Cloud Security Statistics [2026]: Key Data & Trends

82% of cloud breaches trace back to credential failures (Thales). 95% of cloud security failures stem from human error, not provider flaws (SentinelOne). And Gartner estimates that through 2026, 99% of cloud security failures will be the customer's fault.
You'll find 56+ statistics across 12 categories below -- from breach costs and misconfiguration rates to container security and market growth -- sourced from IBM, CrowdStrike, Fortinet, Gartner, Red Hat, and 30+ authoritative reports. Each section includes original analysis cross-referencing multiple data sets to surface insights no single vendor report can show you.
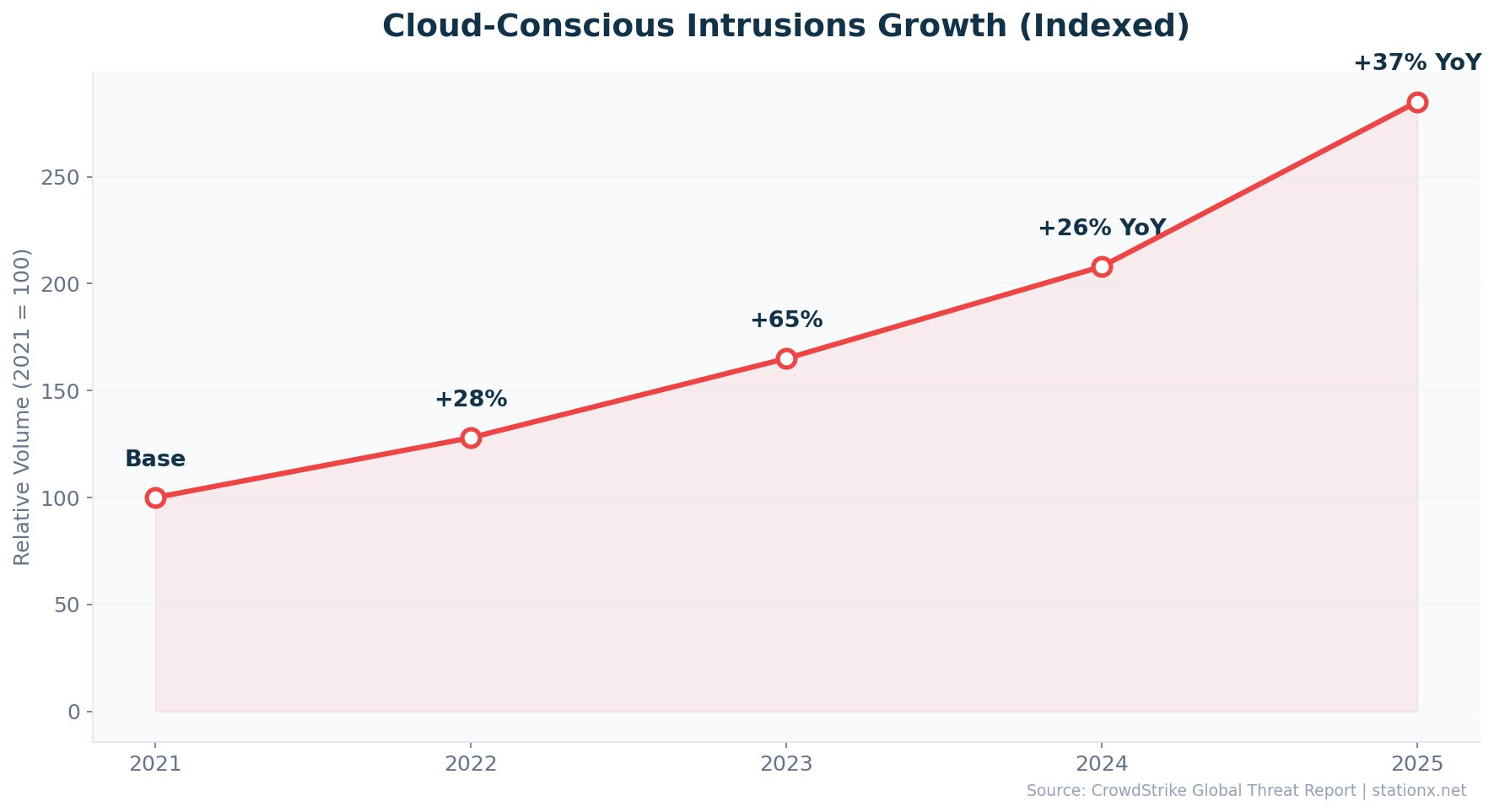
80% of organisations experienced a cloud breach in the past year. Cloud intrusions rose 26% then 37% year-over-year (CrowdStrike). The gap between cloud adoption and cloud security maturity is widening, and the data below shows exactly where.
Key Takeaways
Last updated: May 2026- Multi-environment breaches cost $5.05M -- 26% more than on-premises ($4.01M) (IBM 2025)
- 80% of organizations experienced a cloud security breach in the past year (SentinelOne)
- Cloud intrusions rose 37% year-over-year in 2025, accelerating from 26% growth in 2024 (CrowdStrike)
- 88% of organizations now operate in hybrid or multi-cloud environments (Fortinet 2026)
- 70% of cloud breaches originate from compromised identities (SentinelOne)
- 90% of organizations experienced a Kubernetes security incident (Red Hat)
- The cloud security market will grow from $35.84B to $75.26B by 2030 (Grand View Research)
- Only 18% of organizations have fully operational AI-driven cloud threat detection (Fortinet 2026)
☁ Key Cloud Security Numbers
Cloud security incidents are surging. Significant cloud breaches jumped 154% year-over-year, with 61% of organizations reporting a major incident in 2024 compared to 24% in 2023 (SentinelOne). 80% of organizations experienced at least one cloud security breach in the past 12 months. The scale of the problem is substantial: 45% of all data breaches now occur in cloud environments, and 25% of global cyber attacks specifically target cloud infrastructure.
The data points to a clear pattern: the overwhelming majority of cloud security failures are preventable. Gartner projects that 99% of cloud failures through 2026 will be the customer's fault, and SentinelOne data confirms that 95% stem from human error rather than provider flaws. Identity and credential management is the dominant attack surface, with 82% of breaches attributed to inadequate credential practices (Thales).
Meanwhile, the cloud security market is growing at 13.3% CAGR, from $35.84 billion in 2024 to a projected $75.26 billion by 2030 (Grand View Research). Organizations are investing heavily, with 62% expecting to increase cloud security budgets (Fortinet 2026) and cloud security absorbing 34% of total IT security spending on average. But the data shows spending alone does not solve the problem: 59% of organizations remain in early stages of cloud security maturity despite growing budgets.
The numbers below represent the current state of cloud security across breach costs, misconfiguration rates, identity attacks, multi-cloud challenges, container security, market size, and emerging AI threats. Each section includes original analysis cross-referencing IBM, CrowdStrike, Fortinet, Gartner, SentinelOne, Red Hat, and 30+ additional sources to surface insights that no single vendor report can provide.
| Finding | Value | Source |
|---|---|---|
| Cloud breaches from credential failures | 82% | Thales Group 2023 Cloud Security Study |
| Cloud security failures from human error | 95% | SentinelOne / Industry Reports |
| Cloud security failures that are customer's fault | 99% | Gartner |
| Organizations breached in past year | 80% | SentinelOne Cloud Security Statistics 2026 |
| Data breaches occurring in cloud environments | 45% | SentinelOne Cloud Security Statistics 2026 |
| Cloud intrusion increase (2025 YoY) | 37% | CrowdStrike 2026 Global Threat Report |
| Cloud intrusion increase (2024 YoY) | 26% | CrowdStrike 2025 Global Threat Report |
| Organizations in hybrid/multi-cloud environments | 88% | Fortinet 2026 Cloud Security Report |
| Average multi-environment breach cost | $5.05M | IBM Cost of a Data Breach 2025 |
| Cloud security market size (2024) | $35.84B | Grand View Research |
| Global attacks that are cloud-specific | 25% | SentinelOne Cloud Security Statistics 2026 |
| YoY surge in significant cloud breaches | 154% | SentinelOne Cloud Security Statistics 2026 |
Nearly All Cloud Failures Are Preventable
Cross-referencing Gartner (99% customer fault), SentinelOne (95% human error), and Thales (82% credential failures), the data converges on one conclusion: the vast majority of cloud breaches are self-inflicted. The problem is not cloud security technology -- it is how organizations configure, manage, and govern their cloud environments.
Cloud-conscious intrusions jumped 37% year-over-year in 2025 (CrowdStrike 2026), building on 26% growth in 2024. The acceleration in attack volume is matched by a surge in significant incidents: SentinelOne reports 154% more organizations experienced major cloud breaches compared to the prior year. One in four global cyber attacks (25%) now specifically targets cloud environments.
The cloud security market responds with rapid growth: from $35.84 billion in 2024 to a projected $75.26 billion by 2030 (Grand View Research). But market growth alone does not solve the problem. 88% of organizations now operate in hybrid or multi-cloud environments (Fortinet 2026), creating the complex, multi-boundary architectures that carry the highest breach cost of any deployment model (as shown in the environment comparison below).
