Cybersecurity Trends [2026]: Data, Threats & Predictions

92% of cybersecurity leaders expect a catastrophic cyber event within two years (WEF 2026). The average eCrime breakout time has crashed to 29 minutes — 65% faster than 2024 — with the fastest observed at 27 seconds (CrowdStrike 2026 Global Threat Report). AI-enabled attacks surged 89% year-over-year (CrowdStrike), and 82% of all detections are now malware-free. These are not predictions — these are the cybersecurity trends already reshaping how you need to defend your organisation in 2026.
I've analysed the latest data from WEF, IBM X-Force, CrowdStrike, Gartner, Verizon DBIR, Sophos, Mandiant/Google, Fortinet, and Unit 42 to identify the 14 cybersecurity trends that matter most this year. Each section gives you a clear thesis backed by data, derived analysis you won't find elsewhere, and practical takeaways. Whether you're a CISO building a board presentation or a security professional tracking emerging cyber security trends, you'll find the evidence base here.
Cybersecurity Trends at a Glance
🤖 AI Attacks Surging
89% increase in AI-enabled attacks
94% say AI is #1 cyber change driver
57% of workers use unapproved GenAI
CrowdStrike, WEF, Gartner
🛡️ AI Defence Paying Off
$1.9M saved per breach with AI/automation
34% breach cost reduction
IBM
🔗 Supply Chain 4x
Compromises nearly 4x since 2020
Third-party breaches doubled to 30%
IBM, Verizon DBIR
🔐 Ransomware Fragmenting
109 active groups (+49% YoY)
51 brands — 88% deploy outside hours
IBM, Sophos
⚡ Response Window Shrinking
29 min avg breakout (fastest: 27 sec)
Zero-day windows: 48 hours
CrowdStrike, Mandiant
🔑 Identity Is the New Perimeter
67% of incidents start with identity
82% of detections are malware-free
Sophos, CrowdStrike
☁️ Cloud Under Siege
+37% cloud intrusions overall
+266% from state-nexus actors
CrowdStrike, IBM
📜 Regulation Converging
NIS2 + DORA + EU AI Act all enforcing
GDPR fines hit record €2.1B
EU, Gartner
🔒 Zero Trust Mainstream
Adoption rising 41% → 63%
Saves $1.76M per breach
IBM, Gartner
💰 Spending Climbing
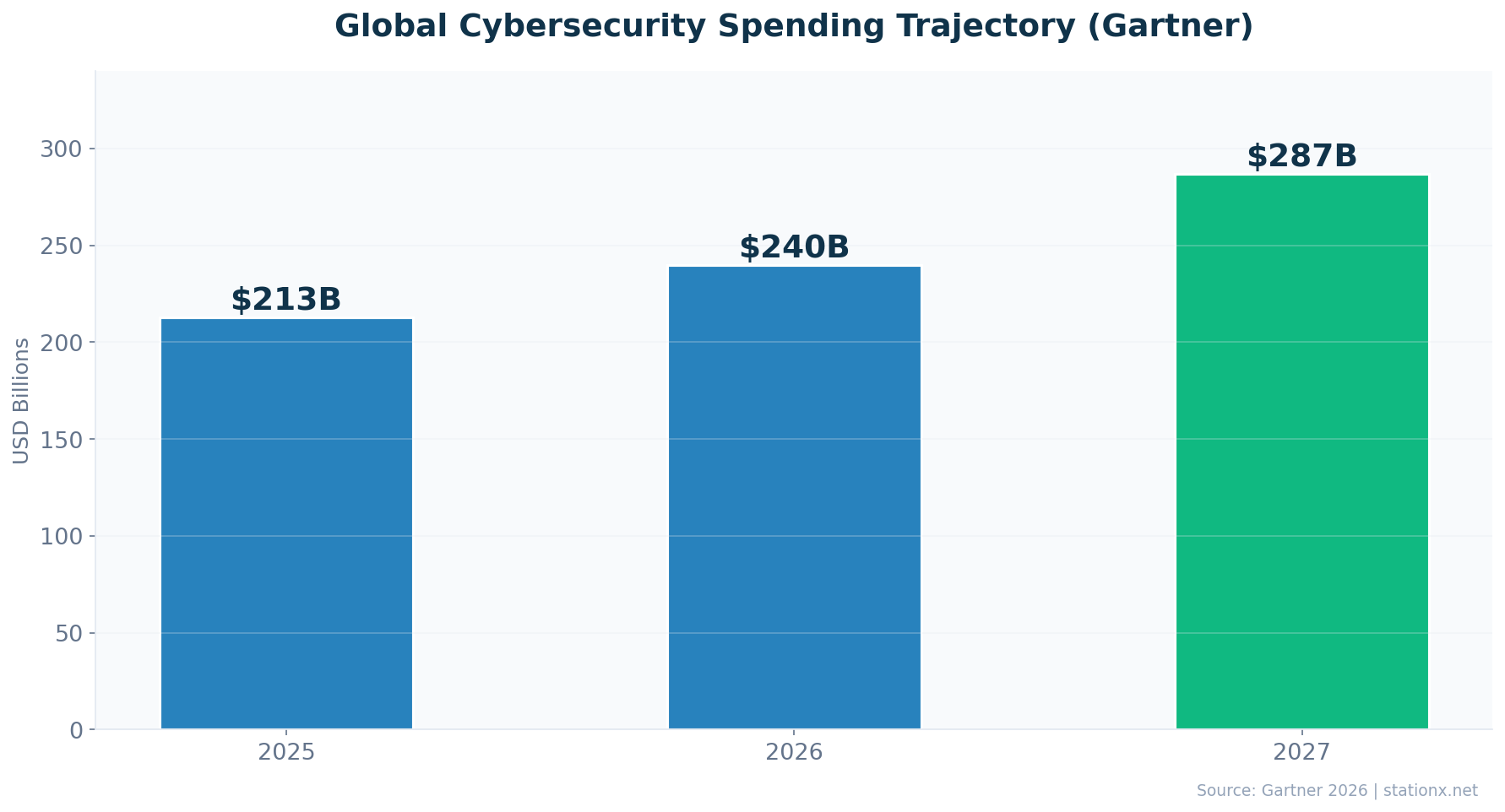
$213B → $240B → $287B
~11% CAGR through 2027
Gartner
Last updated: May 2026
📊 Cybersecurity Trends: The Data Behind the Headlines
The WEF Global Cybersecurity Outlook 2026 paints a stark picture: 92% of surveyed leaders expect a catastrophic cyber event within two years. Global cybercrime costs hit $10.5 trillion annually (Cybersecurity Ventures), and the average data breach costs $4.44 million (IBM). These headline numbers set the stage, but the real story is in the trends driving them — AI acceleration, supply chain contagion, identity-first attacks, and a regulatory reckoning.
The 2026 reporting season has delivered some of the most significant threat intelligence in years. CrowdStrike's 2026 Global Threat Report documented an 89% increase in AI-enabled attacks and a 29-minute average eCrime breakout time (down from 48 minutes). IBM X-Force's 2026 Index found that vulnerability exploitation has overtaken phishing as the top attack vector (40% of incidents), with 109 active ransomware groups representing a 49% increase. Sophos's Active Adversary Report 2026 confirmed identity as the dominant vector: 67% of incidents start with compromised credentials, and MFA was present in only 41% of cases. Mandiant/Google documented 48-hour zero-day exploitation windows and full cloud compromise via CI/CD chains in 72 hours. Together, these reports paint a picture of an offence moving faster, hitting harder, and scaling more efficiently than at any point in cybersecurity history.
The geopolitical dimension: Cybersecurity is now inseparable from geopolitics. 91% of the largest organisations have altered cybersecurity strategies due to geopolitical volatility (WEF 2026). China-nexus intrusions increased 38%, with an 85% surge in logistics sector targeting (CrowdStrike 2026). DPRK-nexus incidents rose 130%, including a $1.46 billion cryptocurrency theft — the largest single crypto heist in history. Cloud intrusions from state-nexus actors surged 266% (CrowdStrike 2026). 73% of respondents report personal exposure to cyber-enabled fraud (WEF 2026), and CEOs now rate cyber-enabled fraud as their top concern, displacing ransomware.
The Verizon DBIR perspective: Verizon's 2025 Data Breach Investigations Report, covering 22,000+ incidents and 12,195 confirmed breaches, provides the broadest empirical view. Third-party involvement in breaches doubled to 30%. Vulnerability exploitation grew 34% year-over-year to 20% of breach vectors. Ransomware appears in 44% of all breaches (up from 32%), with 88% of SMB breaches including ransomware versus 39% for large organisations. 54% of ransomware victims had prior credential exposures in infostealer logs. 15% of employees accessed GenAI on corporate devices, and 72% of those used non-corporate email accounts — creating a shadow AI surface that security teams cannot monitor.
The speed of exfiltration: Palo Alto Unit 42's Global Incident Response Report 2026, covering 750+ engagements across 50+ countries, documents dramatic acceleration: the fastest 25% of exfiltration events now complete in 1.2 hours (down from 4.8 hours), and the overall median exfiltration time is 72 minutes (down from approximately 5 hours). 87% of intrusions spanned multiple attack surfaces (endpoints, cloud, SaaS, identity). Over 90% of breaches stemmed from preventable gaps: misconfigurations, excessive identity trust, and unpatched systems.
The spending response: The market is pricing in the threat escalation. Gartner projects security and risk management spending reaching $240 billion in 2026, up from $213 billion in 2025, with a trajectory to $287 billion by 2027 at approximately 11% CAGR. Security services is the fastest-growing segment at $86.1 billion (2025), driven by the skills gap and the demand for managed detection and response. Cloud security spending is projected to grow from $8.7 billion in 2025 to $12.8 billion by 2027.
This is not a pure statistics roundup. Each section below identifies a specific cybersecurity trend, explains why it matters, and backs the thesis with data from multiple authoritative sources. Where the data permits, I've cross-referenced sources to produce original analysis — the kind of derived insights you won't find in any single vendor report. The future of cybersecurity is being shaped now. Here's what the data says.
