasting an average of just 12 hours before takedown (BlackBerry 2025). 57% of organisations face daily or weekly phishing attempts (GreatHorn 2025).
Phishing appears in 36% of all data breaches (Verizon DBIR 2025) and is the initial attack vector in 16% of breaches (IBM 2025). 80% of all reported security incidents are phishing-related (CSO Online). Global phishing losses total $25 billion annually (SentinelOne 2026), with $17,700 lost every minute (CSO Online). The FBI IC3 received 193,407 phishing complaints in 2024.
| Finding | Value | Source |
|---|---|---|
| Phishing emails sent daily | 3.4 billion | AAG IT / industry data |
| Phishing emails that are AI-generated | 82.6% | Keepnet Labs / VIPRE Security Group |
| Median time to click a phishing link | 21 seconds | Verizon DBIR 2025 |
| Average phishing click rate | 2.7% | Verizon DBIR 2025 |
| Phishing in data breaches | 36% | Verizon DBIR 2025 |
| Phishing as initial breach vector | 16% | IBM Cost of a Data Breach Report 2025 |
| Security incidents that are phishing | 80% | CSO Online |
| Lost to phishing every minute | $17,700 | CSO Online |
| Annual global phishing losses | $25B | CDNetworks / SentinelOne |
| FBI IC3 phishing complaints (2024) | 193,407 | FBI Internet Crime Report 2024 |
| Phishing attacks tracked annually | 3.8 million | APWG Phishing Activity Trends |
| Phishing scams reported (Q4 2024) | 989,123 | APWG Phishing Activity Trends Q4 2024 |
| Phishing attacks (Q2 2025) | 1,130,393 | APWG Phishing Activity Trends Q2 2025 |
| Orgs seeing daily/weekly phishing | 57% | GreatHorn |
| Phishing websites detected (+22% YoY) | 80,000+ | Group-IB 2025 |
The Phishing Firehose
Approximately 39K per second of phishing emails are sent every second. That's 39K per second — enough to fill a 70,000-seat stadium with phishing emails in under two seconds. (AAG IT / industry data)
Phishing at a Glance: The Numbers That Matter
Every 39,000 phishing emails per second, every 92 million clicks per day, every $17,700 lost per minute — these numbers describe an industrial-scale operation. Phishing is no longer the domain of lone operators sending badly spelled emails from Nigerian princes. It is a professional, AI-augmented industry with specialised roles: access brokers who sell compromised credentials, campaign operators who design and distribute phishing emails, cashout teams who convert stolen data into money, and ransomware groups who use phishing as an entry point for multi-million-dollar extortion.
The professionalisation of phishing is reflected in the infrastructure. Phishing-as-a-Service (PhaaS) kits are sold on dark web marketplaces, complete with email templates, credential-harvesting landing pages, evasion techniques, and customer support. These kits lower the technical bar even further — an attacker with no coding ability can launch a sophisticated phishing campaign for under $100.
Phishing Is the #1 Breach Entry Point
Cross-referencing IBM (16% initial vector), Verizon (36% of breaches), and CSO Online (80% of incidents), phishing appears in some form across the majority of all security events. When you add BEC (27% of Arctic Wolf incidents) and social engineering (98% of attacks, Sprinto), the picture is clear: phishing is not just a threat category — it's the primary gateway to every other attack type.
📨 How Many Phishing Emails Are Sent Daily?
The scale of phishing is staggering. 3.4 billion phishing emails flood inboxes daily — that's approximately 39,000 per second. APWG tracked 3.8 million phishing attacks in 2025, with Q2 alone recording over 1.1 million. Phishing websites detected rose 22% year-over-year to 80,000+ (Group-IB 2025), though the average site lasts only 12 hours before takedown (BlackBerry 2025).
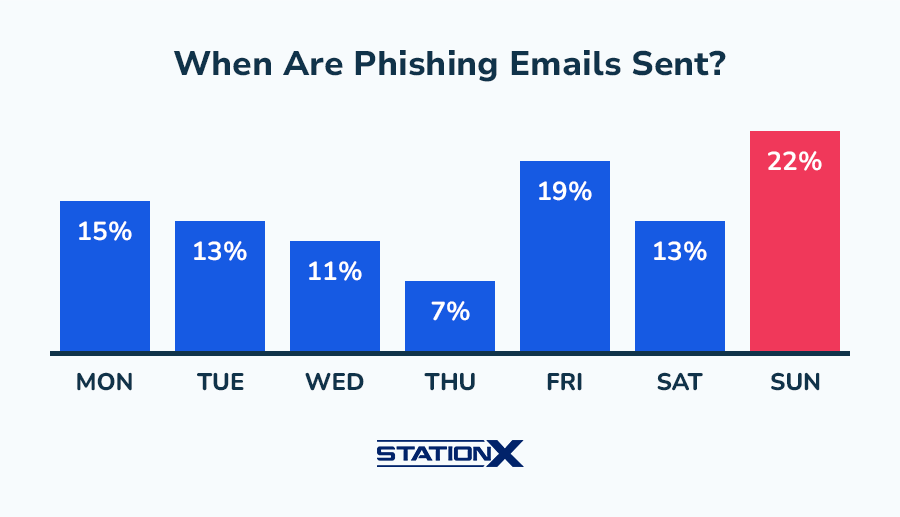
Phishing emails peak on Sundays (22% of weekly volume) and Fridays (19%), suggesting attackers time campaigns for when recipients are less vigilant (StationX analysis). 86% of malicious spam uses embedded links rather than attachments (VIPRE 2024), reflecting a shift toward credential-harvesting landing pages.
| Finding | Value | Source |
|---|---|---|
| Phishing emails sent daily worldwide | 3.4 billion | AAG IT / industry data |
| Phishing attacks tracked (annual) | 3.8 million | APWG Phishing Activity Trends |
| Phishing scams (Q4 2024) | 989,123 | APWG Phishing Activity Trends Q4 2024 |
| Phishing attacks (Q2 2025) | 1,130,393 | APWG Phishing Activity Trends Q2 2025 |
| Phishing websites detected | 80,000+ | Group-IB 2025 |
| Average phishing site lifespan | 12 hours | BlackBerry Global Threat Intelligence 2025 |
| Orgs facing daily/weekly phishing | 57% | GreatHorn |
| Peak phishing day (Sunday) | 22% | StationX / Industry data |
| Friday phishing share (2nd highest) | 19% | StationX / Industry data |
| Malspam using links vs attachments | 86% | VIPRE Security Group Q2 2024 |
$1.06M Lost to Phishing Every Hour
At $17,700 per minute (CSO Online), phishing drains $1.06M per hour and $25.5M per day from the global economy. That's $25 billion annually — making phishing alone costlier than most countries' entire cybercrime losses.
Phishing Volume Trend
The trajectory is clear: phishing volume has grown every year for the past decade. APWG's data shows phishing attacks rising from approximately 1 million in 2020 to 3.8 million in 2025. The proliferation of AI tools has accelerated this growth — generating convincing phishing emails at scale requires minimal human effort when large language models handle the writing, personalisation, and translation.
The 12-hour average phishing site lifespan (BlackBerry 2025) reflects both improving takedown capabilities and attacker adaptation. Modern phishing campaigns use disposable infrastructure — spinning up hundreds of sites simultaneously, knowing most will be taken down quickly. The sites that survive even a few hours capture enough credentials to justify the cost, especially when the average click time is just 21 seconds from email delivery.
Why Sundays and Fridays?