💰 Cloud Data Breach Statistics
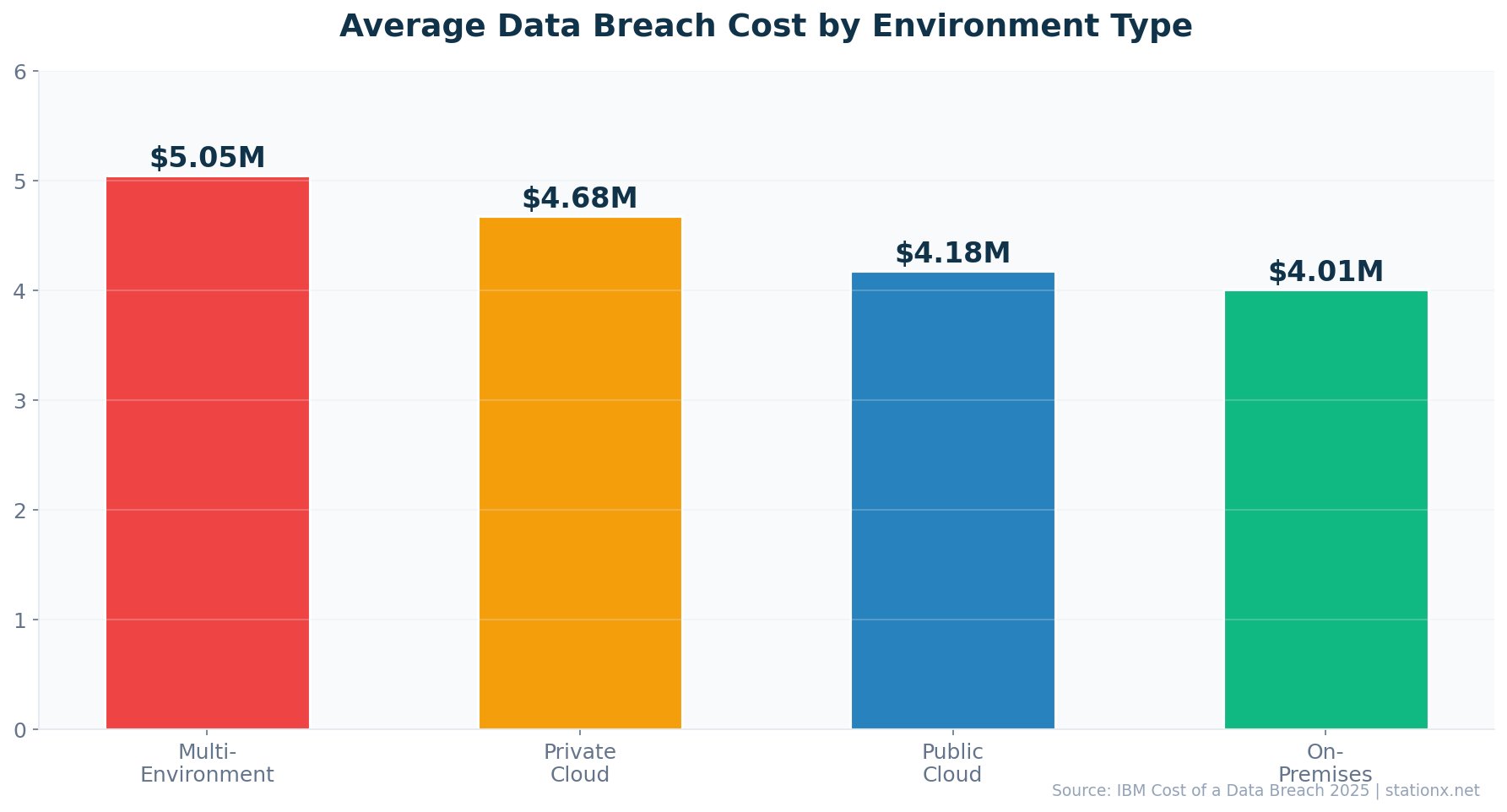
$5.05 million -- that is the average cost of a breach when data is stored across multiple environments, the highest of any configuration (IBM 2025). Private cloud breaches cost $4.68M, public cloud $4.18M, and on-premises $4.01M. The cost premium for multi-environment breaches is 26% above on-premises.
30% of breaches involved data distributed across multiple environments (IBM 2025). These cross-environment breaches take 276 days to identify and contain -- 12% longer than public cloud incidents at 247 days. Data sprawl creates blind spots that extend attacker dwell time and drive up costs.
80% of organizations experienced at least one cloud security breach in the past year (SentinelOne). The surge in significant cloud breaches -- up 154% year-over-year, with 61% of organizations reporting a major incident in 2024 compared to 24% in 2023 -- suggests cloud attacks are not just increasing in volume but also in severity. 45% of all data breaches now occur in cloud environments (SentinelOne), making cloud security a mainstream concern rather than a specialist one.
Breach Cost by Environment Type
The IBM data breaks down breach costs across four environment types. Multi-environment breaches ($5.05M) are the most expensive because data stored across public, private, and on-premises systems creates visibility gaps. Security teams struggle to correlate events across different logging systems, identity stores, and security consoles. Private cloud breaches ($4.68M) cost more than public cloud ($4.18M), possibly because private cloud environments are often custom-built with less mature security tooling than the native controls offered by AWS, Azure, and GCP.
Breach Detection and Containment
The breach lifecycle -- the time from initial compromise to full containment -- varies significantly by environment. Multi-environment breaches take 276 days on average. Public cloud breaches take 247 days. On-premises breaches, despite their lower cost, tend to have shorter lifecycles because security teams have direct physical access to systems, do not depend on provider APIs for forensics, and operate within a single authentication domain.
| Finding | Value | Source |
|---|---|---|
| Public cloud breach cost | $4.18M | IBM Cost of a Data Breach 2025 |
| Private cloud breach cost | $4.68M | IBM Cost of a Data Breach 2025 |
| Multi-environment breach cost | $5.05M | IBM Cost of a Data Breach 2025 |
| On-premises breach cost | $4.01M | IBM Cost of a Data Breach Report 2025 |
| Multi-environment breach lifecycle | 276 days | IBM Cost of a Data Breach 2025 |
| Public cloud breach lifecycle | 247 days | IBM Cost of a Data Breach Report 2025 |
| Breaches spanning multiple environments | 30% | IBM Cost of a Data Breach 2025 |
| Organizations with cloud breach in past year | 80% | SentinelOne Cloud Security Statistics 2026 |
| Data breaches in cloud environments | 45% | SentinelOne Cloud Security Statistics 2026 |
| YoY surge in significant cloud breaches | 154% | SentinelOne Cloud Security Statistics 2026 |
Data Sprawl Drives Both Cost and Detection Time
IBM data reveals a direct correlation between environment complexity and breach impact. Multi-environment breaches cost 26% more than on-premises ($5.05M vs $4.01M) and take 276 days to contain -- nearly 30 days longer than single-cloud deployments. Organizations storing data across public, private, and on-premises systems face the worst outcomes on every metric. This is not about cloud being less secure than on-premises; it is about visibility gaps when data crosses boundaries.
Most Expensive Environments
- Multi-environment: $5.05M per breach
- Private cloud: $4.68M per breach
- 276 days average breach lifecycle
Least Expensive Environments
- On-premises: $4.01M per breach
- Public cloud: $4.18M per breach
- 247 days average breach lifecycle
The breach cost gap between environments is significant but nuanced. Public cloud breaches are actually less expensive ($4.18M) than private cloud ($4.68M), likely because public cloud providers invest more in native security tooling. The highest costs come from data spanning multiple environments, where visibility gaps compound response time and containment effort.
Detection speed matters enormously. IBM data consistently shows breaches contained in under 200 days cost significantly less than those exceeding 200 days. For cloud environments specifically, the 276-day lifecycle for multi-environment breaches represents nearly nine months of attacker dwell time -- ample opportunity for lateral movement, data exfiltration, and privilege escalation.
The 30% Multi-Environment Problem
30% of all breaches now involve data distributed across multiple environments (IBM 2025). This is not a niche concern. When nearly a third of breaches cross environment boundaries, organizations cannot treat cloud security as a separate domain. Unified visibility across public cloud, private cloud, and on-premises is a prerequisite for reducing breach costs and detection times.
⚙ Cloud Misconfiguration Statistics
95% of cloud security failures stem from human error (SentinelOne). Misconfigurations are the single largest preventable cause of cloud breaches, with 45% of Kubernetes security incidents traced to misconfigured settings (Red Hat 2024) and 70% of organizations identifying misconfigured cloud services as a major risk (Fortinet 2026).
The misconfiguration problem is not limited to cloud-specific services. Storage buckets with public access, overly permissive IAM roles, unencrypted databases, disabled audit logging, and open network security groups are all configuration settings that default to insecure states in many services. Organizations without CSPM tools or infrastructure-as-code practices rely on manual configuration -- and manual processes at cloud scale inevitably produce errors.