Accelerating Threats
- AI-enabled attacks — +89% YoY (CrowdStrike 2026)
- Breakout time — 29 min avg, 27 seconds fastest
- Supply chain — nearly 4x since 2020 (IBM X-Force 2026)
- Cloud state-nexus intrusions — +266% (CrowdStrike 2026)
- Identity compromise — 67% of incidents (Sophos 2026)
- Ransomware groups — 109 active, +49% YoY (IBM 2026)
Defence Progress
- AI/automation — saves $1.9M per breach (IBM 2025)
- Zero trust — $1.76M breach cost reduction
- Ransom refusal — 64% now refuse to pay
- Security spending — $213B → $240B → $287B (Gartner)
- AI in security — 77% already using AI for defence (WEF)
| Finding | Value | Source |
|---|---|---|
| Global cybercrime damages annually | $10.5T | Cybersecurity Ventures |
| Projected global cybercrime cost by 2029 | $15.63T | Cybersecurity Ventures |
| Global average data breach cost | $4.44M | IBM Cost of a Data Breach Report 2025 |
| Global average breach cost (2024) | $4.88M | IBM Cost of a Data Breach Report 2024 |
| Ransomware present in breaches | 44% | Verizon DBIR 2025 |
| Expecting catastrophic cyber event within 2 years | 92% | WEF Global Cybersecurity Outlook 2026 |
| Time between cyberattacks | 39 seconds | Cobalt / University of Maryland |
| WEF: AI as key driver of cyber risk | 94% | WEF Global Cybersecurity Outlook 2026 |
| AI-enabled attack increase YoY (CrowdStrike 2026) | 89% | CrowdStrike 2026 Global Threat Report |
| Average eCrime breakout time (CrowdStrike 2026) | 29 minutes | CrowdStrike 2026 Global Threat Report |
| Breaches involving third parties | 30% | IBM Cost of a Data Breach Report 2025 |
| Supply chain/cloud compromises since 2020 (IBM 2026) | 4x | IBM X-Force Threat Intelligence Index 2026 |
| Unfilled cybersecurity positions globally | 4.8 million | ISC2 Cybersecurity Workforce Study 2025 |
| Security spending (2026, Gartner) | $240B | Gartner |
| Projected global cybersecurity spending | $520B | Cybersecurity Ventures |
| Weekly cyberattacks on organizations | 1,968 | VikingCloud / Check Point Research |
What's New in the 2026 Reports
Key changes from the latest reporting cycle compared to prior years:
- Breakout time collapsed: From 48 minutes (CrowdStrike 2025) to 29 minutes (CrowdStrike 2026), 65% faster
- Vuln exploitation overtook phishing: Now 40% of incidents vs phishing dropping (IBM X-Force 2026)
- Ransomware fragmentation: 109 active groups (+49%), a post-centralisation shift (IBM X-Force 2026)
- AI attacks nearly doubled: 89% YoY increase in AI-enabled adversary operations (CrowdStrike 2026)
- Supply chain 4x: Cloud/supply chain compromises nearly quadrupled since 2020 (IBM X-Force 2026)
- State-nexus cloud surge: 266% increase in cloud intrusions from nation-state actors (CrowdStrike 2026)
- Data leaks overtake adversarial AI as top AI concern: 34% vs 29% (WEF 2026), reversed from 2025
The Resilience Perception Gap
A 19-percentage-point gap between CBO confidence (64%) and CISO confidence (45%) in cyber resilience. Business leaders overestimate cyber resilience by nearly 20 percentage points compared to the security teams responsible for delivering it. (WEF Global Cybersecurity Outlook 2026)
🤖 AI-Powered Attacks Are Accelerating
The trend: AI has transformed cyber offence from a craft to a commodity. CrowdStrike's 2026 Global Threat Report recorded an 89% year-over-year increase in AI-enabled adversary operations — the steepest acceleration since AI entered the threat landscape. AI-generated phishing emails now match or exceed human-crafted versions in effectiveness while costing 95% less to produce (HBR 2024). 40% of business email compromise messages in Q2 2024 were AI-generated (VIPRE), and 82.6% of phishing emails are now AI-crafted (Abnormal 2025). The barrier to sophisticated social engineering has collapsed.
The scale: 94% of respondents in the WEF Global Cybersecurity Outlook 2026 now identify AI as the most significant driver of cybersecurity change — up from 66% in 2025. 87% flag AI-related vulnerabilities as the fastest-growing risk (WEF 2026). Gartner projects that by 2027, 17% of all cyberattacks and data leaks will involve GenAI. Deepfake fraud surged in 2024, with the largest single scam reaching $25.6 million via a deepfaked CFO video call (CrowdStrike). Adversaries are also targeting AI systems directly: CrowdStrike documented malicious prompts injected into GenAI tools at 90+ organisations for credential and crypto theft.
The shadow AI problem: 57% of workers use personal GenAI accounts for work, and 33% admit inputting sensitive data into unapproved tools (Gartner 2026). The WEF found that data leaks from GenAI (34%) now lead over adversarial AI capabilities (29%) as the top AI-related concern — a reversal from 2025 when adversarial capabilities dominated at 47%. This shift signals that organisations are recognising the insider risk of uncontrolled AI adoption alongside the external threat. IBM's X-Force 2026 assessment confirms that agentic AI accelerates existing attack playbooks — automated reconnaissance, vulnerability scanning, ransomware operations — but does not invent new attack classes. The implication: defenders need to move at machine speed to match machine-speed offence.
What it means for you: Traditional email security training built around spotting typos and suspicious links is obsolete. AI-generated phishing is grammatically perfect, contextually relevant, and personalised. Gartner lists the "death of traditional security awareness training" as one of its six top cybersecurity trends for 2026. Your defence strategy needs to shift from "spot the fake" to assume-breach detection — monitoring for anomalous behaviour after the click rather than relying on users to catch every latest cybersecurity threat. Meanwhile, establish governance for GenAI tools across the organisation before shadow AI becomes your largest data leak surface.
| Finding | Value | Source |
|---|---|---|
| Orgs citing AI as primary cyber concern | 47% | WEF Global Cybersecurity Outlook 2025 |
| WEF: AI as #1 driver of cybersecurity change | 94% | WEF Global Cybersecurity Outlook 2026 |
| AI-enabled attack increase YoY (CrowdStrike 2026) | 89% | CrowdStrike 2026 Global Threat Report |
| AI used by attackers in breach campaigns | 16% | IBM Cost of a Data Breach Report 2025 |
| AI phishing as attack method | 37% | IBM Cost of a Data Breach Report 2025 |
| Deepfake as attack method | 35% | IBM Cost of a Data Breach Report 2025 |
| AI-generated phishing success rate vs human | 82.6% | Keepnet Labs / VIPRE Security Group |
| AI phishing click-through rate | 54% | Harvard Business Review / Heiding, Schneier et al. |
| AI phishing cost reduction vs manual | 95%+ | Harvard Business Review / Heiding, Schneier et al. |
| BEC emails that were AI-generated | 40% | VIPRE Security Group Q2 2024 |
| AI-crafted phishing share | 80%+ | Abnormal Security / Xceedance |
| Orgs seeing GenAI-related breaches | 97% | Capgemini Research Institute |
| Orgs experiencing AI attacks | 63% | Bitdefender 2025 Cybersecurity Assessment Report |
| GenAI share of cyberattacks by 2027 | 17% | Gartner |
| AI-enabled attack increase | 47% | SentinelOne |
| Workers using personal GenAI for work | 57% | Gartner Top Cybersecurity Trends 2026 |
| Workers entering sensitive data in unapproved GenAI | 33% | Gartner Top Cybersecurity Trends 2026 |
| Top AI concern: data leaks from GenAI | 34% | WEF Global Cybersecurity Outlook 2026 |
| Largest deepfake CFO scam | $25.6M | CrowdStrike 2025 Global Threat Report |
| Deepfake fraud increase | 3,000% | Onfido 2024 Identity Fraud Report |
| Deepfake fraud surge (2024) | 1,300% | Pindrop 2025 Voice Intelligence & Security Report |
The AI Controls Vacuum
Of companies that experienced AI-related security incidents, 97% lacked proper AI access controls. 13% of all companies reported such incidents in 2025.. 57% of workers use personal GenAI accounts for work, and 33% admit entering sensitive data into unapproved tools (Gartner 2026). The gap between AI adoption speed and security controls is the defining risk of 2026. (IBM)
🛡️ AI in Defence: The Security AI Arms Race
The trend: Organisations with extensive security AI and automation pay $3.62M per breach versus $5.52M without — a 34% reduction and $1.9M in savings (IBM 2025). Detection drops from 72 days to 51 days with extensive AI use. 77% of organisations have already adopted AI for cybersecurity purposes (WEF 2026). The defensive dividend from AI is measurable and growing.
The governance gap: But the picture is complicated. 13% of companies reported an AI-related security incident in 2025, and 97% of those affected lacked proper AI access controls (IBM). Approximately 33% of organisations still lack any process to assess the security of AI tools before deployment (WEF 2026). Gartner predicts that organisations prioritising AI Trust, Risk, and Security Management (AI TRiSM) will see 50% improvement in AI model breach containment by 2026. The challenge is not whether to deploy AI — it is deploying AI with governance.
AI-driven SOCs: Gartner identifies "AI-driven SOCs reshape operations and workforce" as one of its six top cybersecurity trends for 2026. AI-enabled SOCs enhance triage accuracy and speed, but introduce cost uncertainty, upskilling requirements, and workforce pressure. IBM X-Force recommends adopting agentic-powered threat detection and autonomous SOCs to match the machine-speed offence documented in CrowdStrike's 29-minute breakout data. The human-in-the-loop model remains essential — AI augments but does not replace human judgment.
What it means for you: The organisations winning the AI arms race are investing in both AI-powered defence tools and the governance frameworks to control them. This means AI security policies, approval workflows for GenAI tools, adversarial AI testing, and security teams with AI expertise. Gartner identifies the end of traditional security awareness training as a top trend — standard training fails amid unsanctioned GenAI tools. The replacement: adaptive, task-based programmes with AI-specific modules. Without governance, AI adoption creates as many vulnerabilities as it closes.
| Finding | Value | Source |
|---|---|---|
| Cost savings from security AI/automation | $1.9M | IBM Cost of a Data Breach Report 2025 |
| Breach cost reduction from security AI | 34% | IBM Cost of a Data Breach Report 2025 |
| Breach cost without AI/automation | $5.52M | IBM Cost of a Data Breach Report 2025 |
| Breach cost with extensive AI/automation | $3.62M | IBM Cost of a Data Breach Report 2025 |
| Security teams adopting AI tools | 77% | IBM Cost of a Data Breach Report 2025 |
| Security teams using AI tools | 75% | Cobalt |
| Orgs where AI demand outpaces capability | 57% | Cobalt |
| Companies reporting AI-related incident | 13% | IBM |
| AI incident victims lacking AI access controls | 97% | IBM |
| Orgs lacking AI access controls | 97% | IBM Cost of a Data Breach Report 2025 |
| Orgs with no AI governance framework | 63% | IBM Cost of a Data Breach Report 2025 |
| Orgs with no AI upload controls | 83% | IBM Cost of a Data Breach Report 2025 |
| AI breach containment improvement with AI TRiSM | 50% | Gartner |
| CISOs citing AI as biggest challenge | 53% | SentinelOne / Industry Reports |
AI Offence vs Defence: The Speed Gap
AI-generated phishing reduces attack costs by 95% and achieves click rates exceeding 50% (HBR 2024). Meanwhile, Organizations with extensive AI/automation save $1.9M per breach ($3.62M vs $5.52M without). The offensive advantage is clear: AI makes attacks cheaper and faster while defenders are still deploying AI tools. The organisations winning are those investing in both. (IBM Cost of a Data Breach Report 2025)
The Sophos perspective on AI: Sophos's Active Adversary Report 2026 offers a grounding assessment: there is no evidence that AI is creating new attack techniques. Instead, AI boosts phishing polish, payload customisation, and deepfake BEC at scale. It lowers barriers for mass exploitation of known vulnerabilities. Attackers still rely on fundamentals — compromised credentials, unpatched systems, and missing MFA. The implication for defenders is clear: AI-driven defence tools are essential for matching the speed and scale of AI-augmented offence, but they do not replace the foundational hygiene that prevents 90%+ of breaches (Unit 42 2026). The organisations with the best outcomes are those that combine AI-powered detection with basic security controls deployed universally.
Fortinet's defence framework: Fortinet recommends five pillars for machine-speed defence: Continuous Threat Exposure Management (CTEM) to identify and prioritise exposures before exploitation, MITRE ATT&CK mapping for detection coverage validation, AI-enabled detection and response workflows, identity management extended to both humans and machines, and network segmentation with zero trust enforcement. This framework directly addresses the 29-minute breakout window, the 82% malware-free detection challenge, and the 88% off-hours deployment pattern documented across the 2026 reports.
🔗 Supply Chain Attacks Are Multiplying
The trend: Third-party breaches doubled year-over-year to 30% of all incidents (Verizon DBIR 2025). IBM's X-Force Threat Intelligence Index 2026 confirms the trajectory: cloud-related intrusions via supply chain and third-party compromises have grown nearly 4x since 2020. Supply chain compromise costs $4.91M per breach on average, and large organisations identify supply chain risk as their greatest barrier to cyber resilience (WEF 2025). The SolarWinds and MOVEit attacks demonstrated the multiplication effect — one compromised vendor cascading to thousands of downstream victims.