Phishing emails peak on Sundays (22%) and Fridays (19%) for strategic reasons. Sunday campaigns exploit reduced IT staffing and weekend inboxes — recipients checking email casually on personal devices are less likely to scrutinise sender addresses or hover over links. Friday campaigns target end-of-week fatigue, when employees rush through overflowing inboxes before the weekend. Thursday (7%) sees the lowest phishing volume, possibly because mid-week alertness is highest.
🤖 AI-Powered Phishing
82.6% of phishing emails detected between September 2024 and February 2025 utilised AI (Keepnet/VIPRE). AI-automated spear phishing achieves a 54% click-through rate — matching skilled human attackers — while reducing campaign costs by 95%+ (HBR 2024). 37% of breaches now involve AI-generated phishing as the attack method (IBM 2025). 40% of BEC emails in Q2 2024 were identified as AI-crafted (VIPRE 2024).
80%+ of social engineering activity is now powered by AI (Abnormal Security 2025). The convergence of generative AI with phishing has fundamentally changed the economics of attacks: campaigns that previously required days of research per target can now be automated across thousands of targets simultaneously, with personalised content that exploits publicly available information from LinkedIn, social media, and corporate websites.
How AI Changed the Economics of Phishing
Before generative AI, a targeted spear phishing campaign required a human attacker to research each target individually — reading their LinkedIn profile, identifying colleagues, mimicking writing styles, and crafting a personalised email. This took hours per target, limiting attacks to high-value individuals. AI has collapsed this cost to near zero: a single operator can now generate thousands of personalised spear phishing emails per hour, each tailored to the recipient's role, company, and recent activity.
The 95%+ cost reduction (HBR 2024) means phishing campaigns that previously required dedicated criminal teams costing $50,000+ per operation can now be run for under $5. The barrier to entry has dropped so far that even unsophisticated actors can launch highly effective attacks. The result: 82.6% of detected phishing emails now show signs of AI generation (Keepnet/VIPRE 2025), and the trend is accelerating.
| Finding | Value | Source |
|---|---|---|
| Phishing emails utilizing AI | 82.6% | Keepnet Labs / VIPRE Security Group |
| AI spear phishing click rate | 54% | Harvard Business Review / Heiding, Schneier et al. |
| AI phishing cost reduction vs manual | 95%+ | Harvard Business Review / Heiding, Schneier et al. |
| BEC emails that are AI-generated | 40% | VIPRE Security Group Q2 2024 |
| AI phishing as attacker method | 37% | IBM Cost of a Data Breach Report 2025 |
| Social eng powered by AI | 80%+ | Abnormal Security / Xceedance |
AI Matches Human Experts at 20x Lower Cost
AI-automated spear phishing achieves a 54% click-through rate — matching skilled human attackers — while reducing campaign costs by 95%+ (HBR 2024). At scale, AI can generate personalised phishing emails for thousands of targets simultaneously, something previously requiring dedicated human operators per target.
AI Phishing Detection Challenges
Traditional phishing detection relied on identifying tell-tale signs: grammatical errors, suspicious sender addresses, mismatched URLs, and generic greetings. AI-generated phishing emails eliminate most of these signals. The prose is grammatically perfect, culturally appropriate, and personalised to the recipient. AI tools can generate phishing emails in any language with native-level fluency, enabling attackers to target regions that were previously protected by language barriers.
Security vendors are responding with AI-based detection — using machine learning to identify subtle patterns in email headers, sending behaviour, and content that distinguish AI-generated phishing from legitimate communications. But this is an arms race: as detection improves, attackers adapt their generation techniques. The 82.6% AI-generated figure (Keepnet/VIPRE 2025) suggests attackers currently have the upper hand in this race.
The AI Phishing Arms Race
Attackers use AI to generate phishing. Defenders use AI to detect it. But at 82.6% AI-generated email volume and a 54% click rate, the current balance favours attackers. The defensive advantage lies in phishing-resistant MFA and user training — controls that work regardless of email quality.
🖱️ How Many People Fall for Phishing Scams?
The average phishing email click rate is 2.7% (Verizon DBIR 2025). That sounds low — until you multiply it by 3.4 billion daily emails. The result: approximately 92 million successful clicks per day, each a potential breach entry point. The median time to click is just 21 seconds from delivery (Verizon DBIR 2025).
The median time to report a phishing email is 28 minutes (Verizon DBIR 2025) — giving attackers a 27.6-minute head start between the first click and the first alert. 60% of phishing incidents involve identity-based attacks (Cisco 2025), where stolen credentials provide immediate access to systems. After comprehensive security awareness training, phishing susceptibility drops to under 5% (KnowBe4 2025).
| Finding | Value | Source |
|---|---|---|
| Median time to click phishing link | 21 seconds | Verizon DBIR 2025 |
| Average phishing click rate | 2.7% | Verizon DBIR 2025 |
| Median time to report phishing | 28 minutes | Verizon DBIR 2025 |
| AI phishing click rate (matches human) | 54% | Harvard Business Review / Heiding, Schneier et al. |
| Susceptibility after training | <5% | KnowBe4 Financial Sector Threats Report 2025 |
| Identity-based phishing incidents | 60% | Cisco Cybersecurity Readiness Index 2025 |
92 Million Clicks Per Day
3.4 billion daily phishing emails × 2.7% click rate = approximately 91.8M successful phishing clicks per day. Each click is a potential breach entry point — and it takes just 21 seconds for the first victim to click. (AAG IT / industry data, Verizon DBIR 2025)
27.6-Minute Head Start for Attackers
The median time to click a phishing link is 21 seconds, but the median time to report it is 28 minutes (Verizon DBIR 2025). That gives attackers a 27.6-minute window between the first compromise and the first alert — long enough to move laterally, exfiltrate data, or deploy ransomware.
The 21-Second Problem
21 seconds. That's the median time from phishing email delivery to the first click (Verizon DBIR 2025). To put this in perspective: most security teams cannot even generate an alert in 21 seconds, let alone respond to one. By the time an email security gateway flags a suspicious message for review, the first victim has already clicked, entered credentials, and potentially handed over access to the entire organisation.
The 28-minute reporting gap makes this worse. If the first click happens at 21 seconds and the first report happens at 28 minutes, attackers have a 27.6-minute window of undetected access. In that window, automated attack frameworks can harvest credentials, move laterally through the network, exfiltrate sensitive data, or deploy ransomware. The solution is not just faster detection — it's pre-click prevention through email filtering, URL sandboxing, and phishing-resistant MFA that limits the damage even when users click.

Phishing Type Explorer
Select a phishing type to see its key statistics and characteristics.
📱 Vishing & Smishing Trends
Vishing (voice phishing) surged 442% from H1 to H2 2024 (CrowdStrike 2025), making it the fastest-growing phishing vector. AI voice cloning enables attackers to replicate a person's voice from just 3 seconds of audio (McAfee 2024). The largest vishing-related scam was a $25 million deepfake CFO video call (CrowdStrike 2024).
Smishing (SMS phishing) accounts for 35% of all phishing attacks (SentinelOne 2026) and surged 40% year-over-year (Keepnet 2025). 19% of breaches now originate from smishing or vishing combined (Verizon DBIR 2025). 83% of phishing websites specifically target mobile devices (Zimperium 2024), reflecting the shift to mobile-first attack strategies.
| Finding | Value | Source |
|---|---|---|
| Vishing attack surge (H1→H2 2024) | 442% | CrowdStrike 2025 Global Threat Report |
| Voice phishing increase YoY | 442% | CrowdStrike 2025 Global Threat Report |
| Smishing/vishing in breaches | 19% | Verizon DBIR 2025 |
| Smishing share of phishing attacks | 35% | SentinelOne / Industry Reports |
| Smishing surge YoY | 40% | APWG / Keepnet |
The Multi-Channel Phishing Storm
Email phishing (3.4B/day), vishing (+442%, CrowdStrike 2025), and smishing (+40%, Keepnet 2025) are converging into a coordinated multi-channel threat. 35% of phishing now uses SMS/messaging apps (SentinelOne 2026), and 19% of breaches originate from smishing or vishing (Verizon DBIR 2025). Traditional email-only defenses miss two-thirds of the attack surface.