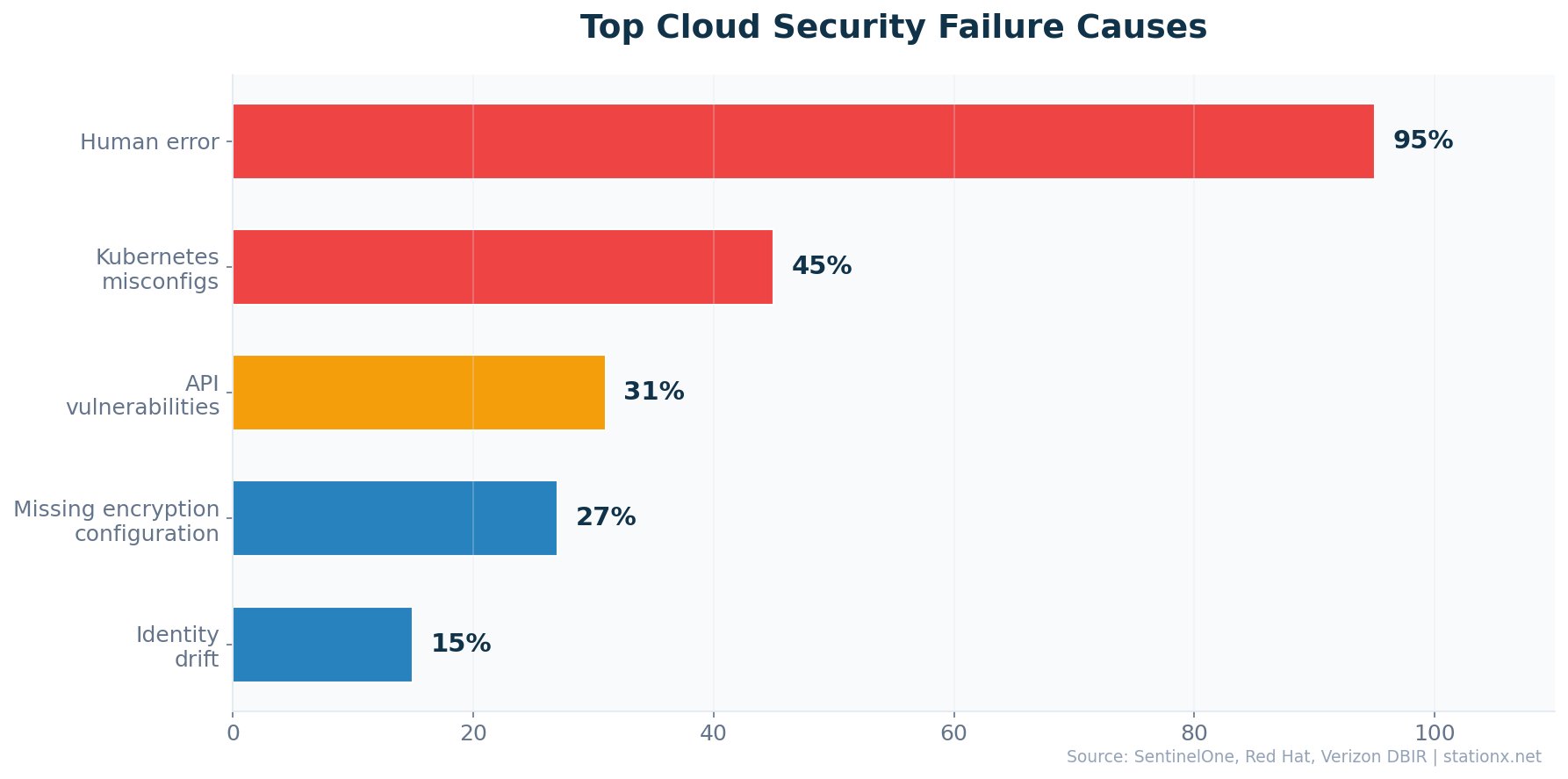
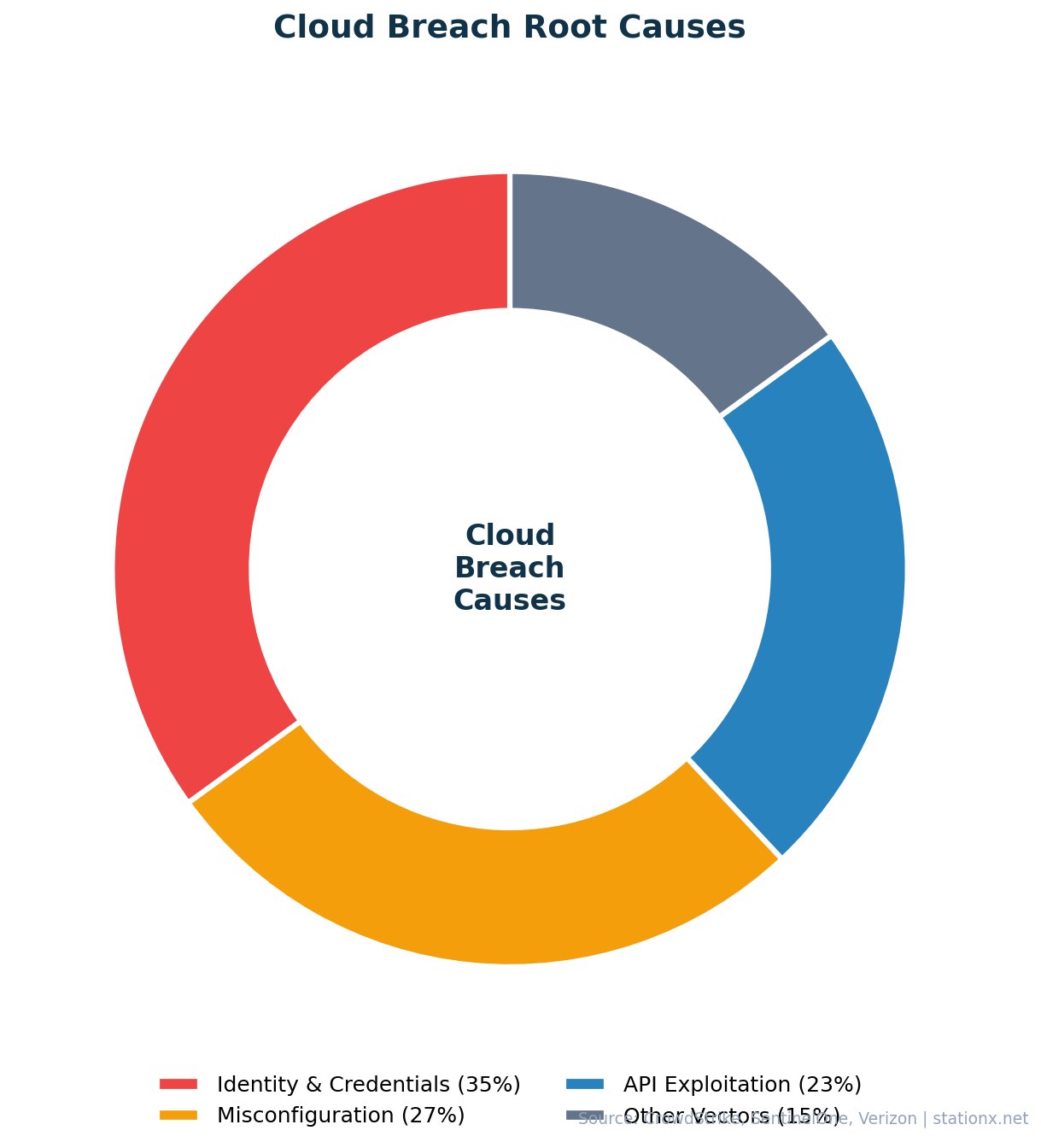
The Verizon DBIR found 15% of breaches involved cloud misconfigurations, while SentinelOne reports 27% of businesses experienced security incidents from public cloud misconfigurations in 2024. 70% of cloud resources were found to be publicly exposed without adequate controls (various sources). API exploitation accounts for 31% of cloud data breaches (SentinelOne).
| Finding | Value | Source |
|---|---|---|
| Cloud failures from human error | 95% | SentinelOne / Industry Reports |
| Cloud failures that are customer's fault | 99% | Gartner |
| Kubernetes incidents from misconfiguration | 45% | Red Hat |
| Organizations with public cloud misconfig incidents | 27% | SentinelOne |
| Breaches involving cloud misconfigurations | 15% | Verizon DBIR 2023 |
| Organizations identifying misconfigured services as major risk | 70% | Fortinet 2026 Cloud Security Report |
| Cloud resources publicly exposed | 70% | Astra / Industry Reports |
| Cloud breaches linked to API exploitation | 31% | SentinelOne Cloud Security Statistics 2026 |
The Shared Responsibility Misconception
Gartner's projection that 99% of cloud security failures through 2026 will be the customer's fault illuminates a persistent misconception. Many organizations assume their cloud provider handles security. In reality, cloud security operates on a shared responsibility model: the provider secures the infrastructure (physical data centers, hypervisors, network), while the customer secures everything above it (data, identity, configurations, access controls). The 95% human error rate (SentinelOne) reflects organizations failing to hold up their side of this model.
Common Misconfiguration Patterns
The most frequent cloud misconfigurations include: storage buckets with public access enabled, overly permissive IAM roles (especially wildcard permissions), security groups allowing unrestricted inbound traffic, unencrypted storage volumes, and disabled logging. Each of these is a configuration toggle -- a single setting that, when left in its default or insecure state, exposes the entire environment to attack. CSPM tools exist specifically to catch these, yet Fortinet data shows 59% of organizations remain in early cloud security maturity stages, meaning basic CSPM adoption is still incomplete.
Misconfiguration Is a Process Problem, Not a Technology Problem
Three independent data sets -- SentinelOne (95% human error), Gartner (99% customer fault), and Red Hat (45% K8s misconfigs) -- converge on the same finding: cloud security failures are overwhelmingly caused by how organizations set up their environments, not by flaws in cloud platforms. Fortinet's 2026 report adds context: 59% of organizations are still in early stages of cloud security maturity. The solution is not more tools -- 69% already cite tool sprawl as a barrier -- but better processes, automation, and training.
API vulnerabilities represent a growing attack surface. 31% of cloud data breaches are linked to API exploitation (SentinelOne), and the rise of microservices architectures means the number of API endpoints is growing exponentially. Organizations that lack API gateway controls and do not inventory their APIs are exposing their cloud environments to automated scanning and exploitation.
Only 21% of organizations encrypt 60% or more of their classified cloud data (SentinelOne). This means the majority of organizations store sensitive data in cloud environments without adequate encryption at rest. Combined with the 70% of cloud resources found publicly exposed, the misconfiguration problem extends well beyond access controls to fundamental data protection practices.
Top Misconfiguration Risks
- 95% from human error (SentinelOne)
- 45% K8s incidents from misconfiguration (Red Hat)
- 70% cloud resources publicly exposed
- 31% breaches from API exploitation
Mitigation Approaches
- CSPM tools for continuous posture monitoring
- Infrastructure as Code (IaC) for repeatable configs
- API gateway controls and inventory
- Automated secret scanning and rotation
🔑 Cloud Identity & Access Security
70% of cloud breaches now originate from compromised identities (SentinelOne). Identity has become the primary control plane -- and the primary attack surface. CrowdStrike reports 35% of cloud incidents in 2024 involved valid credential abuse, and 82% of all threat detections were malware-free, meaning attackers are logging in rather than breaking in.
77% of organizations rank identity and access security as their top cloud concern (Fortinet 2026). This reflects a fundamental shift in cloud attack methodology. Microsoft data shows 99% of identity attacks target passwords, yet the industry continues to underinvest in identity protection. Thales found 82% of cloud breaches trace back to inadequate credential management practices.
| Finding | Value | Source |
|---|---|---|
| Cloud breaches from compromised identities | 70% | SentinelOne / Industry Reports |
| Cloud breaches from credential management failures | 82% | Thales Group 2023 Cloud Security Study |
| Cloud incidents involving valid credentials | 35% | CrowdStrike 2025 Global Threat Report |
| Identity attacks targeting passwords | 99% | Microsoft Digital Defense Report 2024 |
| Organizations ranking IAM as top cloud concern | 77% | Fortinet 2026 Cloud Security Report |
| Threat detections that are malware-free | 82% | CrowdStrike 2026 Global Threat Report |
| Organizations with cloud breach in past year | 80% | SentinelOne Cloud Security Statistics 2026 |
| Cloud resources publicly exposed | 70% | Astra / Industry Reports |
Cloud Security Posture Checker
Answer 5 quick questions to assess your cloud security posture against industry benchmarks.
1. Do you enforce multi-factor authentication (MFA) on all cloud accounts?
2. Do you use a Cloud Security Posture Management (CSPM) tool?
3. Do you encrypt sensitive data at rest and in transit in cloud environments?
4. Do you audit and rotate service account keys/secrets regularly?
5. Do you have unified visibility across all cloud providers and on-premises?
Identity Is the New Perimeter
Three data sources confirm identity as the dominant cloud attack vector: SentinelOne (70% identity-based breaches), CrowdStrike (35% credential incidents, 82% malware-free detections), and Thales (82% credential management failures). Attackers are not exploiting zero-days or breaking encryption -- they are logging in with stolen, phished, or brute-forced credentials. The implication: MFA, least-privilege access, and credential rotation are now the highest-ROI security investments for cloud environments.
