Data Breach Statistics [2026]: Costs, Trends & Latest Data

$4.44 million. That's what the average data breach costs in 2026 — and it takes 241 days to detect and contain one. Whether you need data breach statistics for a board report, security budget justification, or academic research, this is the most comprehensive resource available.
I've aggregated 140+ data breach statistics from over 50 authoritative sources — IBM Cost of a Data Breach, Verizon DBIR, Surfshark, CrowdStrike, Ponemon, and more — and cross-referenced them to produce original analysis you won't find in any single report. You'll find breach costs by industry and country, AI impact on detection and prevention, attack vector analysis, cloud breach trends, and defense strategies across 15 sections below.
Key Data Breach Statistics at a Glance
- $4.44 million — global average breach cost (IBM 2025)
- $10.22 million — US average breach cost, all-time high (IBM 2025)
- 241 days — average breach lifecycle: 181 to detect, 60 to contain (IBM 2025)
- 5,176 confirmed breaches with data exposure in 2024 (Verizon DBIR)
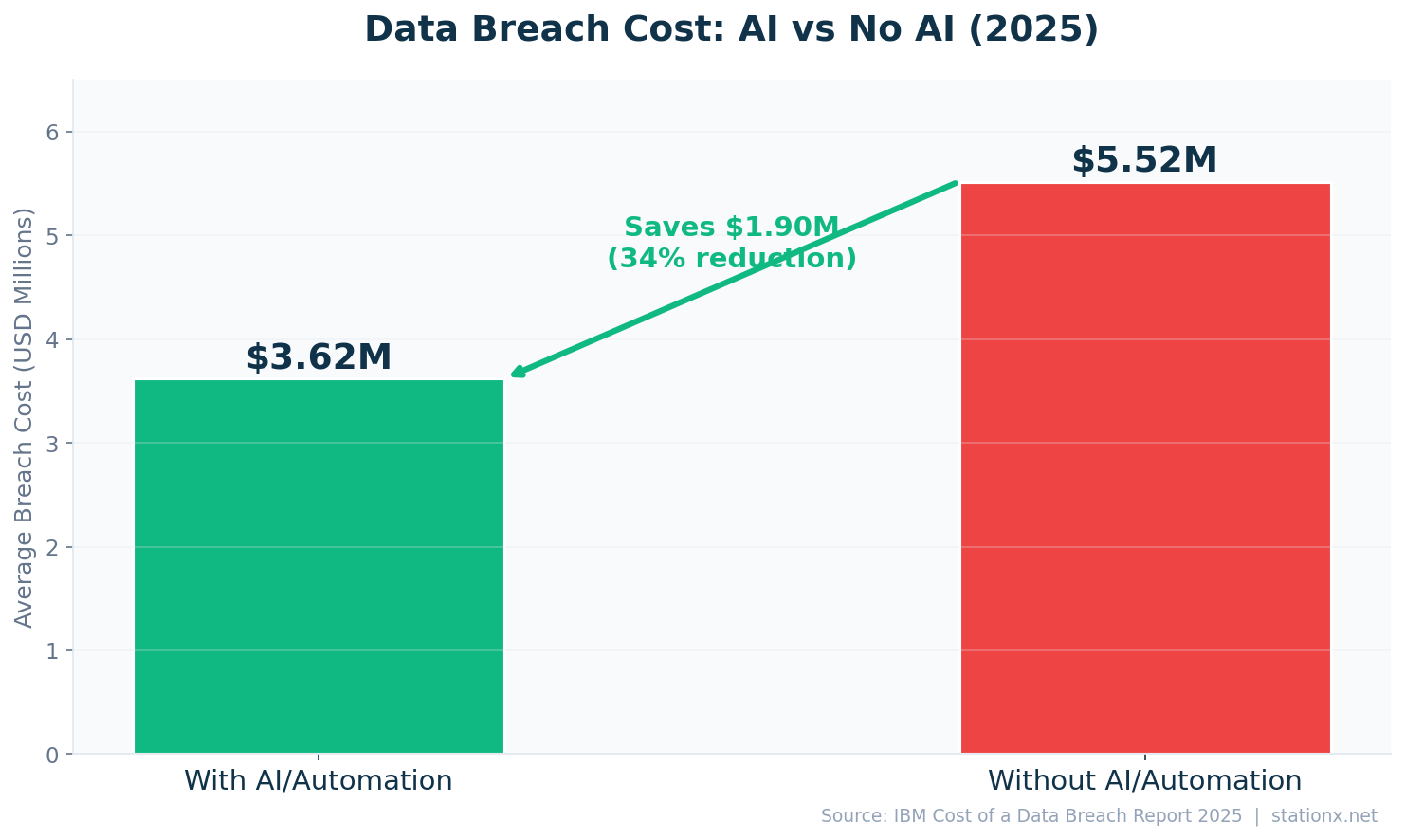
- $1.9 million saved per breach with AI/automation ($3.62M vs $5.52M without)
- $11.2 million — healthcare breach cost, highest industry for 15 years (IBM 2025)
- 82% of breaches involve the human element (Verizon DBIR 2025)
- 70% of breaches come from external actors (IBM 2025)
Last updated: May 2026
📊 Key Data Breach Numbers (2026)
The global average cost of a data breach reached $4.44 million in 2025 (IBM). In the US, that figure climbed to an all-time high of $10.22 million — 2.3x the global average. The average breach takes 241 days from initial compromise to full containment: 181 days to identify and 60 days to contain. Every additional day of undetected access increases the cost.
Verizon's 2024 analysis confirmed 5,176 data breaches with verified data exposure. 82% involved the human element (Verizon DBIR 2025). 70% of breaches originated from external actors (IBM 2025), while 74% had a financial motive (Verizon DBIR 2025). Surfshark tracked 5.2 billion accounts breached worldwide in 2025. 70% of breaches caused significant operational disruption (IBM 2024).
| Finding | Value | Source |
|---|---|---|
| Global average breach cost | $4.44M | IBM Cost of a Data Breach Report 2025 |
| US average breach cost (highest) | $10.22M | IBM Cost of a Data Breach Report 2025 |
| Average breach lifecycle | 241 days | IBM Cost of a Data Breach Report 2025 |
| Average time to identify a breach | 181 days | IBM Cost of a Data Breach Report 2025 |
| Average time to contain a breach | 60 days | IBM Cost of a Data Breach Report 2025 |
| Average cost per compromised record | $160 | IBM Cost of a Data Breach Report 2025 |
| Confirmed breaches (2024) | 5,176 | Verizon DBIR 2025 |
| Breaches involving the human element | 68% | Verizon DBIR 2025 |
| Breaches from external actors | 70% | Verizon DBIR 2025 |
| Breaches with financial motive | 95% | Verizon DBIR 2025 |
| Accounts breached worldwide (2025) | 425.7 million | Surfshark |
| Breaches causing significant disruption | 70% | IBM Cost of a Data Breach Report 2024 |
$1K Lost Per Hour of Breach Dwell Time
At $4.44M average breach cost over a 241-day lifecycle, every hour of undetected access costs approximately $1K. Every day: $18K. This is why AI-powered detection — cutting dwell time from 241 days to 51 days — saves $1.9M per breach. Speed of detection is directly proportional to cost reduction. (IBM Cost of a Data Breach 2025)
The Scale of the Problem
5,176 confirmed breaches in a single year means roughly 14 breaches per day — each costing an average of $4.44 million. At $160 per compromised record, a breach involving 50,000 records costs approximately $8 million. Intellectual property records cost even more: $178 per record (IBM 2025).