The CI/CD identity chain threat: Mandiant/Google Cloud documented a new supply chain attack class in their H1 2026 Threat Horizons report: CI/CD identity chain abuse. In the UNC6426 campaign, PRC-nexus actors compromised a developer's GitHub token via a malicious NPM package, exploited the GitHub-to-AWS OIDC trust relationship, and created an admin role — achieving full cloud compromise in 72 hours. This pattern weaponises the trust relationships inherent in modern DevOps pipelines, making software supply chains an explicit APT target.
The multi-surface reality: Unit 42's Global Incident Response Report 2026 confirms the supply chain angle: 23% of intrusions involved third-party SaaS applications and integrations that bypassed traditional perimeter controls. 87% of all intrusions spanned multiple attack surfaces (endpoints, cloud, SaaS, identity). IBM X-Force 2026 reports that AI-introduced unvetted code in open-source ecosystems is creating new supply chain risk categories that did not exist two years ago.
The data: 55 new ransomware-as-a-service families emerged in 2024 (Travelers), many targeting managed service providers and software supply chains for maximum reach. Cybersecurity Ventures projects software supply chain attacks will cost $138 billion globally by 2031. In financial services, 41.8% of breaches at leading fintech companies traced back to third-party vendors (SecurityScorecard 2025). Verizon DBIR 2025 also found that 22% of breaches now involve edge device and VPN exploits — an approximately 8x rise — with attackers targeting the infrastructure designed to protect remote access.
What it means for you: Your security is only as strong as your weakest vendor. Continuous third-party risk monitoring, vendor security scorecards, and contractual security requirements are no longer optional. The emerging cybersecurity trend is "assumed breach" for supply chains — designing systems that limit blast radius when (not if) a vendor is compromised. For organisations with CI/CD pipelines, audit your OIDC trust relationships, rotate machine credentials every 90 days (Unit 42 recommendation), and implement SCA (Software Composition Analysis) for every dependency. Create "break-glass" plans for instant token revocation when a vendor compromise is detected.
| Finding | Value | Source |
|---|---|---|
| Breaches involving third parties | 30% | IBM Cost of a Data Breach Report 2025 |
| Verizon DBIR: third-party breaches doubled | 30% | Verizon DBIR 2025 |
| Average supply-chain breach cost | $4.91M | IBM Cost of a Data Breach Report 2025 |
| Supply chain/cloud compromises since 2020 | 4x | IBM X-Force Threat Intelligence Index 2026 |
| Large orgs: supply chain as greatest barrier to cyber resilience | 54% | WEF Global Cybersecurity Outlook 2025 |
| Global orgs projected impacted by supply chain attacks | 45% | WEF Global Cybersecurity Outlook 2025 |
| Supply chain attacks climbing | 42% | Purplesec / ENISA |
| CI/CD identity chain to full cloud compromise | 72 hours | Google Cloud Threat Horizons H1 2026 |
| Fintech breaches from third-party vendors | 41.8% | SecurityScorecard |
| Largest US banks suffering third-party breaches | 97% | KnowBe4 Financial Sector Threats Report 2025 |
| Projected supply chain attack cost by 2031 | $138B | Cybersecurity Ventures |
| New RaaS families identified (2024) | 55 | Travelers Insurance |
The Supply Chain Multiplication Effect
Supply chain breaches cost 1.1x the global average ($4.91M vs $4.44M). A single compromised vendor can cascade to thousands of downstream organisations. Third-party breaches doubled to 30% of all incidents in one year, and the projected global cost of software supply chain attacks will reach $138 billion by 2031 (Cybersecurity Ventures). (IBM Cost of a Data Breach Report 2025)
🎯 Ransomware Is Evolving, Not Declining
The trend: Ransomware appears in 44% of all data breaches, up from 32% the prior year (Verizon DBIR 2025). Attack volume surged 58% (HIPAA Journal). IBM's X-Force 2026 report tracked a 49% year-over-year increase in active ransomware groups, with 109 groups now operational — the highest count ever recorded. Sophos's Active Adversary Report 2026 observed 51 distinct ransomware brands, with Akira leading at 22% of incidents followed by Qilin. The fragmentation is deliberate: smaller groups using leaked tools and AI create a more distributed, harder-to-disrupt ecosystem.
The off-hours playbook: 88% of ransomware is deployed outside business hours (Sophos 2026). 79% of data exfiltration also occurs after hours. Attackers reach Active Directory in an average of 3.4 hours post-breach, giving them the keys to the kingdom before most SOC teams are fully staffed. Median dwell time has dropped to just 3 days (Sophos 2026) — attackers are faster and more purposeful. Data exfiltration was confirmed in approximately 50% of ransomware cases, with stolen data leaked publicly within 19.5 days on average.
The economics: The median ransom payment is $115,000, but the median demand is $1.32M — victims negotiate hard (Verizon/Sophos). Recovery costs dwarf the ransom itself at $2.73M mean recovery cost (Sophos 2025). 64% of organisations now refuse to pay, up from 41% two years ago (Verizon DBIR 2025). Yet 67% of those who did pay were attacked again within 12 months (Fortinet). The Verizon DBIR also found that 88% of SMB breaches included ransomware, compared to 39% for large organisations — making ransomware disproportionately an SMB problem.
The SMB ransomware crisis: The Verizon DBIR 2025 revealed a stark divide: 88% of SMB breaches included ransomware, compared to just 39% for large organisations. SMBs face a compounding disadvantage: they lack 24/7 SOC coverage (exploited by the 88% off-hours deployment pattern), often have insufficient log retention (Sophos reports missing logs doubled year-over-year, with some firewalls retaining only 7 days), and stolen credentials bypass patches entirely. Sophos recommends phishing-resistant MFA, reduced identity exposure, and managed detection and response (MDR) for constant visibility as minimum SMB defences.
Forensic destruction is now standard: Mandiant/Google reports that state-sponsored groups and ransomware gangs are routinely deleting logs, forensic artifacts, core dumps, and cloud snapshots. This practice serves two purposes: evading detection during the intrusion and hindering post-incident investigations. For defenders, this means traditional forensic approaches are insufficient. You need immutable log storage, cloud-native audit trails, and snapshot protections that attackers cannot reach.
What it means for you: The economics of ransomware still favour attackers, but defenders are gaining ground through better backups, refusal to pay, and law enforcement involvement. Your cybersecurity predictions for 2026 should assume ransomware volume will not decline. Invest in immutable backups, incident response planning, 24/7 monitoring coverage (particularly outside business hours), and ransomware-specific tabletop exercises. With attackers reaching AD in 3.4 hours, your detection-to-containment window is measured in minutes, not days.
| Finding | Value | Source |
|---|---|---|
| Ransomware present in breaches | 44% | Verizon DBIR 2025 |
| Increase in ransomware attacks (2025) | 58% | HIPAA Journal |
| Active ransomware groups tracked (+49% YoY) | 109 | IBM X-Force Threat Intelligence Index 2026 |
| Active ransomware brands observed (Sophos) | 51 | Sophos Active Adversary Report 2026 |
| Global ransomware damages (2025) | $57B | Cybersecurity Ventures |
| Projected ransomware damages by 2031 | $265B | Cybersecurity Ventures |
| Median ransom payment | $115,000 | Verizon DBIR 2025 |
| Median ransom demand | $1.32M | Sophos State of Ransomware 2025 |
| Organizations refusing to pay ransom | 64% | Verizon DBIR 2025 |
| Ransomware with data exfiltration | 87.6% | Travelers Insurance Claims Data |
| Ransomware deployed outside business hours | 88% | Sophos Active Adversary Report 2026 |
| Time to reach Active Directory post-breach | 3.4 hours | Sophos Active Adversary Report 2026 |
| Median attacker dwell time | 3 days | Sophos Active Adversary Report 2026 |
| Mean global recovery cost (2025) | $1.53M | Sophos State of Ransomware 2025 |
| Median recovery time from ransomware | 100+ days | Sophos State of Ransomware 2024 |
| Ransomware/extortion breach cost | $5.08M | IBM Cost of a Data Breach Report 2025 |
| Total crypto ransom payments (2024) | $813M | Chainalysis |
| Attacked again after paying ransom | 80% | Fortinet State of Ransomware 2024 |
| Ransomware in SMB breaches | 88% | Verizon DBIR 2025 |
| Largest single ransom payment (2024) | $75M | Mandiant M-Trends 2024 |
Ransomware Economics: Demand vs Payment vs Recovery
Median ransom demand: $1.32M. Median payment: $115K. Mean recovery cost (excluding ransom): $2.73M. The recovery cost is 23x the median payment, making the ransom itself a fraction of the true damage. 109 active groups (+49% YoY, IBM 2026), 51 brands (Sophos 2026), 88% deployed outside business hours. (Verizon DBIR 2025, Sophos 2026, IBM X-Force 2026)
⚡ The Shrinking Response Window
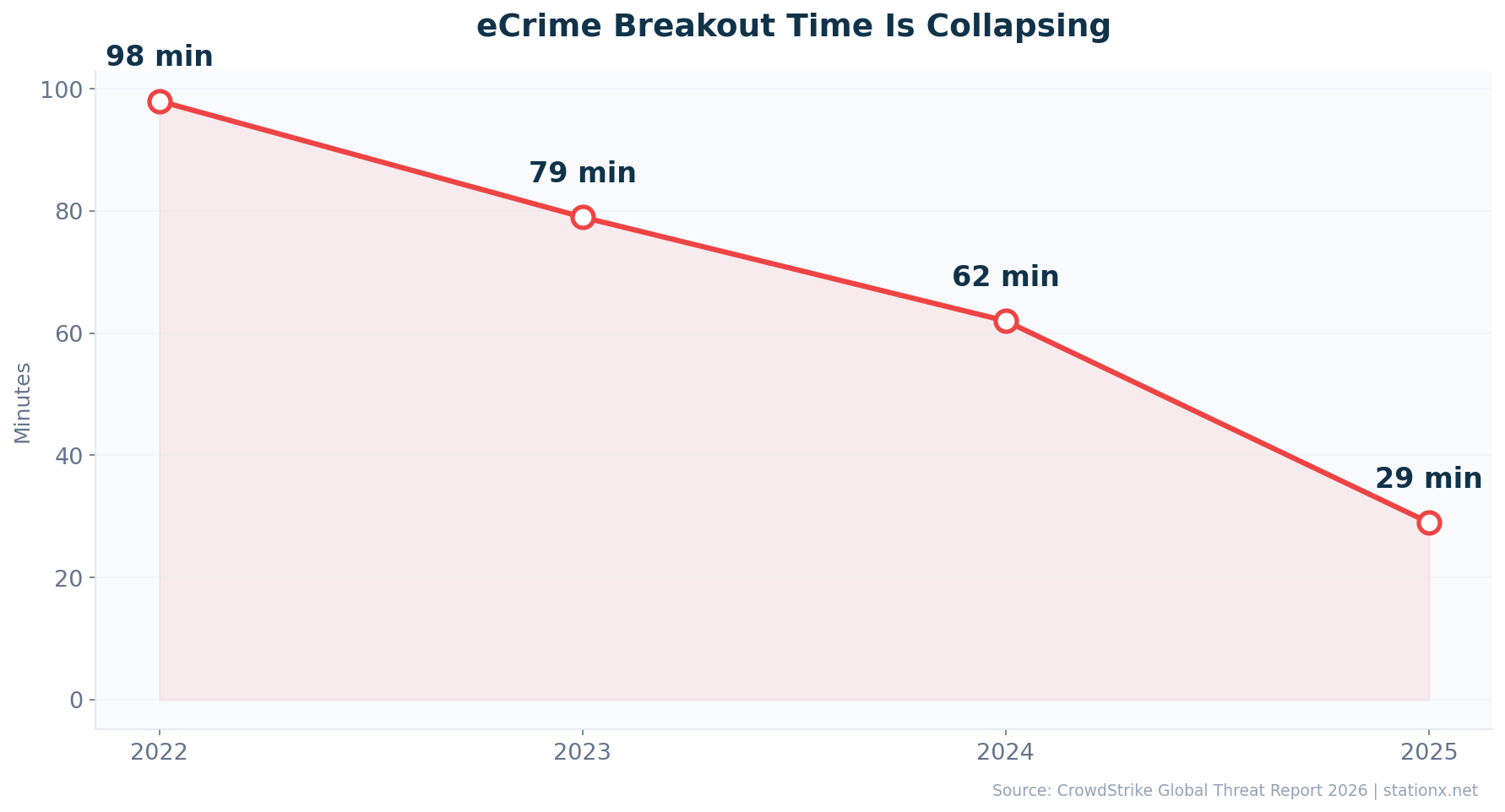
The trend: The time defenders have to detect and respond is collapsing. CrowdStrike's 2026 Global Threat Report documented an average eCrime breakout time of 29 minutes — 65% faster than 2024. The fastest observed breakout was 27 seconds. In one case, data exfiltration began within 4 minutes of initial access. This speed is the new evasion technique: attackers move too fast for traditional detect-and-respond models to engage.