The shift to identity-based attacks reflects cloud architecture itself. In traditional on-premises environments, attackers needed network access first. In cloud environments, identity IS the access. A single compromised service account key can grant access to databases, storage buckets, and compute instances across an entire cloud tenant. The 99% of identity attacks targeting passwords (Microsoft) suggests most organizations have not moved to phishing-resistant MFA, hardware security keys, or certificate-based authentication.
Machine identities -- service accounts, API keys, and workload credentials -- outnumber human identities in most cloud environments by 10:1 or more. CrowdStrike data showing 82% malware-free detections means attackers are abusing legitimate credentials rather than deploying malware that could trigger endpoint detection. This renders traditional antivirus and signature-based detection almost irrelevant for cloud security.
Non-Human Identities and Service Accounts
The identity challenge extends beyond human users. Cloud environments contain tens of thousands of non-human identities: service accounts, API keys, IAM roles, federated identity providers, and workload credentials. These machine identities are often created with broad permissions during development and never scoped down for production. They are rarely rotated -- many organizations have service account keys that have not been changed in years. And they are typically not monitored with the same vigilance as human accounts.
CrowdStrike's documentation of adversaries abusing OAuth flows, hybrid identity synchronization, conditional access policies, and device registration processes shows how sophisticated identity attacks have become. Attackers do not just steal passwords -- they exploit the trust relationships built into cloud identity architectures. Federated identity, while convenient for user experience, creates trust chains that a single compromise can cascade through multiple environments.
Cloud Identity Security Best Practices
The data supports several priority actions for cloud identity security. Enforce phishing-resistant MFA (FIDO2 hardware keys or passkeys) on all accounts, not just privileged ones. Implement just-in-time (JIT) access for administrative privileges -- do not grant standing admin access. Inventory and audit all service accounts and API keys; delete those not used in 90 days. Deploy Cloud Infrastructure Entitlement Management (CIEM) to identify and remediate over-privileged identities. Monitor authentication patterns for anomalies: impossible travel, unusual login times, and first-time access to sensitive resources.
77% Agree IAM Is the Top Concern -- But Few Act Accordingly
Fortinet's finding that 77% of organizations rank identity and access security as their top cloud concern aligns perfectly with the data showing identity as the #1 attack vector. Yet the gap between concern and action is vast: 99% of identity attacks target passwords (Microsoft), meaning most organizations have not deployed phishing-resistant MFA. 35% of cloud incidents involve valid credentials (CrowdStrike), suggesting over-privileged accounts remain widespread. Knowing identity is the problem and solving it are clearly different things.
🌐 Multi-Cloud Security Challenges
88% of organizations now operate across hybrid or multi-cloud environments, up from 78% just one year earlier (Fortinet 2026). 81% rely on two or more cloud providers for critical workloads, and 29% use more than three. This rapid expansion creates compounding security complexity.
69% of organizations cite tool sprawl and visibility gaps as the top barrier to effective cloud security (Fortinet 2026). 66% lack confidence in their ability to detect and respond to cloud threats in real time. Meanwhile, 59% remain in early stages of cloud security maturity, and 64% would prefer a single-vendor unified platform if building their strategy fresh.
| Finding | Value | Source |
|---|---|---|
| Organizations in hybrid/multi-cloud | 88% | Fortinet 2026 Cloud Security Report |
| Using 2+ cloud providers | 81% | Fortinet 2026 Cloud Security Report |
| Using 3+ cloud providers | 29% | Fortinet 2026 Cloud Security Report |
| Multi-cloud adoption rate (2024) | 78% | Fortinet / Cybersecurity Insiders 2024 Cloud Security Report |
| Multi-cloud operations rate | 88% | SentinelOne / Industry Reports |
| Citing tool sprawl as top barrier | 69% | Fortinet 2026 Cloud Security Report |
| Lacking real-time detection confidence | 66% | Fortinet 2026 Cloud Security Report |
| Preferring single-vendor platform | 64% | Fortinet 2026 Cloud Security Report |
| In early cloud security maturity stages | 59% | Fortinet 2026 Cloud Security Report |
The Multi-Cloud Maturity Paradox
Fortinet's 2026 data reveals a striking disconnect: 88% of organizations operate multi-cloud, yet 59% remain in early stages of cloud security maturity. Only 18% have fully operational AI-driven detection. Multi-cloud adoption is outpacing security capability. The 69% citing tool sprawl as their top barrier suggests the problem is compounding -- more providers mean more tools, more tools mean more gaps, and more gaps mean more breaches. The data shows organizations need to consolidate before they can secure.
Multi-Cloud Adoption Trends
The shift from single-cloud to multi-cloud happened faster than security teams could adapt. In 2024, 78% of organizations reported multi-cloud adoption (Fortinet). By 2026, that number reached 88% -- a 10-percentage-point increase in just two years. 81% now rely on two or more cloud providers for critical workloads, and 29% use more than three providers. This expansion is driven by business needs: avoiding vendor lock-in, leveraging best-of-breed services, and meeting data residency requirements.
But multi-cloud adoption introduces compounding complexity. Each additional cloud provider brings its own identity model, its own security controls, its own compliance certifications, and its own logging format. Security teams must maintain expertise across AWS IAM, Azure AD, and GCP IAM simultaneously. The 69% citing tool sprawl as their top barrier reflects the operational reality of managing security across multiple cloud-native consoles, third-party tools, and legacy on-premises systems.
The Fortinet data showing 64% would prefer a single-vendor unified platform signals a market correction. Organizations that expanded to multi-cloud for agility are now realizing the security overhead. The convergence toward CNAPP (Cloud-Native Application Protection Platforms) and XDR (Extended Detection and Response) platforms reflects this demand for consolidation over best-of-breed fragmentation.
The Tool Sprawl Problem
69% of organizations cite tool sprawl and visibility gaps as their top cloud security barrier (Fortinet 2026). This is not just an inconvenience -- it directly impacts security outcomes. Each additional tool introduces its own dashboard, its own alert format, its own API, and its own team of administrators. Alert fatigue compounds: security teams receiving thousands of alerts from dozens of tools across multiple cloud providers cannot effectively triage or prioritize. The result is missed threats and longer dwell times.
The industry's response is platform consolidation. 64% of organizations would choose a single-vendor unified platform if building their cloud security strategy from scratch (Fortinet 2026). CNAPP platforms that combine CSPM, CWPP, container security, and cloud identity management in a single interface are growing rapidly. But only 27% still prefer best-of-breed approaches, reflecting specialized needs that unified platforms do not yet fully address.
Real-Time Detection Gaps
66% of organizations lack confidence in their ability to detect and respond to cloud threats in real time (Fortinet 2026). This is a critical gap: cloud attacks move at machine speed, with CrowdStrike documenting average breakout times of just 29 minutes. If 66% of organizations cannot detect threats in real time and attackers move from initial access to lateral movement in under 30 minutes, the majority of organizations are effectively blind to active attacks in their cloud environments.
The detection gap is partly a skills problem (74% impacted by cloud security skills shortages, SentinelOne) and partly a technology problem (only 18% with operational AI detection, Fortinet). Organizations that achieve real-time cloud detection typically combine cloud-native logging (CloudTrail, Azure Monitor, GCP Audit Logs) with SIEM/XDR platforms that correlate events across environments and apply behavioral analytics to identify anomalies.
Multi-Cloud Risks
- 69% cite tool sprawl as top barrier
- 66% lack real-time detection confidence
- 59% in early security maturity
- Highest breach cost tier (see environment comparison)
Multi-Cloud Benefits
- Avoid vendor lock-in
- Best-of-breed service selection
- Data residency compliance
- Resilience against provider outages
Cloud vs On-Premises: Breach Impact Comparison
Compare breach costs, detection times, and lifecycle across deployment environments.
Source: IBM Cost of a Data Breach Report 2025
The cost comparison data carries important nuances. As shown in the environment comparison, public cloud breaches are actually cheaper than private cloud, contradicting the assumption that private infrastructure is inherently more secure. Public cloud providers -- AWS, Azure, GCP -- invest billions in security engineering, threat detection, and compliance certifications that most organizations cannot replicate in private data centers. The cost advantage reflects the maturity of native security controls, not a difference in threat exposure.
The question is not "cloud vs on-premises" but "how many environments." Organizations with data in a single well-managed environment -- whether cloud or on-premises -- face lower costs and faster detection. The multi-environment premium exists because data crossing boundaries creates gaps that no single security tool can cover. Unified visibility across environments is the most effective cost-reduction strategy the data supports.
Single-Environment Deployments Outperform on Every Metric
IBM data shows organizations with data in a single environment -- whether public cloud or on-premises -- consistently outperform multi-environment deployments on both cost and detection time. As the environment comparison above shows, the ${multiEnvCostPremium}% multi-environment premium is not a cloud tax; it is a complexity tax. Organizations that can consolidate data into fewer environments or achieve genuine unified visibility across environments will reduce breach costs regardless of where their infrastructure sits.
📦 Container & Kubernetes Security
90% of organizations experienced at least one Kubernetes security incident in the past year (Red Hat 2024). Misconfiguration caused 45% of those incidents. 85% of container images in production carry high or critical vulnerabilities (Wiz 2025), and new AKS clusters face their first attack attempt within just 18 minutes of deployment.
The container security statistics paint a concerning picture. The market reached $3.24 billion in 2025 (Mordor Intelligence), reflecting the scale of Kubernetes adoption and the security challenges it creates. AI/ML workload deployments grew 500%, creating larger container images and slower vulnerability scanning cycles. The speed of container deployment clashes with the speed of security -- when an AKS cluster is under attack within 18 minutes, traditional scan-and-patch cycles cannot keep up.
| Finding | Value | Source |
|---|---|---|
| Organizations with K8s security incidents | 90% | Red Hat |
| K8s incidents caused by misconfiguration | 45% | Red Hat |
| Container images with high/critical vulnerabilities | 85% | Red Hat / Wiz Kubernetes Security Report 2025 |
| Time before new AKS cluster faces first attack | 18 min | Wiz Kubernetes Security Report 2025 |
| Container security market size | $3.24B | Mordor Intelligence |
Container Speed Exceeds Security Speed
Red Hat (90% K8s incidents), Wiz (85% images with critical vulns, 18-minute attack window), and Mordor Intelligence ($3.24B market) paint a clear picture: container adoption has outrun container security. The 45% of incidents caused by misconfiguration (Red Hat) echoes the broader cloud pattern -- human error, not sophisticated attacks, is the primary threat. With AI/ML workloads growing 500%, the attack surface is expanding faster than teams can secure it.