The financial motive dominates: 74% of breaches are financially motivated (Verizon DBIR 2025). Espionage accounts for another significant segment (Verizon 2025). Third-party breaches doubled year-over-year to 30% of incidents (IBM 2025), reflecting the expanding attack surface through supply chain dependencies.
📈 Data Breach Trends
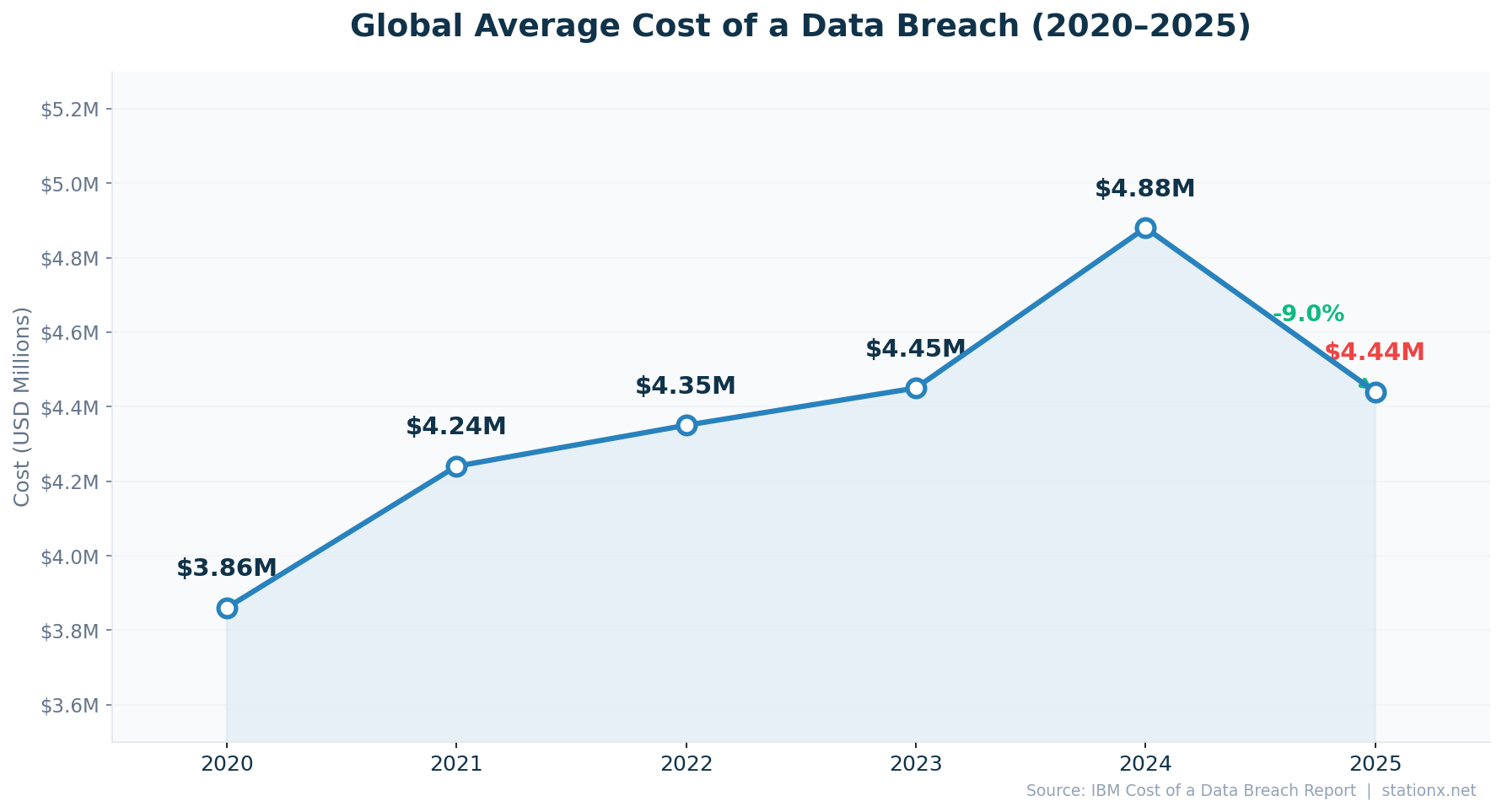
The global average breach cost fell 9% from $4.88M (2024) to $4.44M (2025) — the first decline in four years. But the headline masks a more complex picture: US breach costs hit an all-time high of $10.22M, AI-driven attacks cost $4.49M on average, and third-party breaches doubled year-over-year. The cost drop reflects geographic distribution shifts, not improving security outcomes.
Supply chain attacks grew significantly, with Verizon noting a 68% year-over-year increase in supply chain breaches. 49% of organisations plan to increase security spending (IBM 2025), recognising that current investment levels are insufficient. The trend toward AI in both attack and defence is accelerating, creating a growing gap between organisations that adopt AI security tools and those that don't.
| Finding | Value | Source |
|---|---|---|
| Average breach cost (2024) | $4.88M | IBM Cost of a Data Breach Report 2024 |
| Average breach cost (2025) | $4.44M | IBM Cost of a Data Breach Report 2025 |
| Total incidents reviewed (2024) | 10,626 | Verizon DBIR 2025 |
| Confirmed breaches with data exposure | 5,176 | Verizon DBIR 2025 |
| Third-party breaches (doubled YoY) | 30% | IBM Cost of a Data Breach Report 2025 |
| Supply chain breach increase YoY | 68% | Verizon DBIR 2024 |
| Orgs increasing security spending | 49% | IBM Cost of a Data Breach Report 2025 |
Breach Costs Dropped 9% — But Don't Celebrate Yet
Data breach costs fell -9.0% year-over-year ($4.88M in 2024 to $4.44M in 2025). The drop looks positive, but it's misleading in isolation. The US average hit an all-time high of $10.22M, AI-driven attacks now cost $4.49M, and third-party breaches doubled. The global average fell because more breaches occurred in lower-cost regions, not because breaches became cheaper. (IBM Cost of a Data Breach Report 2024, IBM Cost of a Data Breach Report 2025)
Costliest Breach Types
- Healthcare — $11.2M (15 years running, IBM)
- Multi-environment — $5.05M (IBM 2025)
- Ransomware — $5.08M (IBM 2025)
Biggest Cost Reducers
- AI/Automation — saves $1.9M (IBM 2025)
- Incident response plan — saves $2.66M (IBM)
- Zero-trust — saves $1.76M (IBM 2025)
The AI Divide
The most significant trend in breach data isn't cost or volume — it's the growing divide between organisations with and without AI security tools. Those with extensive AI/automation pay $3.62M per breach; those without pay $5.52M. That $1.9M gap is widening annually. Organisations that haven't adopted AI-driven security are falling behind not just in detection speed but in overall resilience.
🏥 Data Breach Costs by Industry
Healthcare leads all industries at $11.2 million per breach (IBM 2025), a position it has held for 15 consecutive years. The healthcare premium is driven by HIPAA regulatory costs, the high black-market value of medical records (10-40x credit card data), and the life-critical nature of healthcare systems that makes downtime unacceptable.