Zero-day windows collapsing: Mandiant/Google documented threat actors deploying crypto miners within 48 hours of vulnerability disclosure in the React2Shell incident. CrowdStrike recorded a 42% increase in zero-day exploitation before public disclosure. IBM X-Force 2026 found that vulnerability exploitation now accounts for 40% of all incidents — overtaking phishing as the top attack vector for the first time. Attacks on public-facing applications surged 44% year-over-year (IBM). Many exploited vulnerabilities require no authentication, enabling direct scan-to-impact attack paths.
The AD timeline: Once inside, attackers reach Active Directory in an average of 3.4 hours (Sophos 2026). From AD compromise, they can deploy ransomware, exfiltrate data, and move laterally across the entire environment. The median dwell time has compressed to 3 days (Sophos 2026), but the critical damage often occurs in the first few hours. 88% of ransomware is deployed outside business hours (Sophos), exploiting the gap in 24/7 monitoring coverage — particularly at SMBs.
Exfiltration speed acceleration: Unit 42's Global Incident Response Report 2026 provides additional velocity data: the fastest 25% of exfiltration events now complete in just 1.2 hours (down from 4.8 hours — a 4x acceleration). The overall median exfiltration time is 72 minutes, down from approximately 5 hours. In Unit 42's own AI-simulated attack testing, a complete attack chain executed in 25 minutes. Fortinet's assessment is blunt: breach-to-impact timelines have compressed from days to minutes. The implication is that by the time a human analyst has triaged the initial alert, the data may already be exfiltrated.
Social engineering accelerating: CrowdStrike documented a 563% rise in fake CAPTCHA lures and a 141% increase in spam-based initial access vectors. These low-sophistication but high-volume techniques are designed to overwhelm defences with speed and scale rather than technical complexity. Sophos notes that brute-force attacks now account for 15.6% of initial access, nearly matching vulnerability exploitation at 16% — confirming that the simplest attacks remain effective when basic controls are missing.
What it means for you: Your detection and response capability must operate at machine speed. A 29-minute breakout window leaves no room for manual triage. Automated detection, pre-planned containment playbooks, and 24/7 monitoring coverage are prerequisites. Organisations without these capabilities are operating with an open window — the attacker will be through it before your team is alerted. Prioritise automated response for the first 15 minutes: network isolation, credential revocation, and snapshot preservation. Over 90% of breaches stemmed from preventable gaps (Unit 42) — misconfigurations, excessive identity trust, and unpatched systems — meaning basic hygiene remains the highest-impact defence even against machine-speed offence.
| Finding | Value | Source |
|---|---|---|
| Avg eCrime breakout time (CrowdStrike 2026) | 29 minutes | CrowdStrike 2026 Global Threat Report |
| Fastest observed breakout time | 27 seconds | CrowdStrike 2026 Global Threat Report |
| Previous year breakout time (2025 report) | 48 minutes | CrowdStrike 2025 Global Threat Report |
| Zero-day exploitation window (Mandiant) | 48 hours | Google Cloud Threat Horizons H1 2026 |
| Time to Active Directory post-breach | 3.4 hours | Sophos Active Adversary Report 2026 |
| Median attacker dwell time (Sophos) | 3 days | Sophos Active Adversary Report 2026 |
| Ransomware deployed outside business hours | 88% | Sophos Active Adversary Report 2026 |
| Increase in zero-day exploitation before disclosure | 42% | CrowdStrike 2026 Global Threat Report |
| Vulnerability exploitation as top attack vector (IBM 2026) | 40% | IBM X-Force Threat Intelligence Index 2026 |
The Speed Timeline: From Disclosure to Devastation
Zero-day exploit: 48 hours after disclosure (Mandiant). Initial breakout: 29 minutes average, 27 seconds fastest (CrowdStrike 2026). Data exfiltration: 72 minutes median, 1.2 hours for fastest 25% (Unit 42). Active Directory compromise: 3.4 hours (Sophos). Ransomware deployment: outside business hours 88% of the time (Sophos). The entire kill chain from disclosure to domain compromise can now complete in under 4 hours. If your incident response plan assumes next-business-day action, it is already obsolete.
Rapid Response Readiness Checklist
With a 29-minute average breakout window, defenders must automate the first 15 minutes. Based on recommendations from CrowdStrike, Sophos, Mandiant, and Unit 42:
- Automated network isolation — pre-configured playbooks to isolate compromised endpoints within seconds of detection
- Instant credential revocation — break-glass procedures for disabling compromised accounts and revoking tokens
- Immutable log storage — out-of-band log retention that attackers cannot delete (countering forensic destruction)
- 24/7 monitoring coverage — 88% of ransomware deploys outside business hours; SOC coverage gaps are attack windows
- Snapshot preservation — automated cloud snapshot protections that cannot be overridden by compromised admin accounts
- Patch within 48 hours for critical CVEs — zero-day exploitation windows have collapsed to 48 hours (Mandiant)
- AD hardening — reduce blast radius for the 3.4-hour AD compromise timeline; tier administration, restrict NTLM
🔑 Identity-First Security Replaces Perimeter Defence
The trend: Attackers are no longer hacking in — they are logging in. Identity-based attacks surged 75% year-over-year (CrowdStrike 2025). CrowdStrike's 2026 report pushes the picture further: 82% of all detections are now malware-free, relying on valid credentials, trusted identity flows, and approved SaaS integrations. Sophos's Active Adversary Report 2026 confirms identity as the dominant vector: 67% of all investigated incidents started with compromised credentials, weak MFA, or phishing. The network perimeter is irrelevant when the attacker has valid credentials.
The MFA gap: MFA was present in only 41% of cases investigated by Sophos (2026). This is a staggering gap for a control that is universally recommended. Microsoft processes 600 million+ password attacks per day. Infostealer malware surged in 2024 (KnowBe4), harvesting credentials at scale. Verizon DBIR 2025 found that 54% of ransomware victims had prior exposures in infostealer logs, with 40% involving corporate email credentials. 46% of infostealer-compromised systems with corporate logins were non-managed BYOD devices — outside the reach of corporate endpoint security entirely.
Cross-domain identity movement: CrowdStrike's 2026 report highlights a shift to cross-domain movement via identity rather than malware. Attackers traverse trusted identities, SaaS applications, and cloud infrastructure without deploying a single malicious binary. Valid account abuse caused 35% of cloud incidents (CrowdStrike 2025). Gartner identifies "IAM evolving beyond humans" as one of its six top cybersecurity trends for 2026: machine identities and AI agents now require registration, credential automation, and policy-based authorisation as a control plane.
What it means for you: Identity is the new perimeter. Phishing-resistant MFA (FIDO2/passkeys) is no longer a nice-to-have — and standard MFA is insufficient, with prompt-bombing bypasses appearing in 14% of Verizon DBIR incidents. Credential monitoring, privileged access management, and zero-trust identity verification must be your baseline. Extend IAM to machine identities: service accounts, API keys, and AI agents need the same governance as human users. The cyber security trends are clear: organisations treating identity as a control plane rather than a perimeter feature will be materially more resilient.
| Finding | Value | Source |
|---|---|---|
| YoY increase in identity-based attacks | 75% | CrowdStrike 2025 Global Threat Report |
| Incidents starting with identity compromise (Sophos 2026) | 67% | Sophos Active Adversary Report 2026 |
| Detections that were malware-free (CrowdStrike 2026) | 82% | CrowdStrike 2026 Global Threat Report |
| Breaches via stolen credentials | 53% | Verizon DBIR 2025 |
| Credential compromise share of breaches | 31% | Verizon DBIR 2024 |
| Attacks that are malware-free | 79% | CrowdStrike 2025 Global Threat Report |
| eCrime breakout time (2025) | 48 minutes | CrowdStrike 2025 Global Threat Report |
| eCrime breakout time (2026 report: 29 min avg) | 29 minutes | CrowdStrike 2026 Global Threat Report |
| MFA present in investigated cases (Sophos) | 41% | Sophos Active Adversary Report 2026 |
| Enterprise MFA adoption rate | 41% | Microsoft Digital Defense Report 2024 |
| Orgs without phishing-resistant MFA | 76% | Arctic Wolf Threat Report 2025 |
| Monthly credential stuffing attacks | 26 billion | Akamai |
| Infostealer malware increase (2024) | 58% | KnowBe4 Financial Sector Threats Report 2025 |
| Infostealer credentials harvested (H1 2025) | 1.8 billion | SpyCloud |
| Identity-based phishing incidents | 60% | Cisco Cybersecurity Readiness Index 2025 |
| Password attacks per day | 600 million+ | Microsoft Digital Defense Report 2024 |
| Breach cost reduction with zero trust | $1.76M | IBM / UpGuard |
| Leaked authentication cookies | 94 billion | NordVPN Research |
From Hacking In to Logging In
82% of detections are malware-free (CrowdStrike 2026). 67% of incidents start with identity compromise (Sophos 2026). MFA present in only 41% of investigated cases (Sophos). Nearly 90% of Unit 42 cases involved identity weaknesses. 600M+ password attacks per day (Microsoft). The shift from malware-based to identity-based attacks is the most significant tactical evolution in cybersecurity. Traditional endpoint security catches less than a quarter of modern attacks. The defence shift must be equally fundamental: from detecting malware to detecting anomalous identity behaviour.
Identity Attack Prevention Checklist
Based on convergent recommendations from CrowdStrike, Sophos, Verizon, and Unit 42:
- Deploy phishing-resistant MFA universally — FIDO2/passkeys, not SMS or push-only (MFA present in only 41% of Sophos cases)
- Rotate machine identity credentials every 90 days — service accounts, API keys, AI agent tokens (Unit 42 recommendation)
- Monitor for infostealer credential exposure — 54% of ransomware victims had prior infostealer log exposure (Verizon DBIR)
- Extend IAM to non-human identities — machine identities outnumber humans; govern them equally (Gartner 2026 trend)
- Implement ITDR alongside endpoint security — Identity Threat Detection and Response catches the 82% that traditional EDR misses
- Audit BYOD credential exposure — 46% of corporate credential leaks come from non-managed devices (Verizon DBIR)
☁️ Cloud Security Gaps Persist
The trend: Cloud-conscious intrusions rose 37% overall in CrowdStrike's 2026 Global Threat Report, with a staggering 266% surge from state-nexus actors conducting intelligence collection operations. IBM X-Force 2026 recorded a 44% increase in attacks on public-facing applications. Gartner projects that 99% of cloud security failures through 2025 will be the customer's fault, not the provider's. Multi-cloud adoption continues to rise, creating exponential complexity in security management.