Kubernetes environments face a unique challenge: the ephemeral nature of containers means traditional vulnerability management does not work. Containers are created and destroyed in seconds, making point-in-time scanning insufficient. Runtime security -- monitoring containers during execution -- is becoming essential. Organizations need to shift left (scan images in CI/CD) and shift right (monitor runtime behavior) simultaneously.
The 45% misconfiguration rate in Kubernetes mirrors the broader cloud trend, but with higher stakes. A single misconfigured RBAC policy can grant cluster-admin privileges to a compromised pod. A missing network policy can allow lateral movement between namespaces. And the 85% of container images with high or critical vulnerabilities suggests most organizations are deploying known-vulnerable code into production.
The 18-Minute Window Changes Everything
Wiz data showing AKS clusters face attacks within 18 minutes of creation fundamentally changes the container security model. Organizations cannot rely on post-deployment scanning when attackers arrive before the first scan completes. The implication: secure-by-default configurations, immutable infrastructure, and admission controllers that block non-compliant workloads are no longer optional -- they are required from minute one.
Kubernetes Security Best Practices
The data suggests several high-priority actions for Kubernetes security. First, implement admission controllers (OPA Gatekeeper or Kyverno) to enforce security policies before pods are created -- blocking non-compliant deployments at the gate rather than remediating after deployment. Second, enable network policies to restrict pod-to-pod communication, limiting lateral movement if a container is compromised.
Third, scan container images in CI/CD pipelines and block deployment of images with critical vulnerabilities -- the 85% of images with high/critical vulnerabilities (Wiz) should never reach production if pipelines enforce vulnerability thresholds. Fourth, use pod security standards to prevent privileged containers, host network access, and root execution. Fifth, implement secrets management with tools like HashiCorp Vault or cloud-native secrets managers rather than embedding secrets in environment variables or configuration files.
Sixth, enable and centralize Kubernetes audit logging. Without audit logs, security teams have no visibility into API server activity, RBAC changes, or anomalous workload behavior. The 18-minute attack window for new AKS clusters means logging must be enabled from cluster creation -- not after the first incident. Organizations should route Kubernetes audit logs to their SIEM alongside cloud provider logs for cross-environment correlation.
Runtime security monitoring is equally critical. With 90% of organizations experiencing Kubernetes incidents and attackers targeting new clusters within minutes, detecting anomalous behavior during execution -- unexpected processes, network connections to known-bad IPs, privilege escalation attempts -- catches threats that pre-deployment scanning misses. The container security market's growth to $3.24 billion reflects demand for these runtime capabilities.
Service mesh technologies (Istio, Linkerd) add another layer of security by encrypting pod-to-pod communication (mTLS) and providing fine-grained traffic control. For organizations running sensitive workloads in Kubernetes, service mesh adoption addresses both the encryption gap (only 21% encrypting 60%+ of classified data) and the network segmentation challenge. The overhead is non-trivial, but for regulated industries the compliance benefits justify the complexity.
Image signing and verification (Cosign, Notary v2) ensure that only trusted, verified images run in production clusters. Combined with admission controllers that reject unsigned images, this creates a cryptographic chain of trust from build to runtime that addresses the container supply chain risk at a fundamental level. Organizations deploying these controls report significantly lower rates of configuration-related incidents.
Container Image Supply Chain
85% of container images in production carry high or critical vulnerabilities (Wiz 2025). Many of these originate in base images pulled from public registries. Organizations building on top of unvetted base images inherit every vulnerability in the base layer. The solution is a curated internal registry with approved, scanned base images that development teams must use. Combined with automated vulnerability scanning in CI/CD pipelines, this approach addresses the supply chain risk at the source rather than at deployment time.
The container and Kubernetes security challenge is fundamentally a speed problem. Development teams deploy new containers in seconds. Attackers target new clusters in minutes. Traditional security processes that operate on a weekly or monthly cadence cannot keep up. The organizations that succeed at container security will be those that embed security controls directly into the development pipeline -- automated scanning in CI/CD, admission controllers at the cluster boundary, and runtime monitoring during execution -- creating security that moves at development speed rather than forcing development to slow to security speed.
📈 Cloud Security Market & Spending
$35.84 billion -- the global cloud security market in 2024. By 2030, it will reach $75.26 billion, growing at a 13.3% CAGR (Grand View Research). The CASB/CWPP segment alone is worth $8.7 billion (Gartner 2025), and the CSPM market is projected to reach $7.02 billion by 2030 (Fortune Business Insights).
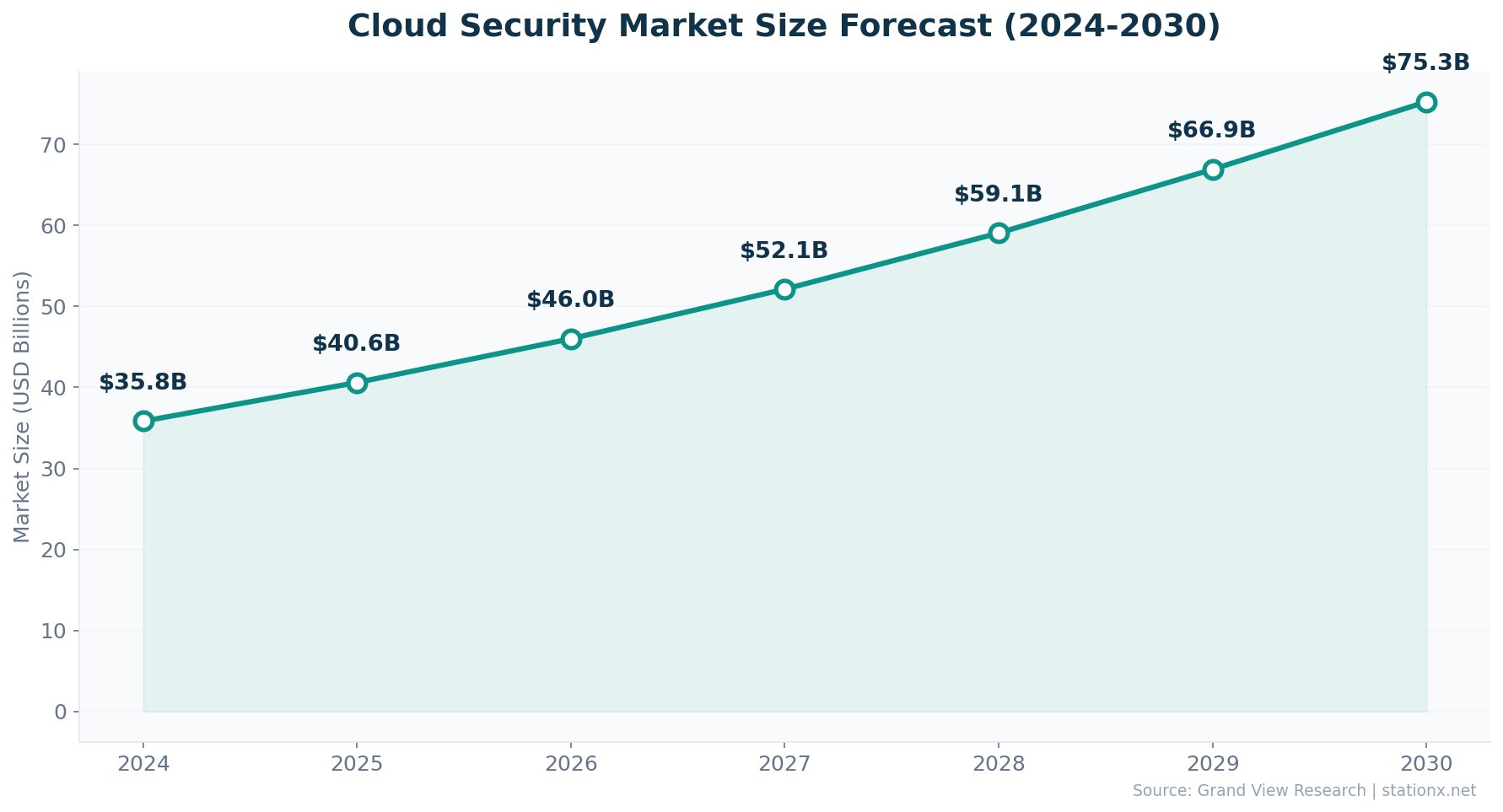
62% of organizations expect their cloud security budgets to increase over the next 12 months (Fortinet 2026). On average, cloud security absorbs 34% of total IT security spending. But 74% of organizations report being impacted by cloud security skills shortages, which constrains their ability to deploy the tools they are buying.
| Finding | Value | Source |
|---|---|---|
| Cloud security market (2024) | $35.84B | Grand View Research |
| Projected market size (2030) | $75.26B | Grand View Research |
| Market CAGR (2025-2030) | 13.3% | Grand View Research |
| CASB/CWPP market size | $8.7B | Gartner |
| CSPM market projection (2030) | $7.02B | Fortune Business Insights |
| Container security market | $3.24B | Mordor Intelligence |
| Organizations increasing cloud security budget | 62% | Fortinet 2026 Cloud Security Report |
| IT security budget allocated to cloud | 34% | Fortinet 2026 Cloud Security Report |
| Impacted by cloud security skills shortage | 74% | SentinelOne Cloud Security Statistics 2026 |
Spending Growth Outpaces Maturity Growth
The cloud security market is doubling in 6 years ($35.84B to $75.26B), and 62% of organizations are increasing budgets. But Fortinet data shows 59% remain in early cloud security maturity, and only 18% have operational AI detection. The skills gap (74% impacted) explains the disconnect -- organizations are buying tools faster than they can staff teams to use them. Budget without maturity is spending, not security.