Financial services comes second at $6.08 million (IBM 2025), followed by critical infrastructure at $4.82 million. Education breaches average $3.80 million. Supply chain breaches cost $4.91 million on average, reflecting the cascading damage when a single vendor compromise affects multiple downstream organisations. Healthcare costs rose 42% between 2020 and 2024 (IBM).
| Finding | Value | Source |
|---|---|---|
| Healthcare (highest — 15 years running) | $11.2M | IBM Cost of a Data Breach Report 2025 |
| Financial services | $6.08M | IBM Cost of a Data Breach Report 2025 |
| Critical infrastructure | $4.82M | IBM Cost of a Data Breach Report 2025 |
| Education | $3.80M | IBM Cost of a Data Breach Report 2025 |
| Global average (all industries) | $4.44M | IBM Cost of a Data Breach Report 2025 |
| Healthcare cost increase 2020-2024 | 42% | IBM / Fortinet |
| Supply chain breach cost | $4.91M | IBM Cost of a Data Breach Report 2025 |
Healthcare Pays 2.5x the Global Average
Healthcare breach costs are 2.5x the global average. At $11.2M per breach, healthcare has led all industries for 15 consecutive years. The premium stems from highly regulated data (HIPAA), life-critical system disruption, and the extraordinarily high black-market value of medical records — worth 10-40x more than credit card numbers. (IBM Cost of a Data Breach Report 2025)
Healthcare Costs 1.8x More Than Financial Services
Healthcare breaches cost 1.8x more than financial services breaches. Healthcare ($11.2M) overtakes financial services ($6.08M) by a factor of 1.8x. Financial services has invested heavily in cybersecurity infrastructure; healthcare lags behind due to budget constraints, legacy systems, and a workforce focused on patient care over IT security. (IBM Cost of a Data Breach Report 2025)
Why Healthcare Remains the Costliest
Healthcare organisations face a unique combination of pressures: strict regulatory requirements (HIPAA mandates breach notifications, credit monitoring, and potential fines), the irreplaceable nature of patient data (you can get a new credit card, but not a new medical history), and the critical operational impact when systems go down (delayed treatments, diverted ambulances, cancelled surgeries). 92% of healthcare organisations experienced at least one cyberattack in 2024 (Ponemon), and 69% reported attacks disrupting patient care (Ponemon 2024).
What Would a Breach Cost Your Organisation?
Adjust the inputs below to estimate your breach cost based on IBM Cost of a Data Breach 2025 data.
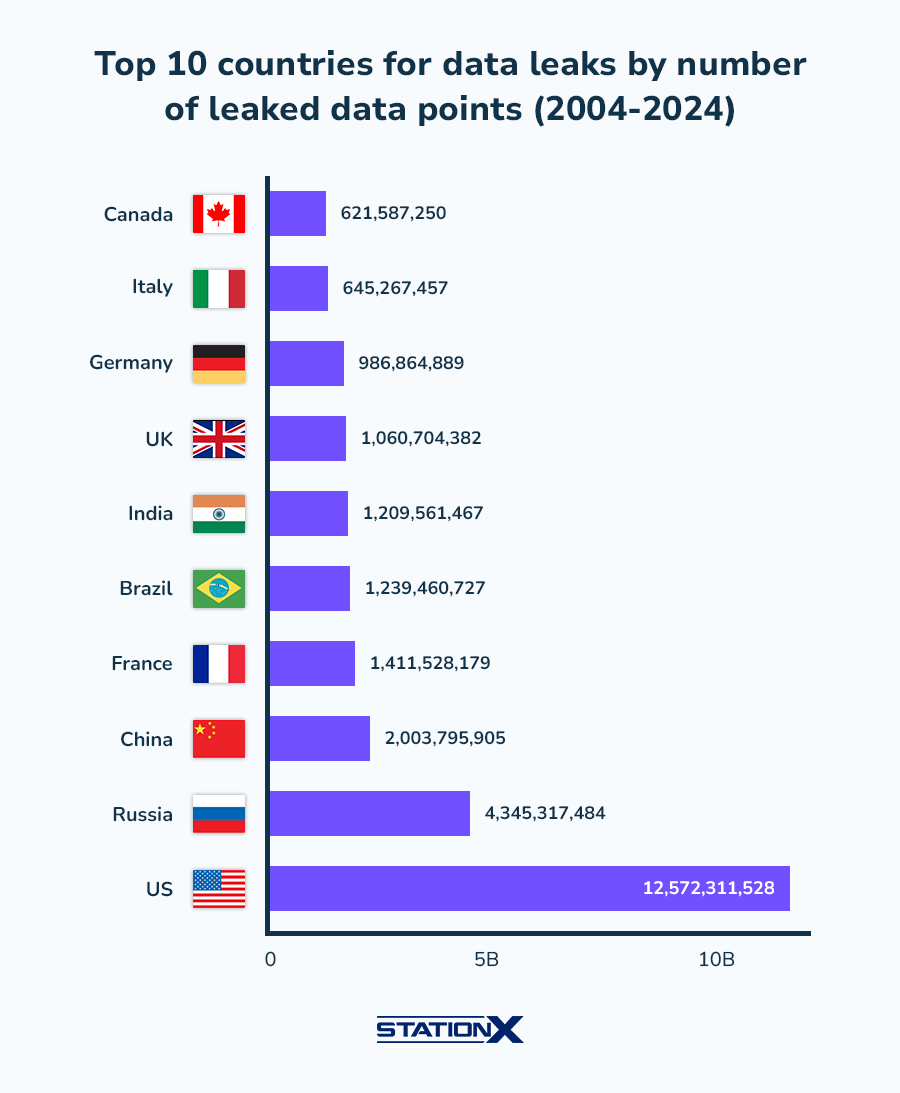
🌍 Data Breach Costs by Country
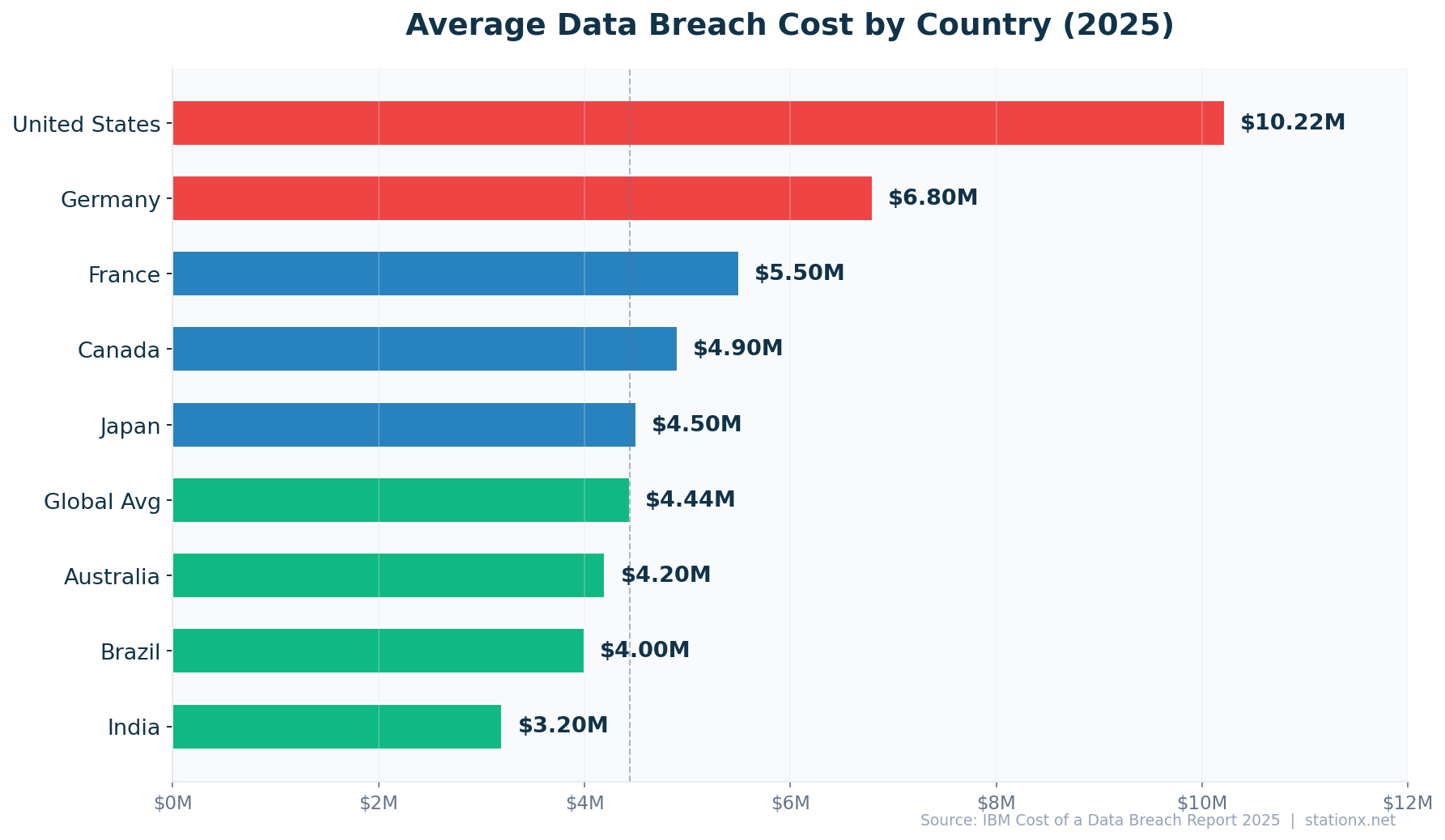
The United States leads the world in breach costs at $10.22 million — an all-time high and 2.3x the global average of $4.44M. Germany follows at $6.8M, France at $5.5M, and Canada at $4.9M. At the lower end, India averages $3.2M — still devastating for organisations in that market, but a 3.2x cost difference from the US.