State-nexus cloud targeting: The 266% increase in state-nexus cloud intrusions (CrowdStrike 2026) represents a qualitative shift. China-nexus groups increased overall intrusions by 38%, with 67% of exploited vulnerabilities granting immediate access and 40% targeting edge devices (VPNs, firewalls) for long-term espionage. DPRK-nexus incidents surged 130%, including the $1.46 billion cryptocurrency theft — the largest single crypto heist in history (CrowdStrike 2026). Russia's FANCY BEAR deployed LLM-enabled LAMEHUG malware for automated reconnaissance. Cloud environments are the new theatre for geopolitical cyber operations.
The data: Hybrid cloud breach costs hit $4.97M, and organisations with breaches spanning multiple environments face the highest costs at $5M+ (IBM 2025). Kubernetes security incidents affected the majority of container-running organisations (Red Hat 2024), with misconfiguration as the primary cause. Mandiant documented full cloud compromise via CI/CD identity chain abuse in 72 hours — exploiting trust relationships between GitHub, NPM, and AWS. IBM X-Force confirms supply chain and cloud compromises have grown nearly 4x since 2020.
What it means for you: Cloud security is a shared responsibility, and 99% of the failures are on your side. The 266% increase from state-nexus actors means cloud environments face both criminal and espionage threats simultaneously. Continuous monitoring, CSPM/CNAPP tooling, and cloud-native identity controls are the minimum. Multi-cloud environments demand unified security posture management. Audit CI/CD trust relationships, enforce least-privilege on machine identities, and implement break-glass token revocation procedures.
| Finding | Value | Source |
|---|---|---|
| Cloud intrusion increase +37% (CrowdStrike 2026) | 37% | CrowdStrike 2026 Global Threat Report |
| Cloud intrusions from state-nexus actors +266% | 266% | CrowdStrike 2026 Global Threat Report |
| Cloud intrusion increase (2024) | 26% | CrowdStrike 2025 Global Threat Report |
| Cloud incidents from credential abuse | 35% | CrowdStrike 2025 Global Threat Report |
| Attacks on public-facing apps +44% (IBM 2026) | 44% | IBM X-Force Threat Intelligence Index 2026 |
| Cloud security failures: customer fault | 99% | Gartner |
| Cloud misconfiguration incidents | 27% | SentinelOne |
| Cloud failures from human error | 95% | SentinelOne / Industry Reports |
| Multi-cloud adoption rate | 78% | Fortinet / Cybersecurity Insiders 2024 Cloud Security Report |
| Multi-cloud operations (2026) | 88% | SentinelOne / Industry Reports |
| Hybrid cloud breach cost | $3.8M | IBM / UpGuard |
| On-premises breach cost | $4.01M | IBM Cost of a Data Breach Report 2025 |
| Multiple environment breach cost | $5.05M | IBM Cost of a Data Breach Report 2025 |
| Cloud breaches from credentials | 82% | Thales Group 2023 Cloud Security Study |
| Cloud breaches from misconfiguration | 15% | Verizon DBIR 2023 |
| CI/CD chain to full cloud compromise (Mandiant) | 72 hours | Google Cloud Threat Horizons H1 2026 |
| Kubernetes security incidents | 90% | Red Hat |
| K8s incidents from misconfiguration | 45% | Red Hat |
| Cloud credential incidents | 35% | CrowdStrike 2025 Global Threat Report |
Cloud Is Now a Geopolitical Battleground
Cloud-conscious intrusions rose 37% overall and 266% from state-nexus actors (CrowdStrike 2026). Mandiant documented full cloud compromise via CI/CD identity chain abuse in 72 hours. IBM X-Force confirms supply chain/cloud compromises have grown nearly 4x since 2020. Attacks on public-facing applications surged 44% (IBM 2026). 48% of Unit 42 intrusions targeted browsers via routine cloud/SaaS access. Cloud security is no longer just a misconfiguration problem — it is a target for nation-state intelligence collection, criminal extortion, and supply chain weaponisation simultaneously. (CrowdStrike 2026, IBM X-Force 2026, Mandiant 2026, Unit 42 2026)
Cloud Defence Priorities for 2026
Based on convergent recommendations from CrowdStrike, Mandiant, IBM, and Fortinet:
- Audit CI/CD trust relationships — review all OIDC, OAuth, and federated identity trusts between code repos, build systems, and cloud providers
- Enforce least-privilege on machine identities — service accounts and workload identities should have narrowly scoped permissions
- Implement CSPM/CNAPP — continuous cloud security posture management catches misconfigurations before attackers do
- Unified multi-cloud monitoring — single-pane visibility across AWS, Azure, GCP, and SaaS environments
- Break-glass token revocation — instant capability to revoke all tokens when a compromise is detected (Unit 42 recommendation)
- Network segmentation for cloud workloads — micro-segmentation limits lateral movement from compromised instances
📜 Regulatory Tsunami: NIS2, DORA, EU AI Act
The trend: Three major regulatory frameworks converged within 18 months: NIS2 (October 2024), DORA (January 2025), and the EU AI Act (phased 2024-2026). This is unprecedented regulatory density. 162 countries now have comprehensive data protection laws (Greenleaf 2025), and cumulative GDPR fines have exceeded €7.1 billion (DLA Piper 2026). GDPR enforcement hit a record €2.1 billion in fines during 2025 alone, signalling an aggressive enforcement posture.
Executive liability is real: Both NIS2 and DORA place direct responsibility on management bodies. Personal liability for executives now extends beyond organisational fines. Cybersecurity has transformed from a technical concern to a board-level governance issue. Gartner identifies "regulatory accountability as executive liability" as one of its six top cybersecurity trends for 2026: regulatory decentralisation elevates cyber resilience to board-level accountability, requiring integration with legal, procurement, and business decisions. 91% of the largest organisations have already altered cybersecurity strategies due to geopolitical volatility (WEF 2026).
The DORA timeline pressure: DORA's 4-hour initial incident notification requirement for major incidents (versus NIS2's 24-hour window) makes manual compliance processes impossible. Automated monitoring tools, SIEM/SOAR systems, and continuous penetration testing have shifted from optional to mandatory. Overlapping reporting obligations mean a single breach can trigger simultaneous reporting under DORA, GDPR, and national frameworks with different formats and deadlines. CISOs increasingly cite regulatory fragmentation as a top challenge (WEF 2025).
The data: The cost of compliance failure adds significant expense to breaches (IBM 2025). Shadow AI governance gaps expose organisations to data compromise: organisations without AI upload controls or governance frameworks face higher breach costs. Privacy spending delivers positive ROI at 1.6x+ returns (Cisco 2025). The EU AI Act's prohibited practices are already enforceable (February 2026), general-purpose AI model requirements apply from May 2026, and high-risk AI system requirements from August 2026.
What it means for you: If you operate in the EU or serve EU customers, you are now subject to a layered regulatory regime that covers network security (NIS2), operational resilience (DORA), and AI governance (EU AI Act) simultaneously. This is not just a compliance exercise — it is a structural shift in how security teams must operate. Board-level accountability for cybersecurity is now mandatory under NIS2, with personal executive liability. DORA's 4-hour reporting deadline demands automated incident detection and response capabilities. Treat compliance as a security enabler and invest in the tooling to meet overlapping obligations.
| Finding | Value | Source |
|---|---|---|
| Cumulative GDPR fines (2026) | €7.1B | DLA Piper GDPR Fines and Data Breach Survey 2026 |
| Cumulative GDPR fines (2025) | €5.88B | DLA Piper GDPR Fines and Data Breach Survey 2025 |
| GDPR breach notifications increase | 22% | DLA Piper GDPR Fines Survey 2026 |
| Countries with data protection laws | 162 | Greenleaf (2025) |
| Compliance failure added breach cost | $1.22M | IBM Cost of a Data Breach Report 2025 |
| CISOs citing regulatory fragmentation | 76% | WEF Global Cybersecurity Outlook 2025 |
| Breached orgs that paid regulatory fines | 32% | IBM Cost of a Data Breach Report 2025 |
| Regulatory fines exceeding $250K | 25% | IBM Cost of a Data Breach Report 2025 |
| Privacy spending ROI | 96% | Cisco 2025 Data Privacy Benchmark Study |
| Shadow AI breach cost | $4.63M | IBM Cost of a Data Breach Report 2025 |
| Orgs requiring AI approval | 45% | IBM Cost of a Data Breach Report 2025 |
| Orgs testing for adversarial AI | 22% | IBM Cost of a Data Breach Report 2025 |
Regulatory Convergence: Three Frameworks, 18 Months
NIS2 (Oct 2024), DORA (Jan 2025), and EU AI Act (phased 2024-2026) created an unprecedented regulatory convergence, requiring simultaneous compliance across 162 countries with data protection laws. For organisations operating across multiple jurisdictions, a single breach can trigger compliance obligations under 5-10 regulatory frameworks simultaneously. The cost of non-compliance now exceeds the cost of compliance. (Greenleaf (2025), DLA Piper GDPR Fines and Data Breach Survey 2026)
Regulatory Timeline: Key Compliance Deadlines
Click each milestone to see details about the regulation and its impact.
NIS2 Directive
Oct 2024 — Enforcement deadline
DORA
Jan 2025 — Enforcement deadline
EU AI Act — Phase 1
Feb 2025 — Prohibited AI practices
EU AI Act — Phase 2
Aug 2025 — General-purpose AI models
EU AI Act — Phase 3
Aug 2026 — High-risk AI systems
🌐 Zero Trust Goes Mainstream
The trend: Zero trust adoption is projected to grow from 41% of enterprises (2025) to 63% in 2026 (IBM/VikingCloud, Gartner). Zero trust reduces breach costs by $1.76M on average (IBM 2025). ZTNA (Zero Trust Network Access) is replacing traditional VPNs as the default remote access architecture. The conversation has shifted from "should we adopt zero trust" to "how quickly can we implement it."
Why zero trust is critical now: The 2026 threat data makes the case for zero trust more compelling than ever. CrowdStrike's 29-minute average breakout time (down from 48 minutes) means traditional perimeter controls cannot react fast enough. 82% of detections are malware-free, rendering signature-based controls obsolete. 67% of incidents start with identity compromise (Sophos 2026). Zero trust's assume-breach posture — continuous verification, least privilege, micro-segmentation — directly addresses both the speed gap and the identity-first attack model. Breaches resolved within 200 days cost substantially less than those taking longer (IBM 2025).
IAM beyond humans: Gartner identifies "IAM evolves beyond humans" as one of its six top cybersecurity trends for 2026. Machine identities and AI agents now outnumber human identities in most enterprise environments. These non-human identities require registration, credential automation, and policy-based authorisation as a control plane — the same zero trust principles applied to human users. Without extending zero trust to machines, you protect the front door while leaving the service entrance open.
What it means for you: Zero trust is no longer a buzzword — it is a measurable cost-reduction strategy. The $1.76M savings per breach makes the ROI calculation straightforward. Start with identity (phishing-resistant MFA, PAM), extend IAM to machine identities and AI agents, then layer on network segmentation and continuous monitoring. Full implementation takes 18-36 months, but every step delivers incremental value. With 88% of ransomware deployed outside business hours (Sophos), zero trust's continuous verification model closes the gap that attackers exploit when human monitoring drops.