Market Segment Breakdown
The cloud security market splits across several distinct segments. CASB (Cloud Access Security Broker) and CWPP (Cloud Workload Protection Platform) solutions collectively represent an $8.7 billion market (Gartner 2025). CSPM (Cloud Security Posture Management) is the fastest-growing segment, projected to reach $7.02 billion by 2030 from $2.21 billion in 2024 -- a 19.8% CAGR driven by the misconfiguration crisis documented above.
Container security ($3.24 billion, Mordor Intelligence) is growing as Kubernetes adoption expands. The CNAPP (Cloud-Native Application Protection Platform) segment is converging CSPM, CWPP, and container security into unified platforms -- reflecting the 64% of organizations that would prefer a single-vendor approach (Fortinet 2026). Asia Pacific is the fastest-growing region at 15% CAGR, driven by cloud migration among SMEs and government digitization initiatives.
The Skills Gap Impact on Spending
74% of organizations report being impacted by cloud security skills shortages (SentinelOne). This creates a paradox: organizations invest in advanced security tools but lack the staff to deploy, tune, and maintain them. Fortinet data showing 59% in early security maturity despite 62% increasing budgets confirms the pattern. The skills gap is not just a staffing problem -- it is a spending effectiveness problem.
Cloud Security Technology Landscape
The cloud security market includes several overlapping technology categories. CASB (Cloud Access Security Broker) solutions sit between users and cloud services to enforce security policies -- controlling access, monitoring activity, and preventing data loss. CWPP (Cloud Workload Protection Platform) secures server workloads in cloud, containers, and serverless environments. CSPM (Cloud Security Posture Management) continuously monitors cloud configurations for compliance violations and misconfiguration risks.
CNAPP (Cloud-Native Application Protection Platform) represents the convergence of these categories into unified platforms. Vendors like Wiz, Palo Alto Prisma Cloud, and CrowdStrike Falcon Cloud Security offer integrated CSPM, CWPP, and container security in single dashboards. The 64% of organizations preferring a single-vendor approach (Fortinet 2026) drives this convergence. However, 27% still prefer best-of-breed tools, suggesting the market will remain segmented for years to come.
Zero trust architecture is increasingly applied to cloud environments. The zero-trust cloud security market is projected to reach $60 billion by 2027 (SentinelOne), with organizations investing in continuous verification of every user, device, and workload. IBM data shows organizations implementing zero trust save over $1 million per breach incident, validating the investment case.
Regional Market Growth
North America dominates cloud security spending, driven by the concentration of cloud-native companies, regulatory requirements (SOX, HIPAA, state privacy laws), and the highest breach costs globally. Europe follows, with GDPR compliance driving investment in data protection and cloud governance tools. Asia Pacific is the fastest-growing region at 15% CAGR (Grand View Research), as enterprises in India, Japan, Australia, and Southeast Asia accelerate cloud migration.
The Cloud Security Market Will Double in Six Years
Grand View Research projects the cloud security market will grow from $35.84B (2024) to $75.26B (2030) at 13.3% CAGR. This doubling reflects both increasing threat severity and growing regulatory pressure. The CSPM segment alone is projected to grow from $2.21B to $7.02B -- a 19.8% CAGR -- driven directly by the misconfiguration crisis that causes 95% of cloud failures. Organizations that delay cloud security investment face compounding risk as attack volumes accelerate faster than market growth.
🏢 Cloud Security by Industry
45% of data breaches now occur in cloud environments (SentinelOne), but the impact varies sharply by industry. Healthcare and financial services -- the most regulated sectors -- allocate 10-15% of their IT budgets to cybersecurity, compared to 8-12% for general enterprises. Government cloud investment is projected to hit $47.9 billion by 2025, driven by digital transformation and compliance mandates.
The multi-environment breach premium applies regardless of industry, but the operational impact depends on the sector. Healthcare faces HIPAA notification requirements, financial services faces regulatory scrutiny, and government agencies face national security implications. The 34% average cloud security budget share (Fortinet 2026) masks wide variation: high-threat industries invest considerably more.
Cloud adoption patterns differ significantly by sector. Financial services organizations tend to use private and hybrid cloud models for regulatory compliance, while technology companies lean toward public cloud. Government agencies are bound by frameworks like FedRAMP and IL4/IL5 certification levels. Each model carries different security implications: private cloud offers more control but higher management overhead; public cloud provides native security tools but requires trust in third-party infrastructure.
| Finding | Value | Source |
|---|---|---|
| Public cloud breach cost (cross-industry) | $4.18M | IBM Cost of a Data Breach 2025 |
| Private cloud breach cost (cross-industry) | $4.68M | IBM Cost of a Data Breach 2025 |
| Multi-environment breach cost | $5.05M | IBM Cost of a Data Breach 2025 |
| On-premises breach cost | $4.01M | IBM Cost of a Data Breach Report 2025 |
| Breaches in cloud environments | 45% | SentinelOne Cloud Security Statistics 2026 |
| Average cloud security budget share | 34% | Fortinet 2026 Cloud Security Report |
Highest Cloud Security Investment
- Healthcare: 10-15% of IT budget
- Financial services: Top global spender
- Government: $47.9B cloud investment
Industry Risk Factors
- 45% of all breaches in cloud environments
- Multi-env breaches carry the highest cost tier across sectors
- 74% impacted by cloud security skills shortage
Cloud Security Budget Does Not Equal Cloud Security
The industry data highlights a disconnect between spending and outcomes. Healthcare and financial services spend 10-15% of IT budgets on security -- above the 8-12% enterprise average -- yet still face the highest breach costs. The Fortinet finding that 59% of organizations are in early cloud security maturity stages applies across industries. Budget allocation is necessary but not sufficient; maturity, process, and skills matter more than the size of the security line item.
Healthcare Cloud Security
Healthcare faces the most expensive breach costs of any industry, with cloud migration accelerating as providers move to electronic health records, telemedicine platforms, and cloud-hosted diagnostic tools. HIPAA compliance requirements add complexity: healthcare organizations must encrypt PHI both at rest and in transit, maintain access logs, and implement business associate agreements with cloud providers. The 21% of organizations encrypting 60%+ of classified cloud data (SentinelOne) suggests most healthcare entities fall short of these requirements.
The convergence of healthcare IoT devices, cloud-hosted clinical data, and legacy on-premises systems creates the exact multi-environment architecture that IBM identifies as the highest breach-cost tier. Connected medical devices often run outdated software and connect to cloud platforms without adequate authentication controls, creating lateral movement paths that attackers exploit. Healthcare organizations face the dual challenge of securing sensitive patient data while maintaining system availability for clinical operations.
Financial Services Cloud Security
Financial services allocate the largest cloud security budgets globally, driven by regulatory mandates (PCI DSS, SOX, GDPR) and the direct financial exposure of cloud breaches. Banks and investment firms face unique multi-cloud challenges: they often use separate cloud providers for customer-facing applications, trading systems, and analytics workloads, creating the multi-environment complexity that IBM identifies as the most expensive breach scenario.
Real-time transaction processing adds latency sensitivity that constrains security implementations. Financial services organizations must balance security controls against transaction speed -- a challenge that pushes them toward cloud-native security tools that operate inline without adding latency. The industry's early adoption of zero trust architectures reflects the need to verify every transaction and access request without impacting service delivery.
Government Cloud Security
Government cloud investment reaching $47.9 billion reflects the scale of public-sector digital transformation. FedRAMP and StateRAMP frameworks set strict cloud security baselines, but adoption is uneven. The nation-state threat landscape adds urgency: CrowdStrike reports cloud-conscious intrusions by state-nexus actors increased 266% in 2025, with government agencies as primary targets for espionage-motivated cloud attacks.
Government agencies face unique procurement and staffing challenges that slow cloud security deployment. Federal hiring processes can take 6-12 months for cleared cybersecurity professionals, and the pay gap between government and private-sector roles exacerbates the 74% skills shortage reported by SentinelOne. The combination of high-value targets, sophisticated adversaries, and constrained resources makes government cloud security particularly challenging.
Technology and SaaS Companies
Technology companies are both the builders and heaviest users of cloud infrastructure. Their exposure is unique: they host customer data in cloud environments, making their security posture directly impact their customers' security. A breach in a SaaS provider can cascade to thousands of downstream organizations. The supply chain dimension (54% citing supply chain as cyber barrier, WEF 2025) is most acute for cloud-native technology companies whose products are the supply chain.
🤖 AI and Cloud Security
AI-enabled adversary operations increased 89% year-over-year (CrowdStrike 2026). 82% of detections were malware-free -- attackers are using AI for reconnaissance, credential theft, and evasion rather than deploying traditional malware. On the defensive side, organizations using AI and automation save $1.9 million per breach and contain incidents 108 days faster (IBM 2025).
But only 18% of organizations have fully operational AI-driven cloud threat detection (Fortinet 2026). 32% limit AI adoption to pilot efforts. The gap between AI-powered attackers and AI-equipped defenders creates asymmetric risk -- adversaries move faster than most security teams can respond. 25% of all global attacks now specifically target cloud environments (SentinelOne).
| Finding | Value | Source |
|---|---|---|
| AI-enabled adversary operations increase | 89% | CrowdStrike 2026 Global Threat Report |
| Detections that are malware-free | 82% | CrowdStrike 2026 Global Threat Report |
| Organizations with fully operational AI detection | 18% | Fortinet 2026 Cloud Security Report |
| Global attacks that are cloud-specific | 25% | SentinelOne Cloud Security Statistics 2026 |
The AI Asymmetry Gap in Cloud Security
CrowdStrike reports AI-enabled adversary operations grew 89%, while Fortinet shows only 18% of organizations have operational AI detection. This asymmetry is the defining cloud security challenge of 2026. Attackers weaponize AI to craft phishing, automate credential stuffing, and evade detection at machine speed. Defenders deploy AI in pilots that never scale. IBM data showing $1.9M savings with security AI proves the ROI case -- but the 82% who lack operational deployment are fighting an arms race with last generation's tools.
The AI landscape in cloud security is a tale of two speeds. Attackers use large language models to generate convincing phishing emails at scale, automate reconnaissance of cloud APIs, and create polymorphic malware that evades signature-based detection. CrowdStrike observed adversaries injecting malicious prompts into GenAI tools at more than 90 organizations, treating AI systems themselves as attack vectors.
On the defensive side, organizations using security AI and automation extensively save $1.9 million per breach and contain incidents 108 days faster than those without (IBM 2025). AI-augmented security operations centers (SOCs) demonstrate a 50% reduction in mean time to detect and a 60% drop in manual triage workload. The ROI is clear, but the deployment gap persists: 32% limit AI to pilot efforts, and the jump from pilot to production requires data engineering, model training, and integration work that many security teams lack the bandwidth to complete.