The US premium reflects several factors: stringent state-level breach notification laws (all 50 states have them), higher litigation exposure and class action risk, higher labour costs for incident response teams, and the concentration of high-value targets in US-based financial services and healthcare sectors. GDPR-regulated European countries (Germany, France) face significant but lower costs due to regulatory fines and mandatory reporting.
| Finding | Value | Source |
|---|---|---|
| United States (highest) | $10.22M | IBM Cost of a Data Breach Report 2025 |
| Germany | $4.03M | IBM Cost of a Data Breach Report 2025 |
| France | $3.73M | IBM Cost of a Data Breach Report 2025 |
| Canada | $4.84M | IBM Cost of a Data Breach Report 2025 |
| Japan | $3.65M | IBM Cost of a Data Breach Report 2025 |
| Australia | $2.55M | IBM Cost of a Data Breach Report 2025 |
| Brazil | $1.22M | IBM Cost of a Data Breach Report 2025 |
| India | $2.51M | IBM Cost of a Data Breach Report 2025 |
| Global average | $4.44M | IBM Cost of a Data Breach Report 2025 |
US Breaches Cost 2.3x the Global Average
US breach costs are 2.3x the global average. At $10.22M per breach, US organisations face more than double the global average of $4.44M. This premium reflects higher regulatory costs (HIPAA, state breach notification laws), larger litigation exposure, higher labour costs for incident response, and the concentration of high-value targets in financial services and healthcare. (IBM Cost of a Data Breach Report 2025)
9 Countries Ranked by Breach Cost
Breach costs range $10.22M (US) to $1.22M (India). The US ($10.22M) leads by a wide margin — 50% more than second-place Germany ($6.8M). The bottom of the ranking, India ($3.2M), still represents a devastating cost for organisations in that market. Geography alone determines a 3.2x cost difference. (IBM Cost of a Data Breach Report 2025)
⏱️ Breach Detection & Response Times
The average organisation takes 181 days to identify a breach and another 60 days to contain it — a total lifecycle of 241 days (IBM 2025). That's nearly 8 months of undetected access. Breaches contained within 200 days cost $3.87M on average; those exceeding 200 days cost $5.01M — a $1.14M penalty for slow detection.
AI/automation dramatically accelerates detection. Organisations with extensive AI detect breaches in 51 days versus the 241-day average (IBM 2025). XDR technology reduces breach lifecycle by 55 days. The median breach discovery time is 24 days (Verizon DBIR 2025), though this figure represents the fastest detectors, not the average.
| Finding | Value | Source |
|---|---|---|
| Average breach lifecycle (identify + contain) | 241 days | IBM Cost of a Data Breach Report 2025 |
| Average days to identify | 181 days | IBM Cost of a Data Breach Report 2025 |
| Average days to contain | 60 days | IBM Cost of a Data Breach Report 2025 |
| Detection time with AI/automation | 51 days | IBM Cost of a Data Breach Report 2025 |
| Median breach discovery time | 51 days | Verizon DBIR 2025 |
| Cost for breaches >200 days | $5.01M | IBM Cost of a Data Breach Report 2025 |
| Cost for breaches <200 days | $3.87M | IBM Cost of a Data Breach Report 2025 |
| Lifecycle reduction with XDR | 55 days | IBM / UpGuard |
AI Detects Breaches 190 Days Faster
AI-equipped organizations detect breaches 190 days faster (51 vs 241 days). With AI/automation, organisations detect breaches in 51 days versus the 241-day average lifecycle without. That's 190 fewer days of undetected attacker access — 190 fewer days of data exfiltration, lateral movement, and damage accumulation. Every additional day of dwell time increases breach cost. (IBM Cost of a Data Breach Report 2025)
Breach Timeline Simulator
What happens after a data breach? Drag the slider to see the typical timeline from compromise to containment.
The 200-Day Cost Threshold
IBM's data reveals a clear cost threshold at 200 days. Breaches contained before 200 days cost $3.87M on average; after 200 days, $5.01M. The $1.14M penalty for crossing this threshold reflects the compounding damage of extended dwell time: more data exfiltrated, more systems compromised, more regulatory notifications required, and more customer trust lost.
The organisations that detect fastest deploy AI-powered security analytics, maintain 24/7 SOC operations, and use XDR platforms that correlate alerts across endpoints, networks, and cloud workloads. The investment case is clear: even modest improvements in detection speed (reducing lifecycle from 241 to 200 days) save over $1 million per breach.
🤖 AI Impact on Data Breaches
AI is reshaping both sides of the breach equation. On defence: organisations with extensive AI/automation pay $3.62M per breach versus $5.52M without — a 34% cost reduction and $1.9M in savings (IBM 2025). AI-equipped organisations detect breaches 190 days faster (51 days vs 241 days). Annual savings from AI-driven security total $2.22M per organisation.