Resilience over prevention: Both WEF and Gartner identify the strategic shift from prevention to resilience as a defining characteristic of 2026. Prevention alone cannot stop 82% malware-free attacks, 29-minute breakout times, or 48-hour zero-day exploitation windows. The resilient organisation assumes breach, limits blast radius through micro-segmentation, maintains continuous monitoring for anomalous behaviour, and can recover critical operations rapidly. Gartner predicts that by 2028, products lacking preemptive cybersecurity capabilities (AI, automation, deception) will lose market relevance. The investment case for zero trust is therefore not just about cost reduction but about organisational survival in an environment where prevention-only strategies are mathematically insufficient.
| Finding | Value | Source |
|---|---|---|
| Zero trust adoption (2025) | 41% | IBM / VikingCloud |
| Zero trust adoption projected (2026) | 63% | Gartner |
| Breach cost reduction with zero trust | $1.76M | IBM / UpGuard |
| Breaches via stolen credentials | 53% | Verizon DBIR 2025 |
| Attacks that are malware-free | 79% | CrowdStrike 2025 Global Threat Report |
| Breach cost when lifecycle > 200 days | $5.01M | IBM Cost of a Data Breach Report 2025 |
| Breach cost with fast resolution | $3.87M | IBM Cost of a Data Breach Report 2025 |
| eCrime breakout time | 48 minutes | CrowdStrike 2025 Global Threat Report |
Zero Trust: Adoption vs Implementation
Zero trust adoption is projected to grow from 41% (2025) to 63% (2026), a 22pp increase in one year. But adoption does not equal full implementation. Many organisations have adopted the framework in principle while still running legacy perimeter-based controls alongside it. The cost data is unambiguous: zero trust reduces breach costs by $1.76M (IBM 2025). (IBM / VikingCloud, Gartner)
Trend Impact Assessment: Which Trends Affect Your Organisation Most?
Rate each trend's impact on your organisation from 1 (low) to 5 (critical). Your personalised risk profile will update in real time.
Your Risk Profile
Moderate
Adjust the sliders above to see your personalised assessment.
🏭 OT/ICS Security Becomes a National Priority
The trend: The convergence of IT and OT networks has turned critical infrastructure into a primary attack target. 619 ICS vulnerabilities were disclosed in H2 2024 (Nozomi), and OT ransomware surged 46% (Nozomi 2025). Gartner predicts 75% of CISOs will be responsible for OT and cyber-physical systems security by 2027. The Colonial Pipeline attack in 2021 was the wake-up call; government mandates are the response.
The data: Critical infrastructure breaches cost $4.82M on average (IBM 2025). IBM X-Force 2026 found that manufacturing takes 27.7% of all cyber incidents — more than any other sector — with data theft as the primary motive. Manufacturing was the top ransomware target in 2024 (Group-IB), driven by operational downtime pressure. Utilities saw significant ransomware increases (DeepStrike 2025). In healthcare, 99% of organisations have at least one device with known exploited vulnerabilities (Claroty 2025). Unmanaged devices remain a primary ransomware entry point (Microsoft 2024).
Edge device targeting: CrowdStrike's 2026 report found that 40% of exploited vulnerabilities in China-nexus operations targeted edge devices — VPNs, firewalls, and routers — for long-term espionage. Mandiant documented PRC-nexus groups (UNC6201, UNC6426) specifically exploiting edge devices for persistent access. Fortinet identifies IT/OT convergence as expanding the lateral movement risk surface, particularly in energy and transport sectors. The combination of edge device exploitation and IT/OT convergence creates a direct path from internet-facing infrastructure to physical control systems.
What it means for you: If your organisation operates OT systems (manufacturing, energy, healthcare, utilities, transport), OT security is no longer an IT-adjacent concern — it is a board-level priority with regulatory obligations under NIS2. Asset visibility, network segmentation between IT and OT, and ICS-specific monitoring are the minimum requirements. The 27.7% manufacturing incident share (IBM) and edge device targeting (CrowdStrike, Mandiant) demand immediate attention to device firmware, patch management, and network segmentation.
| Finding | Value | Source |
|---|---|---|
| ICS vulnerabilities (H2 2024) | 619 | Nozomi Networks OT/IoT Security Report 2025 |
| OT ransomware surge | 46% | Nozomi Networks |
| ICS ransomware increase (Q2 2024) | 20% | Kaspersky ICS CERT |
| Critical infrastructure breach cost | $4.82M | IBM Cost of a Data Breach Report 2025 |
| Critical infra ransomware rate | 28% | Verizon DBIR 2025 |
| CISOs responsible for OT/CPS by 2027 | 75% | Gartner |
| Ransomware from unmanaged devices | 90%+ | Microsoft Digital Defense Report 2024 |
| Healthcare orgs with vulnerable devices | 99% | Claroty State of CPS Security: Healthcare 2025 |
| Utilities ransomware increase | 42% | Fortinet / DeepStrike |
| Manufacturing ransomware | 1,466 | Industrial Cyber |
| Manufacturing: top ransomware target | 660 attacks | Group-IB |
| Router vulnerabilities discovered | 50%+ | Forescout Riskiest Connected Devices 2025 |
The IT-OT Convergence Risk
Critical infrastructure breaches cost $4.82M (IBM 2025), OT ransomware surged 46% (Nozomi 2025), and 75% of CISOs will own OT security by 2027 (Gartner). Manufacturing takes 27.7% of all cyber incidents (IBM X-Force 2026). 13% of incidents involved end-of-life Windows Servers (Sophos 2026). The convergence of IT and OT networks means that an IT-side phishing email can now cascade into physical-world consequences. Edge device exploitation for espionage (40% of China-nexus operations, CrowdStrike 2026) creates a direct path from internet-facing infrastructure to physical control systems. Segmentation is not optional.
End-of-life risk: Sophos's Active Adversary Report 2026 found that 13% of incidents involved end-of-life Windows Servers — systems no longer receiving security patches. In OT/ICS environments, legacy systems are particularly prevalent due to long operational lifecycles and upgrade complexity. The combination of unpatched systems, IT/OT convergence, and the 29-minute breakout speed creates a high-risk environment where a single vulnerability disclosure can lead to physical-world impact within hours. North America accounts for 29% of all attacks (IBM X-Force 2026), with manufacturing consistently the top-targeted sector.
🧬 Quantum Computing Threat Timeline
The trend: Quantum computing capable of breaking RSA-2048 and ECC encryption is not here yet, but the threat perception is accelerating. 37% of respondents in the WEF Global Cybersecurity Outlook 2026 believe quantum will affect cybersecurity within 12 months — a surprisingly near-term concern. Nation-state actors are executing "harvest now, decrypt later" campaigns — stealing encrypted data today with the intent to decrypt it when quantum capability arrives. NIST finalized three post-quantum cryptography (PQC) standards in August 2024 (FIPS 203-205), and a fourth algorithm (HQC) was selected in March 2025. The migration clock is running.
The timeline: The Global Risk Institute estimates a 33% probability of quantum computers breaking RSA-2048 by 2034. NIST and global vendors recommend classical cryptography deprecation by 2030. The NSA's CNSA 2.0 mandates pure PQC for national security systems by 2035 — no classical algorithms permitted. As of January 2026, CISA federal buying guidance already requires quantum-resistant products in available categories. The migration to PQC is estimated to cost $7.1 billion for large enterprises (McKinsey).
Post-quantum cryptography in practice: Gartner identifies post-quantum cryptography as one of its six top cybersecurity trends for 2026, recommending that organisations move PQC to active migration roadmaps now. The practical steps are: inventory all cryptographic assets, identify dependencies on RSA, ECC, and Diffie-Hellman, and build cryptographic agility — the ability to swap algorithms without rebuilding systems. Hybrid approaches (classical plus PQC) are permitted during transition, but pure PQC will be mandated.
What it means for you: The timeline is long (5-10 years for meaningful quantum threat) but the migration is complex and regulators are moving now. Start with a cryptographic inventory: identify where you use RSA, ECC, and Diffie-Hellman. Prioritise systems handling data with long-term sensitivity (healthcare records, financial data, government secrets). CISA's January 2026 procurement guidance signals that quantum readiness is becoming a buying criterion. The organisations starting PQC migration now will avoid the scramble. Those waiting will face a compressed, expensive, and risky transition.
| Finding | Value | Source |
|---|---|---|
| NIST post-quantum standards finalized (2024) | 3 algorithms | NIST |
| Probability of breaking RSA-2048 by 2034 | 33% | Global Risk Institute |
| Post-quantum migration cost for large enterprises | $7.1B | McKinsey / Industry Estimates |
| Expect quantum to affect cybersecurity within 12 months (WEF) | 37% | WEF Global Cybersecurity Outlook 2026 |
Harvest Now, Decrypt Later: The Active Quantum Threat
37% of WEF respondents expect quantum to affect cybersecurity within 12 months. The quantum threat is active today despite quantum computers not yet being capable of breaking current encryption. Nation-state actors are stockpiling encrypted data for future decryption. NIST has finalised 3 PQC standards (FIPS 203-205) with a fourth (HQC) selected. Classical cryptography deprecation targeted for 2030. Pure PQC mandated for national security systems by 2035 (CNSA 2.0). CISA procurement guidance already requires PQC products (January 2026). If your data has sensitivity beyond 10 years (healthcare, government, finance), the migration is already late. (NIST 2024, WEF 2026, Global Risk Institute, Gartner 2026)
Post-Quantum Migration Roadmap
Based on NIST guidance, Gartner recommendations, and CISA procurement requirements:
- Step 1: Cryptographic inventory — identify all systems using RSA, ECC, and Diffie-Hellman across your environment
- Step 2: Data sensitivity classification — prioritise systems handling data with long-term sensitivity (healthcare records, financial data, government secrets)
- Step 3: Build cryptographic agility — architect systems to swap algorithms without full rebuilds; use modular crypto libraries
- Step 4: Implement hybrid mode — deploy classical + PQC key establishment in parallel during transition
- Step 5: Align with NIST standards — adopt FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), FIPS 205 (SLH-DSA) as target algorithms
- Step 6: Procurement alignment — require PQC-capable products in new purchases (following CISA January 2026 guidance)
Target: Classical cryptography deprecation by 2030 (NIST). Pure PQC required for NSS by 2035 (CNSA 2.0).
👥 The Workforce Crisis Deepens
The trend: The global cybersecurity workforce gap exceeds 4.8 million unfilled positions (ISC2 2024). 67% of organisations report a moderate-to-critical skills gap (WEF 2025). The top skill gap is AI security (ISC2 2025), followed by cloud security. Burnout rates in cybersecurity exceed other technology fields, and retention difficulty is a top concern for hiring managers (ISACA 2024).
The data: Organisations with the most severe skills shortages pay a breach cost premium of 17.6% ($5.22M vs $4.44M average, IBM 2025). 87% of organisations attribute at least one breach to the skills deficit (Fortinet 2025). AI is both the problem and the solution: it is the #1 skill gap AND the #1 tool for compensating for the people shortage through automation.
The CISO remit expands: Gartner predicts that by 2028, 50% of CISOs will own disaster recovery alongside incident response — a structural expansion of the CISO role from prevention and detection to full operational resilience. By end of 2026, 64% of employees will be fully remote or hybrid (up from 52% in 2021, Gartner), expanding the identity and endpoint attack surface that security teams must manage. The WEF identifies a growing gap between highly resilient organisations and those falling behind, with skills shortages and resource constraints amplifying systemic risk.
Cyber inequity: The WEF Global Cybersecurity Outlook 2026 documents a stark divergence in global cyber readiness. 84% of respondents in the Middle East and North Africa express confidence in their national cyber preparedness, versus just 13% in Latin America and the Caribbean — a 71-percentage-point gap. 31% of all respondents report low confidence in national cyber incident response, up from 26% the prior year. This inequity means that the global attack surface has weak links that affect everyone through interconnected supply chains and shared infrastructure.
The managed services response: Gartner's spending data reveals how the market is responding to the workforce gap. Security services spending reached $86.1 billion in 2025, making it the fastest-growing segment. Managed detection and response (MDR) services address the core gaps that the workforce shortage creates: 24/7 monitoring coverage (countering the 88% off-hours ransomware deployment pattern), AI-powered threat detection (addressing the 82% malware-free detection challenge), and incident response expertise on demand (matching the 29-minute breakout window). For SMBs especially — where 88% of breaches include ransomware (Verizon DBIR) and internal SOC teams are often impossible to staff — MDR represents the most pragmatic path to closing the gap between threat velocity and defensive capability.