AI as an Attack Surface
Cloud-hosted AI systems introduce a new category of security risk. Organizations deploying AI models on cloud infrastructure face threats including: prompt injection attacks that manipulate model outputs, model poisoning through compromised training data, data exfiltration through model inversion, and unauthorized access to AI endpoints. CrowdStrike documented adversaries targeting AI development platforms directly -- not just using AI as a tool, but treating cloud-hosted AI systems as high-value targets for intellectual property theft and operational disruption.
The machine-to-human identity ratio in cloud environments now reaches 100:1 in many organizations, with AI agents and automated workflows creating thousands of service credentials that are rarely rotated and poorly monitored. As agentic AI systems gain the ability to make autonomous decisions and execute actions, the identity security challenge compounds. A compromised AI agent with elevated cloud permissions can cause damage at machine speed -- far faster than human security teams can intervene.
The AI Security Investment Case
IBM data makes the investment case clear: organizations with extensive security AI save $1.9M per breach, contain incidents 108 days faster, and achieve per-record breach costs of $128 versus $234 without AI -- a 45% reduction. But Fortinet data shows only 18% have reached operational AI detection maturity. The gap between proven ROI and actual deployment represents the largest single opportunity in cloud security. Organizations that close this gap gain a measurable competitive advantage in breach cost and response time.
AI-Enabled Attackers
- 89% increase in AI adversary operations (CrowdStrike)
- 82% of detections malware-free
- Prompt injection at 90+ organizations
- AI-crafted phishing at scale
AI-Enabled Defenders
- $1.9M savings per breach with AI (IBM)
- 108 days faster containment
- 50% reduction in MTTD
- Only 18% at operational maturity
⚠ Cloud Security Threats
Cloud-conscious intrusions rose 26% in 2024, then accelerated to 37% growth in 2025 (CrowdStrike). The trend is unmistakable: attackers are increasingly targeting cloud infrastructure, with 25% of all global cyber attacks now cloud-specific (SentinelOne). Microsoft processes 78 trillion security signals daily across its cloud platforms.
Supply chain vulnerabilities remain a persistent concern: 54% of organizations cite the supply chain as a significant barrier to cyber resilience (WEF 2025). API exploitation causes 31% of cloud data breaches (SentinelOne), and 70% of cloud resources were found to be publicly exposed without adequate protections. Only 21% of organizations encrypt 60% or more of their classified cloud data.
| Finding | Value | Source |
|---|---|---|
| Cloud intrusion increase (2024) | 26% | CrowdStrike 2025 Global Threat Report |
| Cloud intrusion increase (2025) | 37% | CrowdStrike 2026 Global Threat Report |
| Organizations citing supply chain as cyber barrier | 54% | WEF Global Cybersecurity Outlook 2025 |
| Cloud breaches from API exploitation | 31% | SentinelOne Cloud Security Statistics 2026 |
| Global attacks that are cloud-specific | 25% | SentinelOne Cloud Security Statistics 2026 |
| Microsoft security signals processed daily | 78 trillion | Microsoft Digital Defense Report 2024 |
| Cloud resources publicly exposed | 70% | Astra / Industry Reports |
| Organizations encrypting 60%+ of classified cloud data | 21% | SentinelOne Cloud Security Statistics 2026 |
Multi-Cloud Risk Explorer
Explore common misconfiguration risks and security data across major cloud providers.
Top AWS Misconfigurations
- S3 buckets with public access enabled
- Overly permissive IAM policies (wildcard permissions)
- Security groups allowing unrestricted inbound traffic
- Unencrypted EBS volumes and RDS instances
- CloudTrail logging disabled
Cloud Intrusion Growth Is Accelerating, Not Plateauing
CrowdStrike data across two consecutive annual reports shows cloud intrusions grew 26% in 2024, then 37% in 2025. The rate of growth is itself growing. Combined with SentinelOne's finding that 154% more organizations reported significant cloud breaches year-over-year, this is not a plateau -- it is an acceleration. Organizations planning cloud security strategies around static threat models are already behind. The growth trajectory suggests 2026 will be worse without fundamental changes to cloud security posture.
Cloud Threat Vectors in 2026
The cloud threat landscape in 2026 is shaped by five primary attack vectors. Identity and credential compromise leads at 70% (SentinelOne), followed by misconfiguration exploitation (95% of failures from human error, SentinelOne), API attacks (31% of cloud breaches, SentinelOne), supply chain compromises (54% citing supply chain as barrier, WEF), and cloud-native malware and ransomware. Each vector requires different defensive controls, which partly explains the 69% of organizations citing tool sprawl as their top barrier.
Supply Chain Attacks in Cloud Environments
54% of organizations cite the supply chain as a significant barrier to cyber resilience (WEF 2025). Cloud environments amplify supply chain risk because third-party integrations, open-source dependencies, and shared responsibility models create trust relationships attackers can exploit. A compromised CI/CD pipeline can inject malicious code into container images that propagate across production clusters before detection.
Cloud-native supply chain attacks target the build process itself: dependency confusion, compromised base images, and malicious Terraform modules are all vectors that bypass runtime security controls. The 85% of container images with critical vulnerabilities (Wiz) means the supply chain is already compromised at the image level for most organizations.
API Security as an Attack Surface
31% of cloud data breaches are linked to API exploitation (SentinelOne). As organizations build microservices architectures and expose APIs for partner integrations, the API attack surface grows. Common API security failures include: missing authentication on internal APIs, excessive data exposure in API responses, broken object-level authorization, and rate limiting failures. The rise of serverless functions and API gateways means API security is no longer a developer concern alone -- it is a critical cloud security domain.
The shift to cloud-native architectures means more communication happens via APIs rather than direct network connections. A traditional firewall cannot protect an API endpoint. Organizations need API-specific security controls: API gateways with authentication enforcement, API traffic monitoring for anomalous patterns, and API inventory management to identify shadow APIs that security teams do not know exist. The 70% of cloud resources found publicly exposed likely includes many unprotected API endpoints.
Nation-State Cloud Attacks
CrowdStrike reports cloud-conscious intrusions by state-nexus actors increased 266% in 2025. Nation-state attackers target cloud environments for espionage, intellectual property theft, and pre-positioning for potential conflict. These adversaries are highly skilled, well-resourced, and patient -- willing to maintain access for months or years before taking action. The 82% malware-free detection rate means these actors typically use stolen credentials and legitimate cloud tools to avoid triggering traditional security alerts.
Microsoft processes 78 trillion security signals daily across its cloud platforms, reflecting the scale of activity that requires monitoring. The volume alone creates a needle-in-a-haystack challenge: distinguishing adversary activity from legitimate cloud operations in environments generating billions of log entries per day. This is where AI-driven detection offers its greatest value -- processing signal volumes that human analysts cannot feasibly review.
Data Exposure and Encryption Gaps
Only 21% of organizations encrypt 60% or more of their classified cloud data (SentinelOne). This means the majority of sensitive data in cloud environments is either unencrypted or partially encrypted. Combined with the 70% of cloud resources found publicly exposed, the data exposure risk is substantial. Microsoft processes 78 trillion security signals daily, underscoring the scale of cloud activity that needs monitoring.
Cloud Encryption Remains Alarmingly Low
Only 21% of organizations encrypt 60%+ of classified cloud data (SentinelOne). This statistic is striking given that cloud providers offer encryption at rest by default in most services. The gap suggests organizations are not activating available controls, are using services that lack default encryption, or are failing to classify their data in the first place. Combined with 48% of organizations storing both encrypted and unencrypted classified data in cloud (SentinelOne), the encryption problem is not technology -- it is governance.
Cloud Threat Intelligence Landscape
The cloud threat landscape is shaped by three categories of adversaries. Financially motivated cybercriminals (the majority) target cloud environments for data theft, ransomware deployment, and cryptojacking. Nation-state actors (growing 266% in cloud intrusions, CrowdStrike) target cloud environments for espionage, pre-positioning, and intellectual property theft. And insider threats -- both malicious and negligent -- account for a significant portion of the 95% of incidents caused by human error (SentinelOne).
Each adversary type requires different defensive approaches. Financially motivated attackers can be deterred by raising the cost of attack: MFA, network segmentation, and rapid detection reduce the ROI of commodity attacks. Nation-state actors require threat intelligence integration, zero-trust architectures, and continuous monitoring that goes beyond signature-based detection. Insider threats require identity governance, access reviews, and user behavior analytics that can distinguish legitimate from anomalous activity.
Cloud Security Predictions for 2026
The trajectory of the data suggests several cloud security trends for 2026. Cloud intrusion growth will continue accelerating, building on the 26% to 37% acceleration documented by CrowdStrike. Identity-based attacks will remain the dominant vector, with non-human identities (service accounts, AI agents) becoming a larger share of compromised credentials. The CNAPP market will consolidate further as organizations prioritize platform convergence over best-of-breed tools.
AI will amplify both attack and defense capabilities, but the asymmetry gap (89% adversary growth vs 18% defender maturity) will widen before it narrows. Organizations that achieve operational AI detection will gain a measurable advantage -- the IBM data proving $1.9M savings per breach and 108 days faster containment will drive urgent investment. Container security will face increased scrutiny as AI/ML workloads continue to expand, creating larger attack surfaces with faster deployment cycles.
📋 Key Takeaways
- Identity is the primary attack vector. 70% of cloud breaches come from compromised identities, 82% from credential failures, and 82% of detections are malware-free. Invest in MFA, least privilege, and credential rotation before anything else.
- Multi-environment = maximum risk. Breaches spanning multiple environments carry the highest cost tier -- 26% more than on-premises (see the environment comparison). 30% of breaches involve data in multiple environments. Consolidate visibility before expanding infrastructure.
- Misconfiguration is a process failure. 95% of cloud failures are human error. 45% of K8s incidents stem from misconfiguration. The fix is not more tools (69% already cite tool sprawl) -- it is better automation, CSPM, and training.
- Cloud adoption outpaces security maturity. 88% operate multi-cloud, but 59% are in early security maturity. Only 18% have operational AI detection. Budget growth (62% increasing) means nothing without maturity growth.
- Container security is falling behind. 90% experienced K8s incidents. 85% of container images have critical vulnerabilities. New clusters face attacks within 18 minutes. Shift-left security and runtime protection are essential.