On offence: 16% of breaches now involve attacker-used AI (IBM 2025). AI-driven attacks cost $4.49M on average. 37% of breaches use AI-generated phishing as the attack method (IBM 2025). Shadow AI is emerging as a new risk vector: 20% of organisations experienced breaches linked to shadow AI use, costing $4.63M on average — $670K above the global mean.
| Finding | Value | Source |
|---|---|---|
| Breach cost with AI/automation | $3.62M | IBM Cost of a Data Breach Report 2025 |
| Breach cost without AI/automation | $5.52M | IBM Cost of a Data Breach Report 2025 |
| Cost savings from security AI | $1.9M | IBM Cost of a Data Breach Report 2025 |
| Breach cost reduction percentage | 34% | IBM Cost of a Data Breach Report 2025 |
| Detection time with AI | 51 days | IBM Cost of a Data Breach Report 2025 |
| Breaches involving attacker AI | 16% | IBM Cost of a Data Breach Report 2025 |
| Cost of AI-driven attacks | $4.49M | IBM Cost of a Data Breach Report 2025 |
| Shadow AI breach cost | $4.63M | IBM Cost of a Data Breach Report 2025 |
| Orgs with shadow AI breaches | 20% | IBM Cost of a Data Breach Report 2025 |
AI Saves $1.9M Per Breach
Organizations with extensive AI/automation save $1.9M per breach ($3.62M vs $5.52M without). Organisations with extensive AI and automation pay $3.62M per breach versus $5.52M without — a $1.9M gap. AI accelerates detection by 190 days, automates containment, and reduces the manual investigation burden. The ROI case for AI-driven security is now unambiguous. (IBM Cost of a Data Breach Report 2025)
Shadow AI: The Emerging Blind Spot
Shadow AI — employees using unapproved AI tools with corporate data — has emerged as a significant breach vector. 20% of organisations report shadow AI-linked breaches (IBM 2025), costing $4.63M on average. 65% of these breaches compromised customer PII. The root cause: employees paste proprietary data, customer information, and code into public AI services without understanding the data exposure implications.
The defensive case for AI is clear. But the same technology that powers defence — AI-generated phishing (37% of breaches), deepfake impersonation (35% of breaches), and automated reconnaissance — also powers increasingly sophisticated attacks. 49% of organisations plan to increase security spending (IBM 2025), with AI-driven security tools as the primary investment target.
👤 Human Error & Insider Breaches
82% of data breaches involve the human element (Verizon DBIR 2025) — whether through phishing, stolen credentials, misconfiguration, or social engineering. Stanford University research places the figure even higher at 88% when accounting for indirect human error. People remain the weakest link in cybersecurity, and no technology stack eliminates human risk entirely.
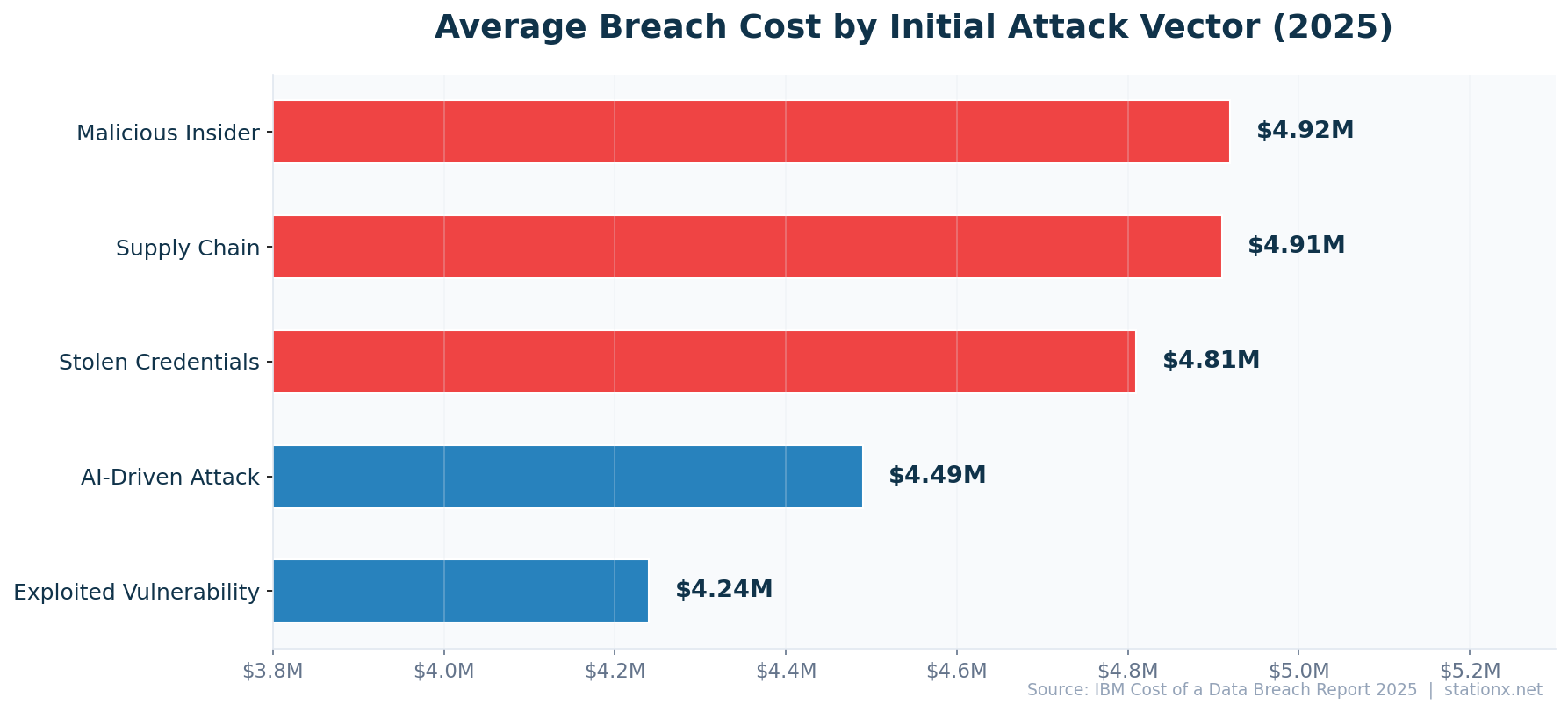
Malicious insider breaches cost $4.92M on average (IBM 2025) — higher than the global average because insiders have legitimate access, making detection harder and dwell time longer. Negligent employees account for the majority of insider incidents (Ponemon 2025). Third-party breaches doubled year-over-year (IBM 2025), adding supply chain partners as an extended insider threat surface.
| Finding | Value | Source |
|---|---|---|
| Breaches involving human element | 68% | Verizon DBIR 2025 |
| Breaches caused by human error | 88% | Stanford University |
| Malicious insider breach cost | $4.92M | IBM Cost of a Data Breach Report 2025 |
| Third-party breach involvement | 30% | IBM Cost of a Data Breach Report 2025 |
| Insider incidents from negligence | 55% | Ponemon Institute / DTEX 2025 Cost of Insider Risks Report |
| Breaches attributed to insiders | 30% | Verizon DBIR 2025 |
| Breach cost with skills shortage | $5.22M | IBM Cost of a Data Breach Report 2025 |
Skills Shortage Adds 17.6% to Breach Costs
Skills shortage adds 17.6% to breach costs ($5.22M vs $4.44M average). Organisations facing high cybersecurity skill shortages pay $5.22M per breach — 17.6% above the global average. The skills gap isn't just a hiring problem; it's a direct financial risk multiplier. Under-staffed security teams detect breaches later, respond slower, and contain less effectively. (IBM Cost of a Data Breach Report 2025)
The Skills Shortage Multiplier
The cybersecurity skills gap isn't just a recruitment challenge — it's a direct cost multiplier. Organisations with high skill shortages pay $5.22M per breach versus the $4.44M global average, a 17.6% premium. Under-staffed security teams take longer to detect breaches, respond less effectively during incidents, and are more likely to miss critical alerts. AI-driven automation partially offsets this gap by handling routine triage and accelerating detection, but human expertise remains essential for complex incident response and threat hunting.
🔍 Breach Vectors & Root Causes
Stolen or compromised credentials are the most common breach vector, appearing in 29% of breaches (Verizon DBIR 2025) at a cost of $4.81M per incident. Ransomware/extortion breaches cost $5.08M on average (IBM 2025) and appear in a growing share of all breaches. Exploited vulnerabilities cost $4.24M per breach, and organisations take a median of 55 days to remediate known vulnerabilities (Verizon DBIR 2025).