Building a security-positive culture: Gartner's identification of the "death of traditional security awareness training" as a top 2026 trend carries workforce implications. With 57% of employees using personal GenAI accounts for work and 33% entering sensitive data into unapproved tools, training must evolve from periodic compliance exercises to continuous, task-based security education with AI-specific modules. Sophos's finding that only 41% of investigated incidents had MFA present, despite years of industry advocacy, demonstrates that technology deployment alone is insufficient — culture change and enforcement are equally critical.
What it means for you: The skills gap is not closing. AI-driven automation (SOAR, AI-powered detection, automated response) is the pragmatic answer for 2026. But automation needs human oversight — and those humans need AI skills. Gartner's spending data confirms the market response: security services is the fastest-growing segment ($86.1B in 2025), driven by organisations outsourcing capabilities they cannot staff internally. Investment in upskilling existing teams in AI security, cloud security, and zero trust is the highest-ROI workforce strategy.
| Finding | Value | Source |
|---|---|---|
| Unfilled cybersecurity positions | 4.8 million | ISC2 Cybersecurity Workforce Study 2025 |
| Active cybersecurity workforce | 5.5 million | ISC2 Cybersecurity Workforce Study 2024 |
| Orgs reporting moderate-to-critical skills gap | 67% | WEF Global Cybersecurity Outlook 2025 |
| Breach cost with skills shortage | $5.22M | IBM Cost of a Data Breach Report 2025 |
| Global average breach cost (comparison) | $4.44M | IBM Cost of a Data Breach Report 2025 |
| AI security as #1 skill gap | 41% | ISC2 Workforce Study 2025 |
| Cybersecurity professionals reporting burnout | 76% | Sophos Addressing Cybersecurity Burnout 2025 |
| Hiring managers citing retention difficulty | 60% | ISACA |
| SMBs without formal AI security policy | 51% | ConnectWise State of SMB Cybersecurity 2024 |
The Workforce-AI Paradox
Skills shortage adds 17.6% to breach costs ($5.22M vs $4.44M average). AI security is simultaneously the #1 skill gap (ISC2 2025) and the #1 tool reducing breach costs (IBM 2025). Organisations need AI-skilled people to deploy the AI tools that compensate for the people shortage. Until this cycle breaks, understaffed organisations will pay more per breach. (IBM Cost of a Data Breach Report 2025)
🔮 Predictions: What's Next (2026–2030)
Based on the data trends analysed across all 14 sections, here are the cybersecurity predictions 2026 and beyond that the evidence supports. These predictions draw on convergent signals from seven major research organisations: WEF, Gartner, CrowdStrike, IBM X-Force, Sophos, Mandiant/Google, and Fortinet. Where multiple sources point to the same trajectory, confidence is highest.
The convergent theme: Every major research organisation's 2026 report highlights the same fundamental shift: speed and identity have replaced sophistication and malware as the defining characteristics of modern attacks. CrowdStrike's 29-minute breakout, Sophos's 3.4-hour AD compromise, Mandiant's 48-hour zero-day windows, and Fortinet's "days to minutes" compression all point to the same conclusion — defenders who rely on human-speed response will consistently lose to machine-speed offence. The predictions below reflect this consensus.
2026: AI governance becomes a board-level requirement
With 13% of companies already reporting AI-related incidents and 97% lacking controls (IBM), the EU AI Act Phase 3 (Aug 2026) will force formal AI governance. Gartner identifies agentic AI governance as its #1 cybersecurity trend for 2026. Expect AI security budgets to double.
2026: Agentic AI attacks become mainstream
Autonomous AI agents capable of executing multi-step attack chains will emerge as a distinct threat category. IBM predicts legacy security models will "crack under pressure" from agentic AI. Fortinet predicts AI agents automating full attack chains, with breach-to-impact compressed from days to minutes. New governance frameworks for AI behaviour at machine speed are needed.
2026: Security spending hits $240 billion
Gartner projects worldwide security and risk management spending reaching $240B in 2026, up from $213B in 2025. The trajectory accelerates to $287B by 2027 (~11% CAGR). Security services represent the fastest-growing segment, driven by the skills gap. Cloud security spending alone will grow from $8.7B to $12.8B by 2027.
2027: Semi-autonomous swarm attacks emerge
Fortinet predicts deeper agentic AI will enable semi-autonomous swarm attacks by the 2027 horizon — coordinated, adaptive, machine-speed offence that overwhelms human-paced defences. 17% of all cyberattacks will involve GenAI by this point (Gartner). Machine-speed offence will require machine-speed defence.
2027: Zero trust becomes the default, not the exception
With adoption projected to reach 63% in 2026 (Gartner), zero trust will cross the adoption threshold where non-adoption becomes the outlier. ZTNA will functionally replace VPNs for enterprise remote access.
2028: CISOs own disaster recovery alongside IR
Gartner predicts that by 2028, 50% of CISOs will own disaster recovery alongside incident response — expanding the CISO remit from prevention and detection to full operational resilience. This structural shift reflects the convergence of cybersecurity with business continuity.
2028: Post-quantum migration accelerates
37% of WEF respondents already expect quantum to affect cybersecurity within 12 months. Government mandates will force PQC migration for defence, finance, and healthcare. Classical cryptography deprecation is targeted for 2030 (NIST). Organisations without crypto-agility will face expensive retrofits.
2030: Cybercrime costs exceed $15 trillion
Cybersecurity Ventures projects global cybercrime costs reaching $15.63 trillion by 2029. At that scale, cybercrime will represent approximately 10% of global GDP — making it the largest illegal economy in human history. Security spending will reach $287B+ annually (Gartner).
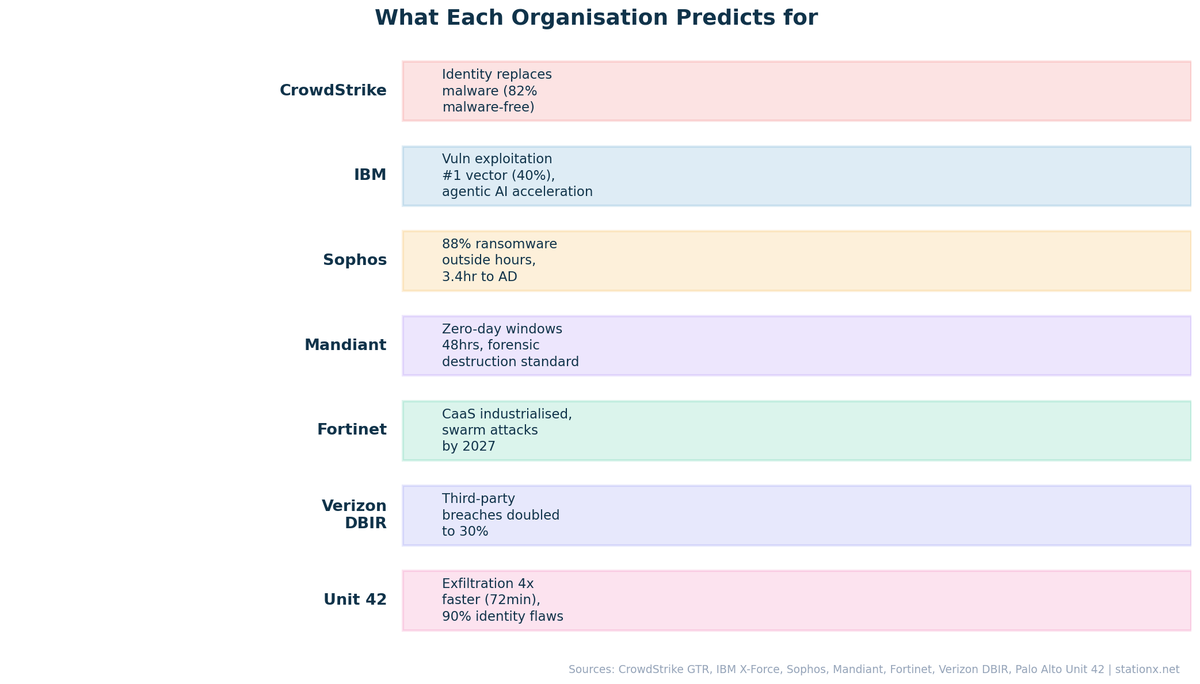
What Each Organisation Predicts for 2026–2030
Each major cybersecurity research organisation has a distinct perspective on where the threat landscape is heading. This comparison table synthesises their key predictions from reports published in late 2025 and early 2026.
| Organisation | Top Threat Focus | Key Prediction | Horizon |
|---|---|---|---|
| WEF | AI + geopolitical fragmentation | 94% identify AI as #1 driver; cyber inequity widens (84% vs 13% confidence gap) | 2026–2028 |
| Gartner | Agentic AI governance | 17% of attacks will involve GenAI by 2027; security spending reaches $287B; CISOs own DR by 2028 | 2026–2028 |
| CrowdStrike | Speed + identity + nation-state | 29-min breakout collapses detect-respond models; 82% malware-free; 266% state-nexus cloud surge | 2026 |
| IBM X-Force | Vulnerability exploitation + fragmentation | Vuln exploitation overtakes phishing (40%); 109 ransomware groups; supply chain 4x since 2020 | 2026 |
| Sophos | Identity + off-hours operations | 67% of incidents start with identity; 88% ransomware outside business hours; AD in 3.4 hours | 2026 |
| Fortinet | CaaS industrialisation + AI agents | Breach-to-impact compressed from days to minutes; semi-autonomous swarm attacks by 2027 | 2026–2027 |
| Mandiant/Google | Zero-day + CI/CD supply chain | 48-hour zero-day windows; full cloud compromise via CI/CD in 72 hours; forensic destruction standard | 2026 |
Security Spending Trajectory: $213B to $287B
Gartner's security spending forecasts show sustained double-digit growth driven by AI investment, regulatory compliance, and the skills gap fuelling demand for managed services. The segment breakdown for 2025: security software at $100.7B (15.1% growth), security services at $86.1B (fastest-growing, driven by the skills gap), network security at $24.8B (13.1% growth), and cloud security (CASB/CWPP) at $8.7B projected to reach $12.8B by 2027.
| Finding | Value | Source |
|---|---|---|
| Security spending (2025) | $213B | Gartner |
| Projected security spending (2026) | $240B | Gartner |
| Projected security spending (2027) | $287B | Gartner |
| Total cybersecurity market spending (2026) | $520B | Cybersecurity Ventures |
Gartner's Six Cybersecurity Trends for 2026
Gartner published its top six cybersecurity trends for 2026 in early 2026. These structural predictions shape enterprise security strategy and investment priorities.
1. Agentic AI Forces a Governance Reckoning
AI systems acting independently via no-code platforms create unmanaged agents, unsecured code paths, and compliance risks. Organisations must inventory and govern AI agents like human insiders — registration, credential management, and policy-based authorisation.
2. Regulatory Accountability as Executive Liability
Regulatory decentralisation elevates cyber resilience to board-level accountability. Integration with legal, procurement, and business decisions is required. Personal liability extends to individual executives under NIS2 and DORA.
3. Post-Quantum Cryptography Moves to Roadmaps
Organisations must inventory cryptographic assets and build cryptographic agility to counter "harvest now, decrypt later" attacks. Migration from theoretical planning to active roadmap implementation.
4. IAM Evolves Beyond Humans
Machine identities and AI agents require registration, credential automation, and policy-based authorisation as a control plane. Non-human identities now outnumber human identities in most enterprises.
5. AI-Driven SOCs Reshape Operations and Workforce
AI-enabled SOCs enhance triage accuracy and speed but introduce cost uncertainty, upskilling requirements, and staffing pressure. Human-in-the-loop models remain essential — AI augments, not replaces.
6. Traditional Security Awareness Training Breaks
Standard security awareness training fails amid unsanctioned GenAI tools (57% using personal accounts, 33% entering sensitive data). The replacement: adaptive, task-based programmes with AI-specific modules to curb data leakage and unsafe AI use.