The AI Voice Cloning Threat
The 442% vishing surge is directly linked to advances in AI voice cloning. McAfee reports that just 3 seconds of audio — from a YouTube video, conference recording, or voicemail greeting — is enough to create a convincing voice clone (McAfee 2024). Attackers use these clones to impersonate executives, requesting urgent wire transfers or sensitive information via phone calls. The $25 million deepfake CFO scam (CrowdStrike 2024) used video deepfake technology on a live call — the finance employee believed they were speaking with their actual CFO.
Smishing exploits a different vulnerability: trust in SMS. Text messages carry more implicit authority than email — a bank alert, delivery notification, or government notice via SMS triggers faster responses with less scrutiny. 83% of phishing websites are now designed for mobile screens (Zimperium 2024), optimised for the smaller display where URL inspection is harder. QR code phishing (+400%, Hoxhunt 2025) bridges physical and digital attack surfaces, appearing in printed materials, emails, and even fake parking meters.
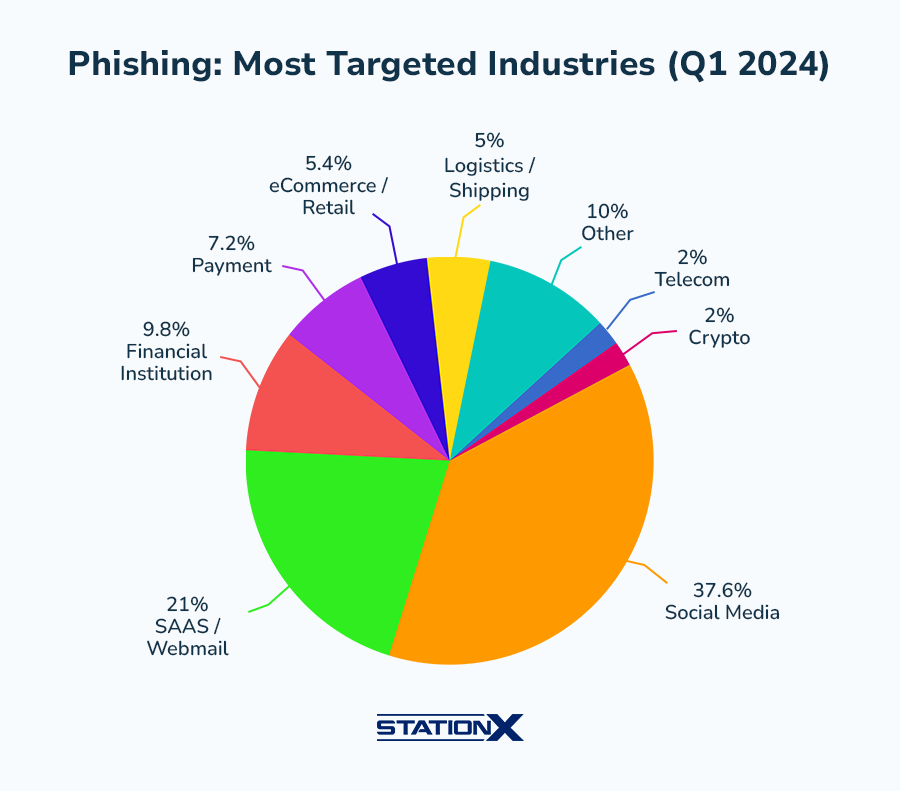
🏥 Phishing Targets by Industry
Phishing is the initial breach vector in 16% of all data breaches (IBM 2025) and appears in 36% of breaches overall (Verizon DBIR 2025). 33% of cloud-related security incidents originate from phishing (IBM X-Force 2025). The phishing insider incident cost averages $804,997 (Ponemon 2025), and 55% of insider incidents are triggered by phishing.

Industry targeting patterns show that phishing is not evenly distributed. Financial services face the highest attack frequency — 300x more attacks than other industries (KnowBe4 2025) — because the direct path from credential theft to monetary gain is shortest. Healthcare is heavily targeted due to the value of medical records and the urgency culture that makes staff susceptible to "urgent action required" messages. Education faces the highest click rates due to a transient population (students, adjunct faculty) with varying security awareness levels.
Cloud-related phishing (33% of cloud incidents, IBM X-Force 2025) targets organisations migrating to cloud platforms, exploiting confusion about new login portals and credential management. Phishing-triggered insider incidents cost $804,997 on average (Ponemon 2025), and 55% of all insider incidents begin with a phishing email — making phishing the primary gateway to insider threats as well.
| Finding | Value | Source |
|---|---|---|
| All security incidents that are phishing | 80% | CSO Online |
| Phishing as initial breach vector | 16% | IBM Cost of a Data Breach Report 2025 |
| Cloud incidents from phishing | 33% | IBM X-Force |
| Phishing insider incident cost | $804,997 | Ponemon Insider Threat Report 2025 |
| Insider incidents triggered by phishing | 55% | Ponemon Insider Threat Report 2025 |
Industry Click Rate Comparison
Phishing click rates vary significantly by industry, driven by workforce composition, security culture, and attack sophistication. Education consistently shows the highest baseline click rates (~5.1%) due to transient student populations, adjunct faculty with limited security training, and open academic environments that prioritise accessibility over restriction. Financial services faces the highest attack frequency but has lower click rates (~4.2%) thanks to regulatory-driven security awareness programs.
Technology companies show the lowest baseline click rates (~2.1%), reflecting a workforce more attuned to cybersecurity risks and more likely to recognise phishing indicators. Healthcare (~3.5%) and government (~3.8%) fall in the middle — both face sophisticated targeting but have varying levels of security awareness maturity. Retail (~3.9%) is increasingly targeted as e-commerce grows, with attackers impersonating delivery services and payment platforms.
Phishing in Supply Chain Attacks
Phishing is increasingly used as the initial vector for supply chain compromises. Attackers target employees at third-party vendors, MSPs, or software suppliers — organisations that often have privileged access to their clients' systems. A single compromised vendor account can cascade to dozens or hundreds of downstream organisations. IBM reports that third-party breaches doubled year-over-year to 30% of all incidents, with supply chain compromises costing $4.91 million on average.
The supply chain phishing attack surface is expanding as organisations adopt more SaaS tools, each with its own authentication system. Every vendor login page is a potential phishing target. Organisations should require phishing-resistant MFA for all vendor access, conduct security assessments of critical suppliers' email security posture, and implement conditional access policies that restrict vendor access by IP, device, and geography.
Phishing Risk Estimator
Estimate your annual phishing exposure based on industry and employee count.