Breaches spanning multiple environments cost $5.05M on average (IBM 2025) — reflecting the complexity of hybrid IT architectures where data flows between cloud, on-premises, and SaaS systems. Supply chain breaches cost $4.91M, driven by the cascading effect when a single compromised vendor grants access to dozens of downstream organisations.
| Finding | Value | Source |
|---|---|---|
| Stolen credentials breach cost | $4.81M | IBM Cost of a Data Breach Report 2025 |
| Breaches using stolen credentials | 53% | Verizon DBIR 2025 |
| Ransomware/extortion breach cost | $5.08M | IBM Cost of a Data Breach Report 2025 |
| Ransomware in breaches | 44% | Verizon DBIR 2025 |
| Exploited vulnerability cost | $4.24M | IBM Cost of a Data Breach Report 2025 |
| Vulnerability exploitation share | 20% | Verizon DBIR 2025 |
| Supply chain breach cost | $4.91M | IBM Cost of a Data Breach Report 2025 |
| Multi-environment breach cost | $5.05M | IBM Cost of a Data Breach Report 2025 |
Why Credentials Dominate
Stolen credentials dominate breach vectors because they bypass perimeter defenses entirely. A valid username and password grants legitimate access — no exploit needed, no malware to detect, no anomaly to trigger. Verizon reports that BYOD devices mixing work and personal credentials create massive exposure, and enterprise-licensed machines regularly appear in credential breach logs. The solution: phishing-resistant MFA (FIDO2/passkeys), credential monitoring, and zero-trust architectures that verify every access request regardless of source.
☁️ Cloud Data Breaches
Hybrid cloud environments have the lowest breach costs at $3.8M — lower than on-premises ($4.01M) and significantly lower than public cloud-only (247-day lifecycle, IBM 2025). The hybrid advantage comes from better visibility across environments and the ability to keep the most sensitive data on-premises while using cloud for less sensitive workloads.
Cloud intrusions increased 26% year-over-year (CrowdStrike 2024), with cloud credential incidents accounting for a growing share. Cloud misconfiguration remains a persistent breach cause (Verizon). Breaches spanning multiple environments — cloud, on-premises, and SaaS — cost $5.05M on average (IBM 2025), the costliest deployment scenario.
| Finding | Value | Source |
|---|---|---|
| Hybrid cloud breach cost (lowest) | $3.8M | IBM / UpGuard |
| On-premises breach cost | $4.01M | IBM Cost of a Data Breach Report 2025 |
| Public cloud breach lifecycle | 247 days | IBM Cost of a Data Breach Report 2025 |
| Breaches from cloud misconfiguration | 15% | Verizon DBIR 2023 |
| Cloud intrusion increase (2024) | 26% | CrowdStrike 2025 Global Threat Report |
| Cloud credential incidents | 35% | CrowdStrike 2025 Global Threat Report |
| Multi-environment breach cost | $5.05M | IBM Cost of a Data Breach Report 2025 |
Cloud Security Best Practices
The cloud breach data points to clear best practices: adopt hybrid architectures (lowest cost), implement cloud security posture management (CSPM) to catch misconfigurations before attackers do, enforce MFA on all cloud accounts, and treat cloud credential management with the same rigour as on-premises access control. The 26% increase in cloud intrusions (CrowdStrike 2024) suggests that many organisations are migrating to cloud faster than they're securing it.
📰 Recent Data Breaches
The past 12 months have seen some of the most consequential data breaches in history, affecting billions of records across healthcare, telecommunications, financial services, and government. These incidents underscore the statistics above — the breach lifecycle, detection delays, and human error patterns play out repeatedly in real-world incidents.
Change Healthcare (2024)
UnitedHealth subsidiary. Ransomware attack disrupted prescription processing for weeks across the US, affecting ~100 million patient records. Estimated cost: over $2.45 billion. The largest healthcare breach by impact in US history.
National Public Data (2024)
Background check company. 2.7 billion records exposed including Social Security numbers, names, and addresses. One of the largest personal data exposures ever, affecting most US adults.
AT&T (2024)
Telecommunications giant. Two separate breaches: 73 million customer records from 2019 data exposed, and call/text metadata for "nearly all" wireless customers (110 million+) stolen from Snowflake cloud platform.
Snowflake Customer Breaches (2024)
Cloud data platform. Attackers used stolen credentials to access 165+ Snowflake customer environments including Ticketmaster (560M records), Santander, and AT&T. Root cause: single-factor authentication on cloud accounts.
MOVEit Transfer (2023-2024)
File transfer vulnerability (CVE-2023-34362). Cl0p ransomware gang exploited zero-day to breach 2,700+ organisations and expose data of 93 million individuals. A single supply chain vulnerability cascading across thousands of victims.
The Common Thread
Every major recent breach maps to the statistics in this article: stolen credentials (Snowflake), ransomware ($5.08M avg cost), supply chain vulnerabilities (MOVEit), healthcare targeting ($11.2M avg), and detection delays (Change Healthcare operated for weeks before full scope was understood). The data predicts the patterns; the incidents confirm them.
💥 Biggest Data Breaches in History
The scale of data breaches has grown exponentially. What was considered a catastrophic breach a decade ago — tens of millions of records — is now routine. The largest breaches in history involve billions of records and have reshaped regulations, corporate security standards, and consumer expectations worldwide.
| Organisation | Year | Records | Impact |
|---|---|---|---|
| Yahoo | 2013-2014 | 3 billion | All Yahoo user accounts. Reduced acquisition price by $350M. |
| National Public Data | 2024 | 2.7 billion | SSNs, names, addresses of most US adults. |
| First American | 2019 | 885 million | Insurance/financial documents, SSNs. Web application vulnerability. |
| Aadhaar (India) | 2018 | 815 million | Biometric and demographic data of Indian citizens. |
| 2021 | 700 million | User profile data scraped and sold on dark web. | |
| Marriott | 2018 | 500 million | Guest data, passport numbers. 4-year dwell time before detection. |
| Equifax | 2017 | 147 million | SSNs, credit data. $700M+ settlement. Unpatched Apache Struts. |
Lessons From the Biggest Breaches
The common themes across the largest breaches are consistent: unpatched vulnerabilities (Equifax, MOVEit), stolen credentials without MFA (Snowflake), extended dwell times (Marriott: 4 years), and supply chain dependencies (MOVEit cascading to 2,700+ victims). Every one of these breaches was preventable with controls that were known and available at the time. The gap is not in security knowledge — it's in consistent implementation.
🛡️ Data Breach Defense & Prevention
The data reveals clear cost-saving strategies. Organisations with incident response plans save $2.66M per breach (IBM 2025). Zero-trust architectures reduce breach costs by $1.76M. DevSecOps approaches bring breach costs to $3.89M — below the global average. AI/automation saves $1.9M per breach. Involving law enforcement saves an additional $990K. Organisations that resolve breaches in under 200 days save $1.14M.
| Finding | Value | Source |
|---|---|---|
| Zero-trust cost reduction | $1.76M | IBM / UpGuard |
| Incident response plan savings | $2.66M | IBM Cost of a Data Breach Report 2025 |
| DevSecOps breach cost | $3.89M | IBM Cost of a Data Breach Report 2025 |
| Law enforcement involvement savings | $990K | IBM Cost of a Data Breach Report 2025 |
| AI/automation cost savings | $1.9M | IBM Cost of a Data Breach Report 2025 |
| Fast resolution breach cost | $3.87M | IBM Cost of a Data Breach Report 2025 |
| Orgs increasing security spending | 49% | IBM Cost of a Data Breach Report 2025 |
Critical Infrastructure: 1.08x the Global Average
Critical infrastructure breaches cost 1.1x the global average. Critical infrastructure breaches average $4.82M — 8.6% above the global mean. The premium is lower than healthcare or financial services, but the societal impact is disproportionately higher: disrupted water systems, power grids, and transportation infrastructure affect millions. (IBM Cost of a Data Breach Report 2025)
The Highest-ROI Security Investments
1. Incident Response Plan & Testing — saves $2.66M
The single largest cost reducer. Create, document, and regularly test your IR plan. Include tabletop exercises quarterly. Assign roles, establish communication protocols, and pre-engage forensics and legal teams.