Fortinet: The 2027 Horizon
Fortinet's FortiGuard Labs 2026 Predictions Report looks further ahead, identifying threats beyond the current cycle. The CaaS (Cybercrime-as-a-Service) ecosystem has industrialised attacks, with specialisation across attack stages: initial access brokers, privilege escalation specialists, and extortion operators working in concert. Breach-to-impact timelines have compressed from days to minutes. By the 2027 horizon, Fortinet predicts deeper agentic AI will enable semi-autonomous swarm attacks — coordinated, adaptive campaigns running at machine speed across multiple targets simultaneously. The defence response: machine-speed detection and containment, continuous threat exposure management (CTEM), and global collaboration through initiatives like INTERPOL cybercrime bounties.
The Trend of Trends: Convergence
The meta-trend across all ${SECTIONS.length - 2} trends is convergence. AI converges with social engineering. Supply chains converge with ransomware. Identity converges with cloud security. Regulation converges across jurisdictions. Speed converges with identity — the 29-minute breakout window collapses the distinction between initial access and full compromise. The organisations that thrive will be those with unified security strategies that address these intersections — not those with siloed teams handling each trend independently.
📋 Key Takeaways
- AI is the defining trend of 2026. 89% increase in AI-enabled attacks (CrowdStrike), 94% identify AI as #1 driver (WEF). The organisations that deploy AI with governance will win; those that deploy it without controls will create new vulnerabilities.
- The response window is shrinking. 29-minute average breakout (CrowdStrike), 27-second fastest, 48-hour zero-day exploitation windows (Mandiant). If your incident response assumes next-business-day action, it is already obsolete.
- Supply chain risk is systemic. Nearly 4x since 2020 (IBM), CI/CD identity chain compromise in 72 hours (Mandiant). Your vendor's security posture is your security posture.
- Identity has replaced the perimeter. 82% of detections are malware-free (CrowdStrike 2026), 67% of incidents start with identity (Sophos). MFA present in only 41% of cases. Phishing-resistant MFA and zero trust identity are non-negotiable.
- Ransomware is fragmenting, not declining. 109 active groups (+49%, IBM), 51 brands (Sophos), 88% deploy outside business hours. Immutable backups, 24/7 monitoring, and incident response planning are the defence.
- Cloud is a geopolitical target. +266% state-nexus cloud intrusions (CrowdStrike). Cloud security must address both criminal and espionage threats simultaneously.
- Regulation is converging. NIS2, DORA, and the EU AI Act create unprecedented compliance density. Treat compliance as a security enabler, not an overhead.
- Security spending is accelerating. $213B (2025) to $240B (2026) to $287B (2027) at ~11% CAGR (Gartner). The market is pricing in the threat escalation.
- Zero trust delivers measurable ROI. $1.76M savings per breach. The adoption trajectory (41% to 63%) shows the market agrees.
- The workforce gap is not closing. AI automation is the pragmatic answer, but it requires AI-skilled people to deploy — creating a paradox only training investment can resolve.
- Quantum is a when, not an if. 37% expect impact within 12 months (WEF). Start with a cryptographic inventory. Build for crypto-agility. CISA is already requiring PQC products in federal procurement.
❓ Cybersecurity Trends FAQ
These answers are based on data from the CrowdStrike Global Threat Report 2026, IBM X-Force Threat Intelligence Index 2026, WEF Global Cybersecurity Outlook 2026, Gartner Top Cybersecurity Trends 2026, Sophos Active Adversary Report 2026, Mandiant/Google Cloud Threat Horizons H1 2026, Fortinet FortiGuard Labs 2026 Predictions, Verizon DBIR 2025, and Palo Alto Unit 42 Global Incident Response Report 2026. All source citations are provided inline.
What are the top cybersecurity trends for 2026?
The top cybersecurity trends for 2026 are: AI-powered attacks and defence (89% increase in AI-enabled attacks), the shrinking response window (29-minute breakout time), supply chain security (4x since 2020), ransomware evolution (109 active groups), identity-first security (82% malware-free detections), cloud security gaps (+266% state-nexus intrusions), regulatory convergence (NIS2, DORA, EU AI Act), zero trust adoption, OT/ICS security, and the quantum computing threat. Each is backed by data from WEF, IBM X-Force 2026, CrowdStrike 2026, Gartner, Sophos, Mandiant, and Fortinet.
How is AI changing cybersecurity in 2026?
AI-enabled attacks increased 89% year-over-year (CrowdStrike 2026), and 94% of leaders identify AI as the most significant driver of cybersecurity change (WEF 2026). On offence, AI phishing costs 95% less (HBR 2024). On defence, AI/automation saves $1.9M per breach (IBM 2025). The key challenge is the governance gap: 57% of workers use unapproved GenAI tools, 33% enter sensitive data, and data leaks from GenAI (34%) now lead over adversarial capabilities (29%) as the top AI concern (WEF 2026). Gartner projects 17% of all cyberattacks will involve GenAI by 2027.
How fast can attackers move once inside a network?
The average eCrime breakout time has crashed to 29 minutes (CrowdStrike 2026), with the fastest observed at 27 seconds. Zero-day exploitation windows have collapsed to 48 hours (Mandiant). Attackers reach Active Directory in 3.4 hours post-breach (Sophos 2026). 88% of ransomware is deployed outside business hours. This speed collapses traditional detect-and-respond models and demands automated, machine-speed detection and containment.
What is the biggest cybersecurity threat in 2026?
Identity-based attacks represent the biggest tactical shift, with 82% of detections now malware-free (CrowdStrike 2026) and 67% of incidents starting with identity compromise (Sophos 2026). The systemic threat is supply chain compromise, which has grown nearly 4x since 2020 (IBM X-Force 2026). The speed threat is equally critical: 29-minute breakout times collapse the response window to minutes.
Is ransomware still a major threat in 2026?
Yes. Ransomware appears in 44% of all breaches (Verizon DBIR 2025). IBM X-Force 2026 tracked a 49% increase in active ransomware groups (109 total). Sophos observed 51 ransomware brands. 88% of ransomware deploys outside business hours, and attackers reach Active Directory in 3.4 hours. 64% of organisations now refuse to pay, and recovery costs ($2.73M average) far exceed the median ransom payment ($115K). SMBs are disproportionately affected: 88% of SMB breaches include ransomware vs 39% for large organisations.
How much is the world spending on cybersecurity?
Gartner projects worldwide security and risk management spending at $213B in 2025, rising to $240B in 2026 and $287B by 2027 (~11% CAGR). Security services is the fastest-growing segment, driven by the skills gap. Cloud security spending is projected to grow from $8.7B to $12.8B by 2027. The spending trajectory reflects both threat escalation and regulatory compliance pressure.
What is zero trust and why does it matter?
Zero trust is a security framework that assumes no user, device, or network is trusted by default. It requires continuous verification, least-privilege access, and micro-segmentation. Zero trust reduces breach costs by $1.76M (IBM 2025), and adoption is projected to reach 63% of enterprises in 2026 (Gartner). With 82% of detections malware-free and 29-minute breakout times, zero trust's assume-breach posture directly addresses the speed and identity gaps.
What regulations affect cybersecurity in 2026?
Three major EU frameworks are now active or phasing in: NIS2 (network security, Oct 2024), DORA (financial resilience, Jan 2025), and the EU AI Act (phased 2024-2026). DORA's 4-hour incident reporting deadline makes manual compliance impossible. NIS2 and DORA both impose personal executive liability. GDPR enforcement hit a record €2.1B in fines in 2025. Combined with 162 countries with data protection laws, this represents the most complex regulatory environment in cybersecurity history.
How are nation-state actors changing the cybersecurity landscape?
Cloud intrusions from state-nexus actors surged 266% (CrowdStrike 2026). China-nexus intrusions rose 38%, with 40% targeting edge devices for espionage. DPRK-nexus incidents increased 130%, including the $1.46 billion cryptocurrency theft. Russia deployed LLM-enabled malware for automated reconnaissance. 91% of the largest organisations have altered cybersecurity strategies due to geopolitical volatility (WEF 2026). The lines between nation-state espionage and financially motivated cybercrime are blurring.
What is Cybercrime-as-a-Service (CaaS)?
Fortinet reports that cybercrime has industrialised into a Cybercrime-as-a-Service model, emphasising speed and throughput over technical innovation. Specialised providers offer tools for each attack stage: initial access, privilege escalation, lateral movement, and data exfiltration. This lowers the skill barrier, enabling less sophisticated actors to run advanced operations. The result: more attackers, faster attacks, and a ransomware ecosystem with 109 active groups (IBM 2026) and 51 distinct brands (Sophos 2026).
When will quantum computing threaten current encryption?
The Global Risk Institute estimates a 33% probability of quantum computers breaking RSA-2048 by 2034. 37% of WEF respondents believe quantum will affect cybersecurity within 12 months. NIST finalized 3 PQC standards in August 2024, with a fourth (HQC) selected in March 2025. NIST recommends classical cryptography deprecation by 2030, and the NSA mandates pure PQC for national security systems by 2035. CISA's January 2026 procurement guidance already requires quantum-resistant products.
About This Data
This article draws from 1472 statistics aggregated from 50+ authoritative sources including IBM Cost of a Data Breach, Verizon DBIR, CrowdStrike Global Threat Report, WEF Global Cybersecurity Outlook, FBI IC3, ISC2 Cybersecurity Workforce Study, Sophos, Gartner, Mandiant M-Trends, and Ponemon Institute reports.
Derived statistics (marked "Nathan House's Analysis") are computed by cross-referencing data from multiple sources — for example, comparing breach costs across industries using IBM data, or validating ransomware trends across Verizon, Sophos, and HIPAA Journal findings.
All statistics include inline source citations with links to primary sources. Data spans 2023-2026, with preference given to the most recent available figures. Last updated: May 2026.
How to Use This Data
Security professionals can use these cybersecurity trends and supporting data to build board-level presentations, justify security investment, and benchmark organisational readiness against each trend. The interactive Trend Impact Assessment tool above can help you prioritise which trends matter most for your specific context.
For CISOs building board presentations: The data points most relevant to executive audiences are the spending trajectory ($213B to $287B, Gartner), the breakout speed compression (29 minutes average, CrowdStrike), the identity compromise dominance (67% of incidents, Sophos), and the regulatory liability landscape (personal executive liability under NIS2 and DORA). The organisation comparison table in the Predictions section provides a cross-vendor consensus view suitable for strategic planning.
For security teams benchmarking readiness: Key benchmarks to assess your position: Do you have 24/7 monitoring coverage? (88% of ransomware deploys outside business hours.) Is MFA deployed universally? (Present in only 41% of investigated cases.) Can you detect and contain within 29 minutes? (Average eCrime breakout time.) Have you inventoried machine identities alongside human users? (IAM beyond humans is a top Gartner trend.) Is your CI/CD pipeline audited for trust relationship abuse? (Mandiant documented full cloud compromise in 72 hours via this vector.)
This page is updated as new data emerges. Sources include CrowdStrike Global Threat Report 2026, IBM X-Force Threat Intelligence Index 2026, WEF Global Cybersecurity Outlook 2026, Gartner Top Cybersecurity Trends 2026, Sophos Active Adversary Report 2026, Mandiant/Google Cloud Threat Horizons H1 2026, Fortinet FortiGuard Labs 2026 Predictions, and Verizon DBIR 2025. Bookmark it and return for the latest cybersecurity trends and cybersecurity predictions. If you spot an outdated statistic or want to suggest a source, contact us.
About the Author

Nathan House, StationX
Nathan House is a cybersecurity expert with 30 years of hands-on experience. He holds OSCP, CISSP, and CEH certifications, has secured £71 billion in UK mobile banking transactions, and has worked with clients including Microsoft, Cisco, BP, Vodafone, and VISA. Named Cyber Security Educator of the Year 2020 and a UK Top 25 Security Influencer 2025, Nathan is a featured expert on CNN, Fox News, and NBC. He founded StationX, which has trained over 500,000 students in cybersecurity.