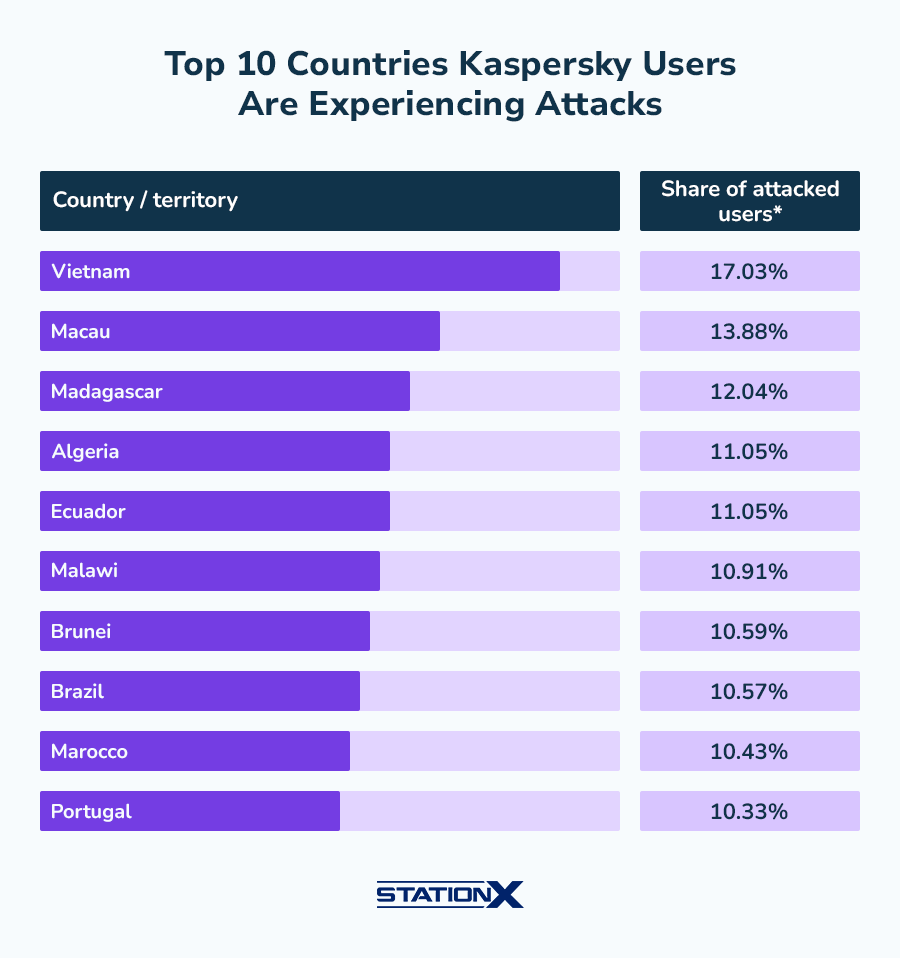
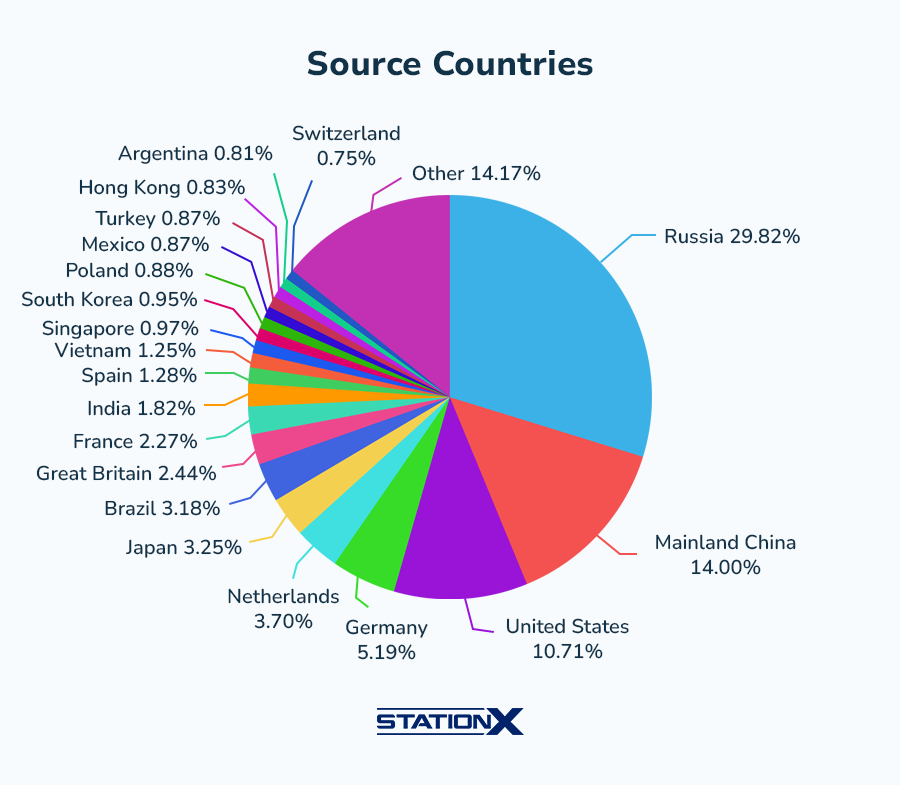
🌍 Phishing Targets by Country
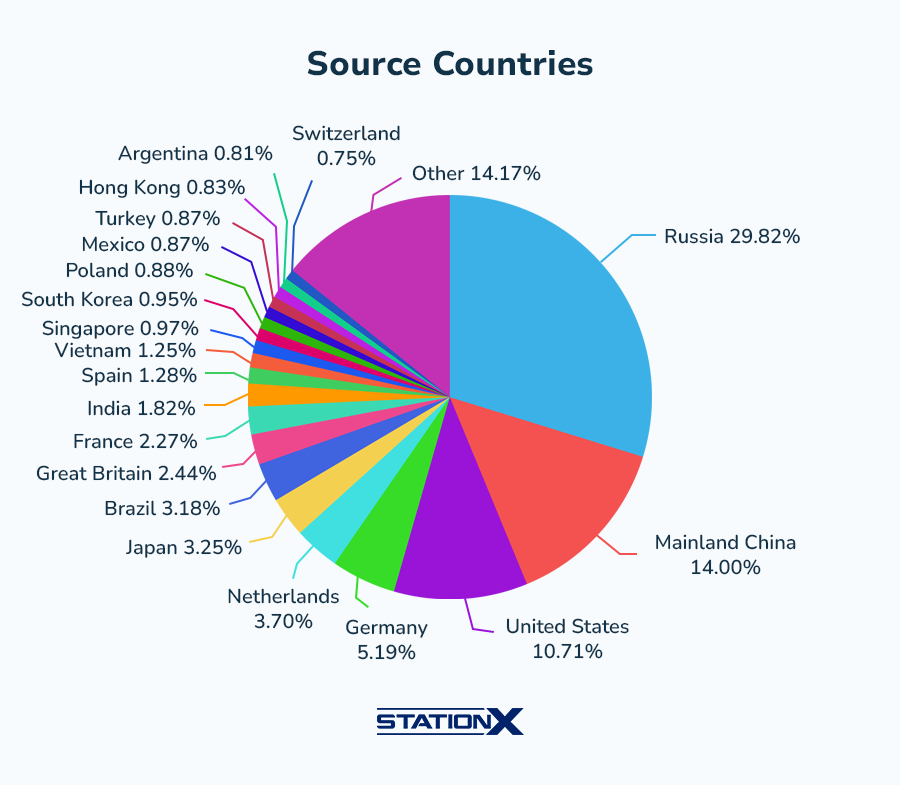
The United States is the primary target for phishing attacks, with the FBI IC3 receiving 193,407 phishing complaints in 2024. US BEC losses alone totalled $2.77 billion. Cryptocurrency-related phishing accounted for an additional $28.5 million in FBI-reported losses. The Netherlands (17.7%), Russia (13.7%), and other countries show distinct targeting patterns based on financial sector presence and digital infrastructure maturity.
| Finding | Value | Source |
|---|---|---|
| FBI phishing complaints (US, 2024) | 193,407 | FBI Internet Crime Report 2024 |
| FBI BEC losses (US, 2024) | $2.77B | FBI Internet Crime Report 2024 |
| FBI crypto phishing losses (US) | $28.5M | FBI Internet Crime Report 2024 |
Regional Phishing Patterns
Phishing targeting varies significantly by region. The Netherlands receives 17.7% of global phishing emails — disproportionate to its population — due to its role as a major European financial and logistics hub. Russia (13.7%) and other Eastern European countries see high volumes both as targets and as source countries. The APAC region faces distinct phishing campaigns tailored to local languages and banking systems, with mobile-first attacks dominating in markets where smartphone penetration exceeds desktop usage.