2. AI-Driven Security Operations — saves $1.9M
Deploy AI/automation for threat detection, alert triage, and automated response. Cuts detection time from 241 days to 51 days. The ROI is now unambiguous: $1.9M saved per breach at the cost of tooling investment.
3. Zero-Trust Architecture — saves $1.76M
Verify every access request regardless of source. Implement least-privilege access, microsegmentation, and continuous authentication. Reduces lateral movement when initial compromise occurs.
4. Law Enforcement Engagement — saves $990K
Involve law enforcement early. FBI and equivalent agencies provide threat intelligence, support recovery, and can help negotiate with ransomware operators. IBM data shows a $990K cost reduction from engagement.
5. DevSecOps Integration — reduces to $3.89M
Embed security into the development pipeline. Catch vulnerabilities before deployment. DevSecOps organisations have below-average breach costs because fewer vulnerabilities reach production.
The Combined Defense ROI
Organisations implementing IR plans + AI automation + zero-trust see cumulative savings of $6.32M per breach — more than the global average breach cost itself. The investment case is not incremental; it's transformative. Effective defence doesn't just reduce breach costs — it can make them cheaper than the cost of not investing.
⚖️ Data Breach Regulations & Fines
Compliance failure adds $1.22M to the average breach cost (IBM 2025). This premium reflects regulatory fines, mandatory notifications, credit monitoring provisions, and increased legal exposure. 70% of breaches cause significant operational disruption (IBM 2024), extending the financial impact beyond direct incident costs.
The regulatory landscape continues to expand globally. GDPR fines have reached hundreds of millions for major breaches (Meta: €1.2B for data transfer violations). US state-level privacy laws are proliferating, with California (CCPA/CPRA), Virginia, Colorado, and others imposing breach notification requirements and potential penalties. Sector-specific regulations — HIPAA (healthcare), PCI DSS (payments), SOX (financial reporting) — add industry-specific compliance costs.
| Finding | Value | Source |
|---|---|---|
| Additional cost from compliance failure | $1.22M | IBM Cost of a Data Breach Report 2025 |
| Savings from involving law enforcement | $990K | IBM Cost of a Data Breach Report 2025 |
| Breaches causing operational disruption | 70% | IBM Cost of a Data Breach Report 2024 |
Key Data Breach Regulations
GDPR (EU/EEA)
72-hour breach notification, fines up to 4% of annual global revenue or €20M. Largest fine: €1.2 billion (Meta, 2023).
HIPAA (US Healthcare)
Mandatory breach notification to HHS within 60 days for breaches affecting 500+ individuals. Penalties from $100 to $50,000 per violation, up to $1.5M per year per violation category.
CCPA/CPRA (California)
Statutory damages of $100-$750 per consumer per incident for data breaches involving negligent security. Class action exposure for large breaches.
SEC Cyber Disclosure Rules (US)
Material cyber incidents must be disclosed within 4 business days. Annual reporting on cybersecurity risk management. Effective December 2023.
📅 Data Breach Statistics by Year
Data breach costs have trended upward over the past decade, with a brief dip in 2025. The trajectory reflects increasing data volumes, expanding regulatory requirements, and growing attacker sophistication. Here's how the global average breach cost has changed:
| Year | Avg Cost | YoY Change | Key Development |
|---|---|---|---|
| 2025 | $4.44M | -9.0% | AI security adoption accelerates; US hits $10.22M record |
| 2024 | $4.88M | +10.0% | All-time high; AI-driven attacks emerge |
| 2023 | $4.45M | +2.3% | MOVEit supply chain attack; healthcare costs surge |
| 2022 | $4.35M | +2.6% | Cloud breaches rise; ransomware intensifies |
| 2021 | $4.24M | +10.0% | Remote work impact; Colonial Pipeline |
| 2020 | $3.86M | -1.5% | COVID-19 pandemic; SolarWinds breach |
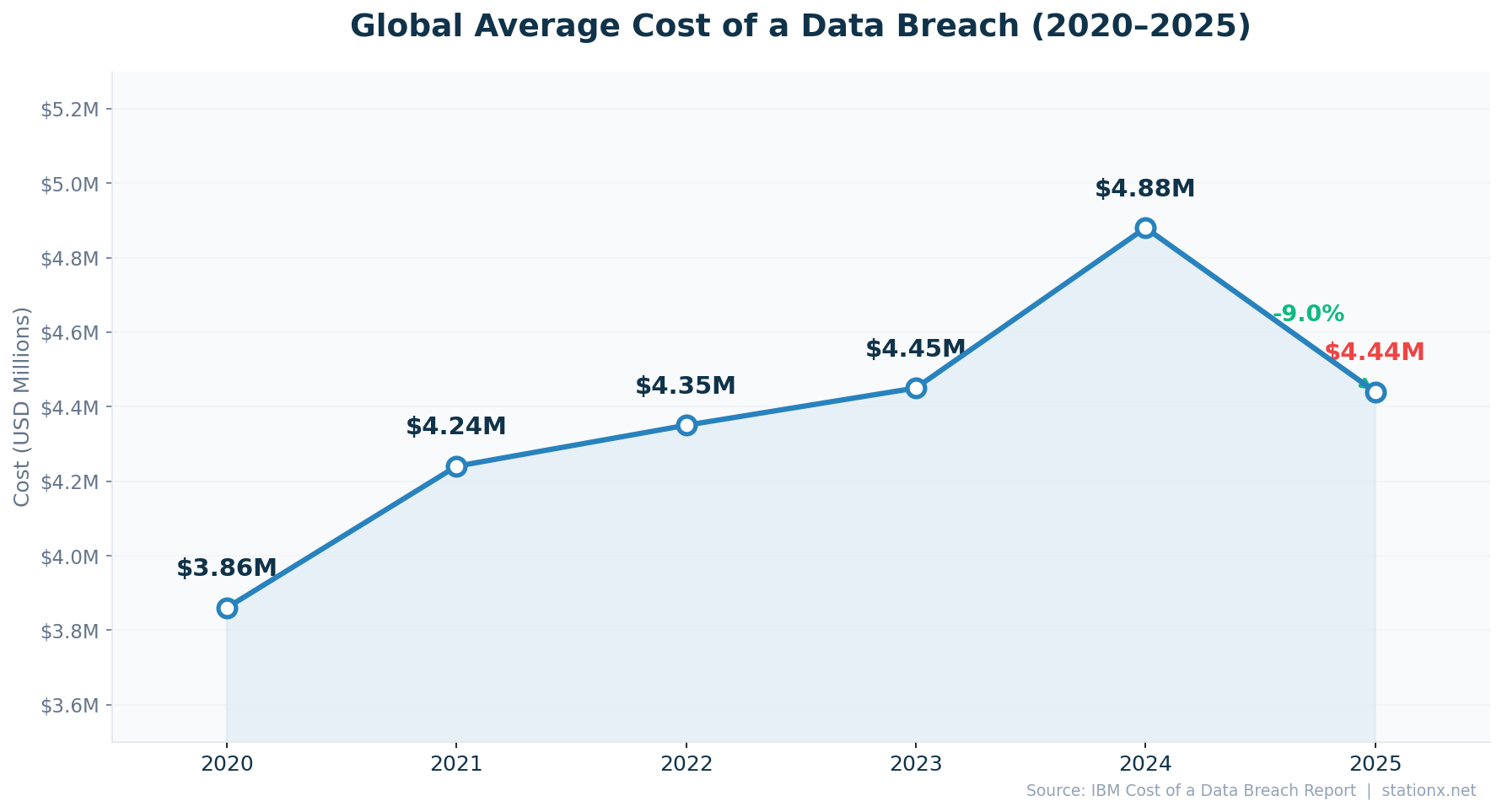
The 2025 dip is noteworthy but should not be interpreted as improving security. The US average hitting $10.22M (all-time high), third-party breaches doubling, and AI-driven attack costs averaging $4.49M all suggest the threat landscape is intensifying. The global average decline reflects geographic distribution changes: more breaches in lower-cost regions like India ($3.2M) and Brazil ($4.0M), bringing the weighted average down while individual country costs rise.