- AI creates asymmetric risk. AI adversary operations grew 89%, but only 18% of defenders have operational AI detection. Organizations using security AI save $1.9M per breach. The ROI case is proven -- the deployment gap is the problem.
- Cloud intrusions are accelerating. Growth went from 26% (2024) to 37% (2025). 25% of all global attacks are now cloud-specific. Static security strategies will not work against a dynamic threat curve.
- Encryption gaps are widespread. Only 21% encrypt 60%+ of classified cloud data. 70% of cloud resources are publicly exposed. Basic controls remain undeployed at scale.
What This Means for Security Leaders
The data across all sections points to a clear priority stack for cloud security investment. First, solve identity. 70% of breaches start with compromised credentials, and phishing-resistant MFA is the single highest-ROI control. Second, achieve unified visibility. Multi-environment breaches cost 26% more because teams cannot see across boundaries. Third, automate configuration management. 95% of failures are human error -- CSPM tools and infrastructure as code eliminate entire classes of misconfiguration.
For board presentations and budget justifications, the numbers speak clearly: multi-environment breaches carry the highest cost of any deployment model, security AI saves $1.9M per incident, and the cloud security market is growing at 13.3% CAGR because every organization recognizes the gap between cloud adoption and cloud security maturity.
The organizations that close this gap fastest will not be those with the largest budgets -- 59% in early maturity despite budget growth proves that. They will be those that focus on the fundamentals: identity, visibility, and configuration management, deployed consistently across every cloud environment.
Cloud Security Priority Matrix
Based on the data across all sections, the priority matrix for cloud security investment is:
Immediate (0-3 months)
- Enforce MFA on all cloud accounts
- Audit and reduce IAM permissions
- Enable encryption at rest everywhere
- Deploy CSPM for critical workloads
- Inventory all service accounts and API keys
Short-term (3-12 months)
- Implement unified visibility across environments
- Deploy container runtime security
- Establish infrastructure-as-code practices
- Integrate cloud logs into SIEM/XDR
- Evaluate CNAPP platform consolidation
Medium-term (12-24 months)
- Deploy AI-driven threat detection
- Implement zero-trust architecture
- Automate compliance monitoring
- Build cloud security CoE
- Conduct red team exercises on cloud
The priority ordering reflects the data: identity controls deliver the highest ROI because 70% of breaches start with compromised identities. Unified visibility is second because multi-environment breaches cost 26% more than single-environment. AI detection is high-value ($1.9M savings per breach) but requires foundational controls to be in place first. Organizations that skip fundamentals to deploy advanced capabilities are building on an unstable foundation.
❓ Frequently Asked Questions
How common are cloud security breaches?
80% of organizations experienced a cloud security breach in the past year (SentinelOne 2026). Significant cloud breaches surged 154% year-over-year, with 61% of organizations reporting a major incident in 2024 compared to 24% in 2023. 45% of all data breaches now occur in cloud environments.
Cloud-conscious intrusions grew 37% year-over-year in 2025 (CrowdStrike 2026), and 25% of all global cyber attacks now specifically target cloud infrastructure (SentinelOne). The frequency and severity of cloud breaches are both increasing simultaneously.
What percentage of data breaches are caused by cloud misconfigurations?
Multiple sources converge on misconfiguration as a leading cause. Verizon DBIR reports 15% of breaches involve cloud misconfigurations, SentinelOne reports 27% of organizations had public cloud misconfig incidents, and 95% of cloud security failures stem from human error. Red Hat found 45% of Kubernetes incidents are caused by misconfiguration.
Gartner projects that 99% of cloud security failures through 2026 will be the customer's fault, primarily due to misconfigurations. 70% of organizations identify misconfigured cloud services as a major risk (Fortinet 2026), and 70% of cloud resources are found to be publicly exposed without adequate controls.
How much does a cloud data breach cost?
Breach costs vary by environment type. Multi-environment breaches cost $5.05M on average, private cloud $4.68M, public cloud $4.18M, and on-premises $4.01M (IBM 2025). Multi-environment breaches also take the longest to contain at 276 days.
30% of breaches involve data distributed across multiple environments (IBM 2025). The 26% cost premium for multi-environment breaches reflects the visibility and coordination challenges of managing security across multiple cloud providers and on-premises systems simultaneously.
What is the biggest cloud security threat?
Identity and credential compromise is the biggest cloud security threat. 70% of cloud breaches originate from compromised identities (SentinelOne), 82% are attributed to credential management failures (Thales), and 35% of cloud incidents involve valid credential abuse (CrowdStrike). 77% of organizations rank identity and access security as their top cloud concern (Fortinet 2026).
Is cloud more secure than on-premises?
On-premises breaches cost the least of any environment type and have the shortest lifecycles. However, the data shows the issue is not cloud vs on-premises but rather how environments are managed. 99% of cloud security failures are the customer's fault (Gartner), and multi-environment setups with poor visibility create the highest risk.
Public cloud providers invest billions in security engineering and offer native controls that most organizations cannot replicate in private data centers. Public cloud breaches actually cost less than private cloud (see the environment comparison above), suggesting that well-managed public cloud can be cost-effective from a security perspective.
Properly configured cloud can be more secure, but most organizations have not reached that maturity level -- 59% are still in early stages (Fortinet 2026). The answer is not "cloud vs on-premises" but "how well-managed is your security posture regardless of environment."
What is the cloud security market size?
The global cloud security market was valued at $35.84 billion in 2024 and is projected to reach $75.26 billion by 2030, growing at a 13.3% CAGR (Grand View Research). Key segments include CASB/CWPP ($8.7B, Gartner 2025), CSPM (projected $7.02B by 2030), and container security ($3.24B, Mordor Intelligence).
62% of organizations expect their cloud security budgets to increase over the next 12 months (Fortinet 2026), with an average of 34% of total IT security spending allocated to cloud security. Asia Pacific is the fastest-growing region at 15% CAGR.
How fast are cloud attacks growing?
Cloud-conscious intrusions grew 26% year-over-year in 2024, then accelerated to 37% growth in 2025 (CrowdStrike). The rate of growth is itself increasing. Significant cloud breaches surged 154% year-over-year, with 25% of all global cyber attacks now specifically targeting cloud environments (SentinelOne).
AI-enabled adversary operations increased 89% (CrowdStrike 2026), and cloud-conscious intrusions by state-nexus actors rose 266% in 2025. The acceleration in cloud attacks reflects both the growing value of cloud-hosted data and the expanding attack surface created by multi-cloud adoption.
About This Data
This article draws from 56 statistics aggregated from 50+ authoritative sources including IBM Cost of a Data Breach, Verizon DBIR, CrowdStrike Global Threat Report, WEF Global Cybersecurity Outlook, FBI IC3, ISC2 Cybersecurity Workforce Study, Sophos, Gartner, Mandiant M-Trends, and Ponemon Institute reports.
Derived statistics (marked "Nathan House's Analysis") are computed by cross-referencing data from multiple sources — for example, comparing breach costs across industries using IBM data, or validating ransomware trends across Verizon, Sophos, and HIPAA Journal findings.
All statistics include inline source citations with links to primary sources. Data spans 2023-2026, with preference given to the most recent available figures. Last updated: May 2026.
How to Use This Data
Security professionals can use these cloud security statistics to build business cases for CSPM, IAM, and unified visibility investments. Compare your organization's posture against the benchmarks above to identify gaps. Use the breach cost comparisons and environment-specific data to justify budget requests with hard numbers that resonate with executive decision-makers.
For business cases: Use the environment comparison data from the breach costs section to quantify the cost of cloud complexity. Pair with the 276-day detection lifecycle to show the time-to-value of unified visibility investments. The Fortinet data on 62% budget increases and 34% cloud security budget share provides industry benchmarks for budget planning.
For risk assessments: The Cloud Security Posture Checker tool above gives a quick benchmark. For deeper analysis, map your organization against the Fortinet cloud maturity model (59% in early stages) and the identity security indicators (70% identity-based breaches, 82% credential failures).
For board presentations: Lead with the three headline numbers -- 82% credential breaches, the multi-environment breach premium, 37% intrusion growth. Use the IBM environment comparison chart to make the case visually. Close with the market growth data ($35.84B to $75.26B) to show this is a sector-wide investment priority, not a discretionary expense.
This page is updated monthly as new reports are published. Bookmark it and return for the latest cloud security data. If you spot an outdated statistic or want to suggest a source, contact us.
Sources Used in This Article
This analysis draws from 56+ statistics aggregated from authoritative sources across the cloud security industry. Primary data sources include:
- IBM Cost of a Data Breach Report 2025 -- breach costs by environment type, lifecycle data, AI impact
- CrowdStrike Global Threat Report 2026 -- cloud intrusion trends, malware-free detections, AI adversary data
- Fortinet 2026 Cloud Security Report -- multi-cloud adoption, maturity levels, spending, tool sprawl
- SentinelOne Cloud Security Statistics 2026 -- breach rates, identity data, API breaches, encryption gaps
- Red Hat State of Kubernetes Security 2024 -- container incidents, misconfiguration causes
- Gartner -- cloud customer fault projections, CASB/CWPP market sizing
- Wiz Kubernetes Security Report 2025 -- container vulnerabilities, attack speed data
- WEF Global Cybersecurity Outlook 2025 -- supply chain barriers, geopolitical context
- Grand View Research -- cloud security market size and CAGR projections
- Thales Cloud Security Study -- credential management and breach attribution
Derived statistics (marked "Nathan House's Analysis") are computed by cross-referencing data from multiple sources. All statistics include inline source citations with links to primary reports.
About the Author

Nathan House, StationX
Nathan House is a cybersecurity expert with 30 years of hands-on experience. He holds OSCP, CISSP, and CEH certifications, has secured £71 billion in UK mobile banking transactions, and has worked with clients including Microsoft, Cisco, BP, Vodafone, and VISA. Named Cyber Security Educator of the Year 2020 and a UK Top 25 Security Influencer 2025, Nathan is a featured expert on CNN, Fox News, and NBC. He founded StationX, which has trained over 500,000 students in cybersecurity.
Related Cybersecurity Statistics
Cloud security sits within a broader cybersecurity landscape. The breach cost data referenced in this article comes from the same IBM research that underpins our data breach statistics page. The identity attack patterns documented by CrowdStrike connect to our broader cybercrime analysis. Explore these related collections for comprehensive coverage of adjacent topics.