Cryptocurrency-related phishing is a growing subset, with the FBI reporting $28.5 million in crypto phishing losses in 2024 (FBI IC3). These attacks mimic legitimate cryptocurrency exchanges, wallets, and DeFi platforms, exploiting the irreversible nature of cryptocurrency transactions. Once funds are transferred to an attacker's wallet, recovery is virtually impossible.
Top Phishing Brands and Impersonation Targets
Attackers impersonate the brands people trust most. Microsoft, Google, Apple, Amazon, and major banks are consistently the most impersonated brands in phishing campaigns. Microsoft 365 phishing is particularly prevalent because compromising a Microsoft account gives attackers access to email, OneDrive, SharePoint, and Teams — the entire digital workplace. Google Workspace phishing follows the same logic.
Delivery service impersonation (DHL, FedEx, Royal Mail) has surged alongside the growth of e-commerce. "Your package is being held" and "delivery attempted" messages generate urgency without requiring any prior relationship with the target. Government impersonation (HMRC, IRS, tax agencies) spikes during tax seasons. Banking phishing ("unusual activity detected on your account") remains one of the highest-conversion phishing categories because it triggers immediate fear of financial loss.
🔗 Phishing Delivery Methods
86% of malicious spam now uses embedded links rather than attachments (VIPRE 2024), reflecting a strategic shift toward credential-harvesting landing pages that evade attachment-scanning defenses. QR code phishing (quishing) increased 400% between 2023 and 2025 (Hoxhunt), exploiting the trust users place in QR codes and the difficulty of previewing URLs on mobile devices.
60% of phishing incidents are identity-based (Cisco 2025), targeting credentials rather than deploying malware. The average phishing site lasts just 12 hours before takedown (BlackBerry 2025), but that's enough time — with a 21-second click time and 92 million daily clicks, most damage occurs within the first hour. 83% of phishing websites specifically target mobile users (Zimperium 2024).
| Finding | Value | Source |
|---|---|---|
| Malspam using links vs attachments | 86% | VIPRE Security Group Q2 2024 |
| QR code phishing increase | 400% | Hoxhunt Phishing Trends Report |
| Identity-based phishing incidents | 60% | Cisco Cybersecurity Readiness Index 2025 |
| Average phishing site lifespan | 12 hours | BlackBerry Global Threat Intelligence 2025 |
| Mobile-targeted phishing sites | 83% | Zimperium Mobile Threat Report 2024 |
The QR Code Phishing Explosion
QR code phishing (quishing) deserves special attention. The 400% increase (Hoxhunt 2025) reflects a fundamental gap in email security: most email gateways scan URLs and attachments but cannot interpret QR codes embedded as images. Attackers exploit this by embedding malicious QR codes in otherwise clean emails, bypassing traditional link-scanning defenses entirely. When users scan the QR code with their phone, they're redirected to a credential-harvesting site outside the corporate network's security controls.
Identity-based phishing (60% of incidents, Cisco 2025) represents the convergence of phishing with credential theft. Rather than deploying malware, modern phishing focuses on harvesting usernames and passwords through convincing login page replicas. With stolen credentials, attackers gain legitimate access that bypasses most perimeter defenses — no exploit needed, no malware to detect, just a valid login from a "trusted" user.
Adversary-in-the-Middle (AitM) Phishing
A sophisticated evolution of credential phishing is the Adversary-in-the-Middle (AitM) attack, where the phishing site acts as a real-time proxy between the victim and the legitimate login page. The victim enters their credentials and even their MFA token — both are captured and immediately relayed to the real site. The attacker gains a fully authenticated session, bypassing standard MFA. AitM phishing kits are now available as commodity tools on dark web marketplaces, making this advanced technique accessible to low-skill attackers.
Only phishing-resistant MFA (FIDO2/passkeys, hardware security keys) defeats AitM attacks, because these methods verify the actual domain of the login page cryptographically. If the domain doesn't match, the authentication fails — even if the user is fooled. This is why the industry is rapidly moving toward passwordless authentication using passkeys, which eliminate the credential-harvesting attack surface entirely.
💰 Cost of Phishing Attacks
Global phishing losses total $25 billion annually (SentinelOne 2026). $17,700 is lost to phishing every minute (CSO Online). The average BEC attack costs $4.67 million (IBM 2025), while the average BEC loss per incident is $160,000+ (Arctic Wolf 2025). Phishing-related insider incidents average $804,997 each (Ponemon 2025).
71% of organisations expect a business-disrupting cyber incident in the next 12-24 months (Cisco 2025), with phishing as the most likely entry point. The cost compounds across the attack chain: a successful phishing click leads to credential theft, lateral movement, data exfiltration, or ransomware deployment — each adding to the total breach cost.
| Finding | Value | Source |
|---|---|---|
| Annual global phishing losses | $25B | CDNetworks / SentinelOne |
| Lost to phishing every minute | $17,700 | CSO Online |
| Average BEC attack cost | $4.67M | IBM / HoxHunt |
| Average BEC loss per incident | $160,000+ | Arctic Wolf Threat Report 2025 |
| Phishing insider incident cost | $804,997 | Ponemon Insider Threat Report 2025 |
| Orgs expecting disruptive incident | 71% | Cisco Cybersecurity Readiness Index 2025 |
The Compounding Cost Chain
Phishing rarely ends at the initial click. The cost compounds through a chain of consequences: credential theft leads to account compromise, which enables lateral movement, data exfiltration, and often ransomware deployment. IBM reports that breaches originating from phishing take an average of 241 days to identify and contain — one of the longest lifecycles of any attack vector. Each additional day of undetected access increases the total breach cost.
For organisations, the true cost of phishing includes direct financial losses, incident response costs, regulatory fines, legal expenses, reputational damage, customer churn, and business disruption. The $25 billion annual figure captures only the measurable direct losses. Including indirect costs — productivity loss from security lockdowns, executive time spent on breach response, increased insurance premiums — the total impact is substantially higher.
The Phishing Attack Chain
Phishing email (3.4B/day) → Click (21 sec) → Credential harvest → Account compromise → Lateral movement → Data exfiltration or ransomware → Average breach cost: $4.44M (IBM 2025)
🛡️ Phishing Defense & Training
Security awareness training reduces phishing susceptibility to under 5%, down from an industry baseline of approximately 33% (KnowBe4 2025). That's an 85%+ reduction in click-through rates. The median time to report phishing is 28 minutes (Verizon DBIR 2025), but trained users report faster. The gap between click time (21 seconds) and report time (28 minutes) represents the critical window for attacker exploitation.
Phishing sites last an average of 12 hours before takedown (BlackBerry 2025), underscoring the importance of pre-click defenses (email filtering, URL sandboxing) over post-click remediation. Multi-factor authentication — particularly phishing-resistant MFA (FIDO2/passkeys) — provides the strongest defense against credential-harvesting phishing, even when users click.
| Finding | Value | Source |
|---|---|---|
| Susceptibility after training | <5% | KnowBe4 Financial Sector Threats Report 2025 |
| Median time to report phishing | 28 minutes | Verizon DBIR 2025 |
| Median time to click (21 sec) | 21 seconds | Verizon DBIR 2025 |
| Phishing site lifespan (12 hrs) | 12 hours | BlackBerry Global Threat Intelligence 2025 |
Training Cuts Susceptibility by 85%+
KnowBe4 reports phishing susceptibility drops to under 5% after comprehensive security awareness training — down from an industry average baseline of ~33% before training. The median time to report phishing (28 minutes) also improves dramatically with trained users. The ROI case for training is now quantifiable: fewer clicks means fewer breaches.