📋 Key Takeaways for 2026
The data breach landscape in 2026 is defined by three forces: the AI security divide, supply chain risk multiplication, and the speed-vs-cost relationship. Here's what the data tells us:
1. AI Is the Single Biggest Cost Differentiator
$1.9M savings per breach. 190 days faster detection. 34% cost reduction. Organisations with AI/automation pay $3.62M; without pay $5.52M. The gap is widening annually. AI security investment is no longer optional — it's the primary determinant of breach cost.
2. Speed of Detection = Speed of Cost Reduction
Breaches contained within 200 days cost $3.87M; after 200 days: $5.01M. Every day of dwell time adds cost. AI cuts detection from 241 days to 51. XDR reduces lifecycle by 55 days. Invest in detection speed above all else.
3. Incident Response Plans Save More Than Any Technology
$2.66M savings per breach — the single largest cost reducer identified by IBM. Create, test, and regularly update your IR plan. Add zero-trust ($1.76M savings) and law enforcement engagement ($990K savings) for cumulative protection.
4. Supply Chain Risk Is Doubling Annually
Third-party breaches doubled YoY to 30% of incidents (IBM 2025). Supply chain breaches cost $4.91M. A single compromised vendor cascades to hundreds of victims (see: MOVEit, Snowflake). Vendor security assessment and third-party risk management are no longer optional.
5. Healthcare and the US Face Disproportionate Costs
Healthcare: $11.2M (2.5x global average, 15 years running). US: $10.22M (2.3x global, all-time high). These premiums reflect regulatory exposure, litigation risk, and the high value of the data these sectors handle. Industry-specific security investment must match industry-specific risk.
About This Data
This article draws from 140 statistics aggregated from 50+ authoritative sources including IBM Cost of a Data Breach, Verizon DBIR, CrowdStrike Global Threat Report, WEF Global Cybersecurity Outlook, FBI IC3, ISC2 Cybersecurity Workforce Study, Sophos, Gartner, Mandiant M-Trends, and Ponemon Institute reports.
Derived statistics (marked "Nathan House's Analysis") are computed by cross-referencing data from multiple sources — for example, comparing breach costs across industries using IBM data, or validating ransomware trends across Verizon, Sophos, and HIPAA Journal findings.
All statistics include inline source citations with links to primary sources. Data spans 2023-2026, with preference given to the most recent available figures. Last updated: May 2026.
How to Use This Data
Security professionals can use these data breach statistics to build business cases for cybersecurity investment, justify budget increases, benchmark their organisation against industry and country averages, and quantify the ROI of specific controls (AI/automation, zero-trust, IR plans).
For CISOs and security leaders: Use the $4.44M average breach cost, $2.66M IR plan savings, and $1.9M AI savings to justify security budget to the board. The cost-of-not-investing argument is now data-driven: every control has a quantifiable savings figure.
For risk managers: Use the industry and country cost data to model breach exposure for cyber insurance, risk registers, and board reporting. The 200-day cost threshold provides a clear KPI for detection capability improvement.
For journalists and researchers: All statistics include inline source citations with links to primary sources. Derived statistics are clearly marked as "Nathan House's Analysis" with computation methodology shown.
This page is updated monthly as new reports are published. Bookmark it and return for the latest data breach statistics. If you spot an outdated statistic or want to suggest a source, contact us.
About the Author

Nathan House, StationX
Nathan House is a cybersecurity expert with 30 years of hands-on experience. He holds OSCP, CISSP, and CEH certifications, has secured £71 billion in UK mobile banking transactions, and has worked with clients including Microsoft, Cisco, BP, Vodafone, and VISA. Named Cyber Security Educator of the Year 2020 and a UK Top 25 Security Influencer 2025, Nathan is a featured expert on CNN, Fox News, and NBC. He founded StationX, which has trained over 500,000 students in cybersecurity.
Primary Sources
IBM Cost of a Data Breach Report 2025
Global average costs, industry/country breakdowns, AI impact, detection times, defense ROI
Verizon DBIR 2025
Breach volumes, human element, attack vectors, credential theft, financial motives
CrowdStrike Global Threat Report 2025
Cloud intrusions, credential incidents, eCrime breakout time, nation-state threats
Ponemon Institute 2025
Insider threat costs, healthcare cyberattack rates, negligent employee data
Surfshark Data Breach Research
Global breached account counts, country-level leak data, cumulative breach data
Stanford University
Human error breach causation research (88%)
❓ Frequently Asked Questions About Data Breaches
How much does a data breach cost?
The global average cost of a data breach is $4.44 million (IBM Cost of a Data Breach 2025). In the US, that figure is $10.22 million. Healthcare breaches cost $11.2 million on average. Costs include incident response, legal fees, regulatory fines, customer notification, credit monitoring, business disruption, and reputational damage.
How long does it take to detect a data breach?
The average organisation takes 181 days to identify a breach and 60 days to contain it — a total lifecycle of 241 days (IBM 2025). With AI/automation, detection drops to 51 days. The median breach discovery time is 24 days for the fastest detectors (Verizon DBIR 2025).
What is the most common cause of data breaches?
82% of breaches involve the human element (Verizon DBIR 2025). Stolen or compromised credentials are the most common initial attack vector (29% of breaches, Verizon 2025), followed by ransomware/extortion, exploited vulnerabilities, and phishing. 70% of breaches originate from external actors (IBM 2025).
Which industry has the highest breach costs?
Healthcare has led all industries for 15 consecutive years at $11.2 million per breach (IBM 2025). Financial services is second at $6.08 million, followed by critical infrastructure at $4.82 million. The healthcare premium is driven by regulatory costs (HIPAA), the high value of medical records, and critical system disruption impact.
How can organisations reduce breach costs?
The most effective cost reducers are: incident response plans ($2.66M savings), AI/automation in security operations ($1.9M savings), zero-trust architecture ($1.76M savings), and involving law enforcement ($990K savings). Organisations deploying all four can see combined savings exceeding the average breach cost itself.
How many data breaches happen per year?
Verizon confirmed 5,176 data breaches with verified data exposure in 2024. Surfshark tracked 5.2 billion accounts breached worldwide in 2025. The actual number of breaches is likely higher, as many incidents go unreported or undetected.