Layered Phishing Defense Strategy
Effective phishing defense requires a layered approach. No single control stops all phishing — the 2.7% click rate persists even with email filtering because attackers constantly evolve their techniques. The most effective defence stack combines: (1) email gateway filtering with AI-based detection, (2) URL sandboxing and real-time link analysis, (3) regular security awareness training to reduce susceptibility below 5%, (4) phishing-resistant MFA (FIDO2/passkeys) to prevent credential exploitation even after a click, and (5) endpoint detection to catch post-compromise lateral movement.
The economics favour defense: security awareness training costs a fraction of a single phishing breach. Reducing click rates from the industry baseline (~33%) to under 5% with comprehensive training eliminates 85%+ of the risk surface. Adding phishing-resistant MFA closes most of the remaining gap — even if a user clicks and enters credentials on a fake site, the attacker cannot use those credentials without the physical security key or passkey.
The Defense ROI
Security awareness training: ~$25/employee/year. Phishing-resistant MFA: ~$5/user/month. Average phishing breach cost: $4.44M. The math is straightforward — investing $100K in training and MFA for a 1,000-person organisation eliminates 90%+ of the risk from phishing attacks costing millions.
Incident Response for Phishing
When phishing succeeds — and it will, despite the best defenses — the speed of response determines the damage. Organisations with a documented incident response plan specifically for phishing events contain breaches faster and at lower cost. The response playbook should include: immediate credential reset for compromised accounts, session token revocation, email quarantine of additional messages from the same campaign, forensic analysis of what data was accessed, and notification to affected parties.
Automated response orchestration (SOAR platforms) can execute the first four steps within minutes of a confirmed phishing compromise, dramatically reducing the attacker's operational window. When the median time from click to report is 28 minutes, automated response can close the gap that manual processes cannot. Organisations that combine user training, phishing-resistant MFA, email filtering, and automated incident response achieve the strongest defensive posture against phishing attacks.
Phishing Simulation Programs
The most effective security awareness programs include regular phishing simulations — controlled phishing campaigns that test employee awareness without real risk. These simulations measure click rates, report rates, and susceptibility trends over time. KnowBe4's data showing susceptibility dropping to under 5% after training comes from organisations running monthly simulation campaigns combined with just-in-time training for employees who click.
Simulation programs work best when they evolve: initial tests use obvious phishing indicators, progressively introducing more sophisticated techniques including AI-generated content, impersonation of internal employees, and multi-channel attacks (email followed by a "verification" phone call). Organisations that run quarterly simulations see 50-60% improvement in the first year. Those running monthly simulations with immediate feedback see 70-80%+ improvement within 6 months.
⚠️ Biggest Phishing Attacks & Notable Campaigns
The biggest phishing attacks in recent years demonstrate how the threat has evolved from mass-blast emails to sophisticated, multi-channel campaigns leveraging AI, deepfakes, and social engineering at scale. Here are the most significant:
$25M Deepfake CFO Scam (2024)
Attackers used AI-generated deepfake video to impersonate a company's CFO on a video call, convincing a finance employee to transfer $25 million. The attack combined vishing, deepfake technology, and social engineering in a single coordinated campaign. Multiple participants on the call were deepfaked — only the victim was real (CrowdStrike 2024).
$1.5B Lazarus Group ByBit Heist (2025)
North Korea's Lazarus Group executed a $1.5 billion cryptocurrency heist against ByBit in 2025, believed to have originated from a spear phishing attack targeting an exchange employee. The attack demonstrates how a single phishing email can cascade into the largest cryptocurrency theft in history.
442% Vishing Surge (H2 2024)
CrowdStrike documented a 442% surge in voice phishing between H1 and H2 2024, driven by AI voice cloning tools that can replicate any voice from 3 seconds of audio. This was not a single campaign but an industry-wide shift — attackers increasingly use phone calls to bypass email security filters entirely, targeting IT help desks, finance teams, and executives.
QR Code Phishing Explosion (+400%)
QR code phishing (quishing) increased 400% between 2023 and 2025 (Hoxhunt). Attackers embed malicious QR codes in emails, printed flyers, and even over legitimate QR codes on parking meters and restaurant menus. Users scan with mobile devices, bypassing desktop email security controls and landing on credential-harvesting sites designed for mobile screens.
AI-Generated BEC Surge (2024-2025)
40% of BEC emails in Q2 2024 were identified as AI-generated (VIPRE). BEC volume surged 54% in H1 2025 vs 2023 (Abnormal Security). AI-generated BEC attacks are nearly impossible to distinguish from legitimate executive communications, with personalised writing styles, contextually relevant content, and grammatically perfect prose across multiple languages.
Phishing vs Other Attack Vectors
Phishing is not just one attack vector among many — it's the gateway to most others. Ransomware, credential theft, business email compromise, insider threats, and supply chain attacks frequently begin with a phishing email. IBM reports phishing as the initial vector in 16% of breaches, but its downstream impact is far broader: stolen credentials from phishing enable 53% of all breaches (Verizon DBIR 2025), and phishing triggers 55% of insider incidents (Ponemon 2025).
Phishing: The Breach Gateway
- 36% of breaches involve phishing (Verizon)
- 16% initial breach vector (IBM)
- 55% of insider incidents start with phishing
- 68% of cyberattacks originate from email
What Phishing Enables
- Credential theft → 53% of breaches
- Ransomware deployment
- BEC wire fraud ($2.77B/year)
- Supply chain compromise
The Evolution of Phishing Tactics
Phishing has evolved through distinct generations. First-generation attacks (early 2000s) were mass-blast emails with obvious indicators — foreign princes, lottery winnings, Nigerian bank transfers. Second-generation attacks (2010s) introduced brand impersonation, landing page cloning, and industry-targeted campaigns. Third-generation attacks (2020s) leverage AI content generation, multi-channel delivery, AitM credential proxying, and deepfake technology. Each generation made the previous generation's defenses insufficient.
The current fourth-generation threat combines all previous capabilities with autonomous AI agents that can conduct entire social engineering campaigns end-to-end: researching targets, crafting personalised messages, adapting in real-time to responses, and even conducting follow-up calls using voice clones. While this capability is still emerging, the building blocks are all commercially available. Security planning for 2026-2028 must account for this trajectory.
📲 Mobile Phishing Statistics
83% of phishing websites specifically target mobile devices (Zimperium 2024). Smishing accounts for 35% of all phishing attacks (SentinelOne 2026), and the smishing surge hit 40% year-over-year growth (Keepnet 2025). Mobile phishing is harder to detect: smaller screens hide URL previews, and SMS messages carry more implicit trust than email. QR code phishing (+400%, Hoxhunt 2025) further exploits mobile-first behaviour.
The mobile attack surface extends beyond SMS. Messaging apps (WhatsApp, Telegram, Slack), social media DMs, and even calendar invites are used as phishing delivery channels. Mobile banking trojans have surged (Kaspersky 2024), often delivered through smishing links. Organisations relying solely on desktop email security miss a significant portion of the phishing threat landscape.
Why Mobile Phishing Works
Mobile devices create a perfect environment for phishing success. Smaller screens hide URL bars and make it harder to inspect links before clicking. Push notifications create urgency — a text message reading "Your account has been compromised, verify now" triggers immediate action on a device designed for instant response. Mobile browsers often lack the security extensions available on desktop. And personal devices typically operate outside corporate security controls, meaning no email gateway, no URL sandboxing, and no endpoint detection.
The convergence of work and personal communication on mobile devices compounds the risk. Employees accessing corporate email, Slack, Teams, and other work tools on the same device where they receive personal SMS and social media messages means a smishing attack can reach a corporate user through a completely unmonitored channel. QR code phishing bridges physical spaces — attackers have placed malicious QR codes over legitimate ones on parking meters, restaurant menus, and even corporate visitor badges.
Mobile Phishing Defense Gaps
Most enterprise security stacks were designed for desktop environments. Email security gateways filter corporate email, but they cannot scan personal SMS messages, WhatsApp conversations, or social media DMs on employee phones. This creates a fundamental visibility gap: the device that has the most access to corporate systems (mobile, with SSO apps, email, Slack, VPN) is also the device with the least security monitoring.
Mobile threat defense (MTD) solutions and mobile device management (MDM) platforms can close some of these gaps by scanning URLs before they open in mobile browsers, detecting phishing apps, and enforcing security policies on managed devices. However, adoption remains low — many organisations still treat mobile security as an afterthought. Given that 83% of phishing sites target mobile users (Zimperium 2024) and 35% of phishing uses SMS/messaging (SentinelOne 2026), this gap represents one of the largest unaddressed phishing risk surfaces.
📅 How Often Do Phishing Attacks Happen?
Phishing emails peak on Sundays (22% of weekly volume) and Fridays (19%), with Thursday being the lowest day at 7% (StationX analysis). This pattern suggests attackers target weekends and end-of-week fatigue, when recipients are less likely to scrutinise emails carefully. Monday (15%) and Tuesday (13%) see moderate volumes, while Wednesday (11%) and Saturday (13%) fall in between.
These timing patterns have direct implications for security operations. SOC teams should increase email monitoring coverage on Sundays and Fridays, when phishing volume peaks. Automated email security rules can apply stricter filtering during high-risk periods. Security awareness training should specifically address weekend and end-of-week vigilance, since attackers deliberately time campaigns to exploit periods of reduced attention.
Time-of-day patterns also matter. Phishing emails timed to arrive early Monday morning — when employees face hundreds of accumulated weekend emails — achieve higher click rates than those sent mid-afternoon on a Tuesday. Attackers study recipient behaviour, timing delivery for maximum impact. Enterprise email security that queues and rescans early-morning email batches can catch threats that real-time filters miss under volume pressure.
Phishing Volume by Day of Week
Seasonal Phishing Patterns
Beyond day-of-week patterns, phishing follows seasonal trends tied to cultural and business events. Tax season (January-April in the US, January-January in the UK) drives government impersonation phishing — HMRC, IRS, and tax authority phishing spikes 3-4x during filing periods. Holiday shopping seasons (November-December) see surges in delivery service and retail brand impersonation. Back-to-school periods drive education-sector targeting. Year-end financial reporting triggers BEC attacks targeting finance teams under deadline pressure.
Major news events create phishing opportunities. Natural disasters trigger fake charity phishing. Product launches (new iPhone, major software releases) generate fake pre-order and update phishing. Health crises create fake government alert phishing. Geopolitical events create fake news and sanction-related phishing targeting businesses. Attackers monitor the news cycle and launch themed campaigns within hours of breaking events, exploiting heightened emotion and reduced critical thinking.
Phishing Statistics Year-Over-Year
Comparing phishing statistics across years reveals acceleration, not stability. APWG data shows the trajectory: approximately 1 million attacks in 2020, 1.3 million in 2021, 2.35 million in 2022, 3.2 million in 2023, and 3.8 million in 2025. The compounding growth rate of 30-40% annually shows no sign of slowing, particularly as AI tools further reduce the cost and effort of launching campaigns.
BEC losses have followed a similar trajectory: FBI IC3 reported $1.8 billion in 2020, $2.4 billion in 2021, $2.7 billion in 2022, $2.9 billion in 2023, and $2.77 billion in 2024. While the 2024 figure shows a slight decline from 2023, the overall trend remains upward, and the introduction of AI-generated BEC content in 2024-2025 suggests this may be a brief pause before renewed acceleration. The cost per BEC incident has increased even as total reported losses plateaued, indicating fewer but more sophisticated and higher-value attacks.
APWG Phishing Attacks by Year
Source: APWG Phishing Activity Trends Reports
FBI IC3 BEC Losses by Year
Source: FBI Internet Crime Reports 2020-2024
📊 Phishing by the Numbers: Visual Summary
The following visual components summarise the key phishing statistics for 2026. Use these for presentations, security awareness sessions, and executive briefings.
Attack Method Breakdown
Email remains the dominant phishing channel, but the multi-channel threat is growing rapidly. The percentages above represent share of overall phishing activity across channels — note that attacks often span multiple channels (e.g., an email that asks the recipient to call a phone number combines email phishing with vishing).
Phishing Defense Effectiveness
Defense effectiveness estimates are approximate, based on vendor data and industry benchmarks. Phishing-resistant MFA (FIDO2/passkeys) provides the strongest single control because it cryptographically verifies the login domain, defeating even AitM attacks. The most effective defence combines multiple layers — no single control catches all phishing.
Building Your Anti-Phishing Stack
Based on the data in this article, here's the recommended anti-phishing defense stack ordered by impact:
Layer 1: Phishing-Resistant MFA (FIDO2/Passkeys)
Eliminates credential-harvesting effectiveness even when users click. Defeats AitM proxy attacks that bypass standard MFA. Deploy for all users, prioritising executives and finance staff.
Layer 2: Security Awareness Training + Monthly Simulations
Reduces click rates from ~33% baseline to under 5% (KnowBe4). Monthly simulations with just-in-time training achieve 70-80%+ improvement in 6 months. Include vishing and smishing simulations, not just email.
Layer 3: AI-Based Email Security Gateway
Catches AI-generated phishing that rule-based filters miss. Analyses sender behaviour, communication patterns, and content anomalies. Integrates with Microsoft 365 / Google Workspace.
Layer 4: URL Sandboxing & Real-Time Link Analysis
Detonates suspicious links in a sandbox before they reach users. Critical because 86% of malicious spam uses embedded links (VIPRE 2024). Time-of-click analysis catches delayed-activation phishing pages.
Layer 5: Automated Incident Response (SOAR)
Closes the 27.6-minute gap between first click and first report. Automatically resets compromised credentials, revokes sessions, quarantines campaign emails, and notifies affected users within minutes.
Layer 6: Mobile Threat Defense & MDM
Covers the 35% of phishing using SMS/messaging and 83% of phishing sites targeting mobile. Scans URLs on mobile devices, enforces security policies, and detects phishing apps.
Layer 7: Out-of-Band Verification Procedures
Confirms wire transfers, payment changes, and sensitive data requests via a separate communication channel (phone call to known number). Defeats BEC attacks regardless of email quality.
No single layer is sufficient. The data shows that even the best email filtering misses some phishing (82.6% AI-generated content challenges detection), that trained users still click occasionally (2.7% baseline with training), and that mobile and voice channels bypass email controls entirely. The strongest phishing defense is a combination of technical controls that prevent credential exploitation (MFA), human controls that reduce click rates (training), and procedural controls that catch what both miss (verification protocols, automated response).
📋 Key Takeaways for 2026
The phishing landscape in 2026 is defined by three converging trends: AI-powered content generation, multi-channel delivery (email + voice + SMS + QR), and identity-based attacks that bypass traditional security controls. Here's what the data tells us:
1. AI Has Permanently Changed Phishing Economics
82.6% of phishing emails are AI-generated. AI spear phishing matches human-expert click rates at 95% lower cost. The barrier to sophisticated phishing attacks has dropped to near zero, and the trend is accelerating.
2. Email-Only Defense Is No Longer Sufficient
Vishing surged 442%, smishing grew 40%, and QR code phishing increased 400%. 35% of phishing now uses SMS/messaging apps. Organisations defending only the email channel miss a growing share of attacks.
3. Training and Phishing-Resistant MFA Are the Highest-ROI Defenses
Training cuts susceptibility by 85%+ (from ~33% to <5%). Phishing-resistant MFA (FIDO2/passkeys) prevents credential exploitation even when users click. Together, these two controls address 90%+ of phishing risk at a fraction of breach costs.
4. BEC Remains the Costliest Phishing Type
$2.77B in FBI-reported BEC losses (2024), $4.67M average BEC attack cost (IBM), and 54% volume surge in H1 2025. BEC requires no malware — just convincing impersonation, now supercharged by AI-generated content.
5. Speed Is the Attacker's Advantage
21 seconds to click, 28 minutes to report. That 27.6-minute gap is the attacker's window. Closing this gap through automated response, pre-click prevention, and real-time URL analysis is critical for reducing breach impact.
About This Data
This article draws from 76 statistics aggregated from 50+ authoritative sources including IBM Cost of a Data Breach, Verizon DBIR, CrowdStrike Global Threat Report, WEF Global Cybersecurity Outlook, FBI IC3, ISC2 Cybersecurity Workforce Study, Sophos, Gartner, Mandiant M-Trends, and Ponemon Institute reports.
Derived statistics (marked "Nathan House's Analysis") are computed by cross-referencing data from multiple sources — for example, comparing breach costs across industries using IBM data, or validating ransomware trends across Verizon, Sophos, and HIPAA Journal findings.
All statistics include inline source citations with links to primary sources. Data spans 2023-2026, with preference given to the most recent available figures. Last updated: May 2026.
How to Use This Data
Security professionals can use these phishing statistics to build business cases for email security investment, justify security awareness training budgets, and benchmark phishing resilience against industry averages. The derived insights highlight cost differentials and risk gaps that resonate with executive decision-makers.
For CISOs and security leaders: Use the $25 billion annual phishing loss figure, $4.67M average BEC cost, and 27.6-minute click-to-report gap to justify investment in phishing-resistant MFA, email security upgrades, and security awareness programs. The ROI data — training reducing susceptibility by 85%+ at ~$25/employee/year — provides a clear cost-benefit argument.
For security awareness trainers: Use the day-of-week patterns, AI phishing statistics, and multi-channel threat data to design realistic simulation campaigns. Focus training on vishing and smishing, not just email — these are the fastest-growing vectors and the least defended.
For journalists and researchers: All statistics include inline source citations with links to primary sources. Derived statistics are clearly marked as "Nathan House's Analysis" with computation methodology shown. Data spans 2023-2026, with preference given to the most recent available figures.
This page is updated monthly as new reports are published. Bookmark it and return for the latest phishing attack statistics. If you spot an outdated statistic or want to suggest a source, contact us.
About the Author

Nathan House, StationX
Nathan House is a cybersecurity expert with 30 years of hands-on experience. He holds OSCP, CISSP, and CEH certifications, has secured £71 billion in UK mobile banking transactions, and has worked with clients including Microsoft, Cisco, BP, Vodafone, and VISA. Named Cyber Security Educator of the Year 2020 and a UK Top 25 Security Influencer 2025, Nathan is a featured expert on CNN, Fox News, and NBC. He founded StationX, which has trained over 500,000 students in cybersecurity.
Primary Sources
Verizon DBIR 2025
Click rates, breach vectors, phishing in breaches, BEC data, social engineering trends
IBM Cost of a Data Breach 2025
BEC costs, phishing as breach vector, AI impact on detection and costs
FBI Internet Crime Report 2024
BEC losses, phishing complaints, crypto phishing, US-specific data
CrowdStrike Global Threat Report 2025
Vishing surge (442%), deepfake scams, AI-powered threats, voice cloning
APWG Phishing Trends Reports
Quarterly and annual phishing attack volumes, year-over-year trends
Keepnet Labs / VIPRE Security
AI-generated phishing rates (82.6%), BEC AI generation (40%), malspam analysis
HBR / Academic Research 2024
AI spear phishing click rates (54%), cost reduction analysis (95%+)
KnowBe4 / Ponemon / SentinelOne
Training effectiveness, insider phishing costs, global loss estimates, smishing data
❓ Frequently Asked Questions About Phishing
How many phishing emails are sent per day?
Approximately 3.4 billion phishing emails are sent every day worldwide. 82.6% of these are AI-generated (Keepnet/VIPRE 2025). That works out to roughly 39,000 phishing emails per second. The annual total tracked by APWG was 3.8 million distinct phishing attacks in 2025.
What percentage of cyber attacks are phishing?
Phishing appears in 36% of all data breaches (Verizon DBIR 2025) and is the initial attack vector in 16% of breaches (IBM 2025). 80% of all reported security incidents involve phishing in some form (CSO Online). When including all forms of social engineering (email, voice, SMS), 98% of cyberattacks involve social engineering (Sprinto).
How much does phishing cost businesses?
Global phishing losses total $25 billion annually (SentinelOne 2026). The average BEC attack costs $4.67 million (IBM 2025). The FBI reported $2.77 billion in BEC losses alone in 2024 from 21,442 complaints — approximately $129K per complaint. Phishing costs $17,700 per minute globally (CSO Online), or approximately $1.06 million per hour.
What is the phishing email click rate?
The average phishing email click rate is 2.7% (Verizon DBIR 2025). AI-generated spear phishing achieves a much higher 54% click rate (HBR 2024), matching skilled human attackers at 95% lower cost. The median time for a user to click a phishing link is just 21 seconds after receiving the email (Verizon DBIR 2025). With 3.4 billion daily phishing emails and a 2.7% click rate, that's approximately 92 million successful clicks per day.
How effective is phishing awareness training?
Comprehensive security awareness training reduces phishing susceptibility to under 5%, down from an industry baseline of approximately 33% — an 85%+ reduction (KnowBe4 2025). Organisations running monthly phishing simulations with immediate feedback see 70-80%+ improvement within 6 months. Training also improves phishing reporting times, closing the 27.6-minute gap between first click and first report.
What are the latest phishing trends for 2026?
The three biggest phishing trends in 2026 are: (1) AI-generated phishing now accounts for 82.6% of detected phishing emails, with 54% click rates matching human experts; (2) multi-channel attacks — vishing surged 442%, smishing grew 40%, QR phishing increased 400%; (3) BEC remains the costliest variant at $4.67M average per attack, with volume surging 54% in H1 2025. Traditional email-only defenses are increasingly insufficient.
What is business email compromise (BEC)?
BEC is a form of phishing where attackers impersonate executives, vendors, or trusted contacts via email to trick employees into making wire transfers, sharing sensitive data, or changing payment details. FBI IC3 reported $2.77 billion in BEC losses from 21,442 complaints in 2024. The average BEC attack costs $4.67 million (IBM 2025). BEC requires no malware — just convincing impersonation, now supercharged by AI-generated content.
What is the best protection against phishing?
The most effective phishing defense combines multiple layers: (1) phishing-resistant MFA (FIDO2/passkeys) — defeats even AitM attacks; (2) security awareness training with monthly simulations — reduces susceptibility to under 5%; (3) AI-based email gateway filtering; (4) URL sandboxing and real-time link analysis; (5) automated incident response for rapid credential reset after compromise. No single control stops all phishing — layered defense is essential.
